PRODUCT: IDENTITY GUARDIANS
Automate Credential Remediation
Across Your Directory Services
SpyCloud Identity Guardians integrate with Active Directory, Entra ID, and Okta Workforce to automatically detect and remediate compromised session cookies and credentials. Prevent authentication bypass, account takeover, and improve password hygiene across your entire workforce with less lift.
Turn darknet data into automated directory defense
SpyCloud Identity Guardians empower Identity and Access Management (IAM) teams to prevent identity threats by acting on malware, phishing, combolists, and breached session cookie and credential exposures before criminals can. Instead of relying on outdated password policies or manual resets, Identity Guardians deliver continuous monitoring and automated remediation of verified credential exposures – aligned with NIST 800-63B and Zero Trust principles.
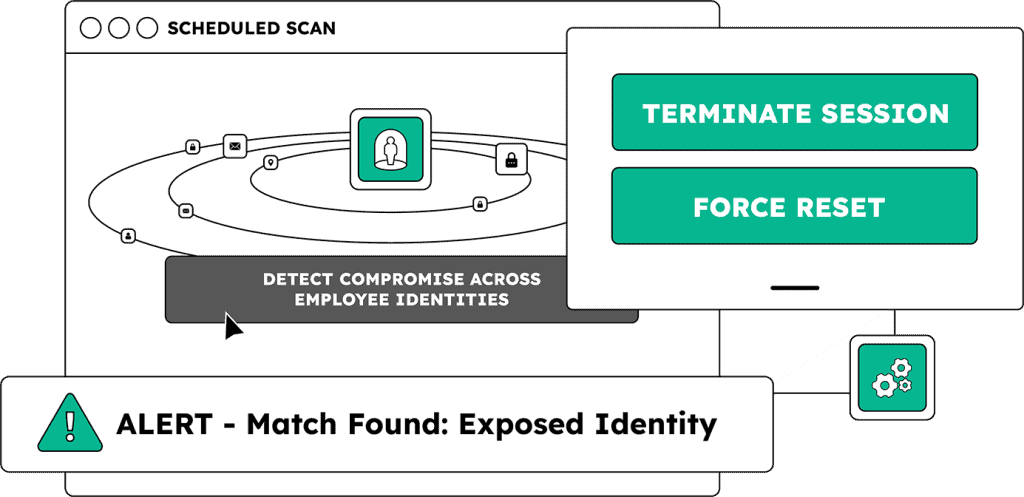
Scheduled scanning detects workforce credential exposures day or night, without manual intervention
Eliminate blindspots from dark web exposures by terminating sessions and resetting passwords instantly – including those tied to employees’ past or personal identities
Extend protection to contractors and third parties to ensure secure, compliant access across environments
EXPLORE PRODUCTS
SpyCloud integrates where identity hygiene happens
Whether you manage on-prem directories or cloud-based identities, Identity Guardians plug into your environment with minimal setup – enabling real-time credential remediation without slowing down operations.
Automate credential resets or disable high-risk accounts – acting on malware exposures in as little as 5 minutes from discovery

Extend automated credential protection to Microsoft’s cloud-based directory services
Integrate with Okta Workforce to automatically terminate sessions, enforce password resets, trigger downstream workflows, change user groups, and more
Know more with
IDLink analytics
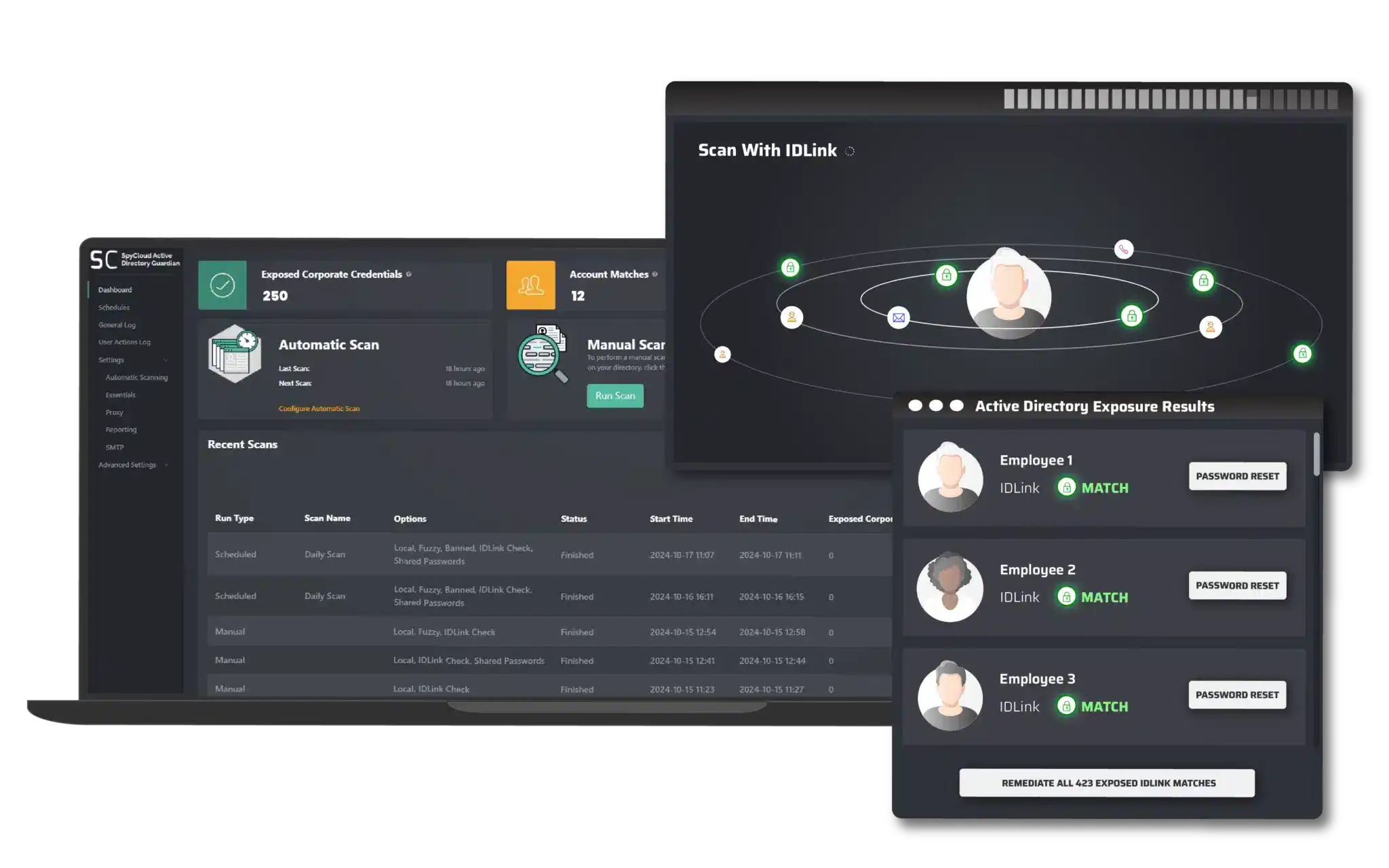
Find up to 14x more passwords per user
Scan with IDLink for even more powerful coverage of exposed Active Directory accounts. Find all exposed credentials tied to your employees’ holistic identities, some of which are likely outside your monitoring visibility.
Using SpyCloud helps us break into the cycle of identity access brokers and remediate compromised accounts before they are used against us. The Active Directory Guardian platform has also enabled us to enforce and maintain excellent account hygiene of our clients.
EXPLORE MORE PRODUCTS
Up-level your identity threat defense
Workforce Threat Protection
Prevent session hijacking and account takeover attempts by acting on exposed employee identities
Endpoint Threat Protection
Remediate malware-exposed users, devices, and applications to prevent ransomware and other identity attacks
Next steps
Protect your directory. Preserve your sanity.
Get a demo with our team today.
Compromised Credential Remediation FAQs
Native IdP tools operate exclusively on internal signals. Okta ThreatInsight detects anomalous login patterns and known-bad IP addresses within the Okta environment. Azure AD Password Protection blocks weak and commonly used passwords at the point of password creation. Neither tool has visibility into credentials that were stolen outside the corporate environment and are now circulating in criminal markets. When an employee’s personal device is infected by infostealer malware and their work credentials are exfiltrated, that theft does not generate any signal inside Okta or Azure AD. The stolen credentials simply exist in criminal markets, ready to be tested against the corporate login portal, with no alert generated until a login attempt occurs or an account is compromised. SpyCloud Identity Guardians monitor against SpyCloud’s recaptured darknet dataset — breach records, infostealer malware logs, and phishing data sourced directly from criminal infrastructure — which is where those stolen credentials actually exist. IDLink analytics extend that monitoring to personal identity footprints, finding credentials that were exposed through personal accounts with the same password as the work account. The result is 14 times more plaintext passwords found per user compared to exact-match monitoring against the corporate domain alone.
NIST Special Publication 800-63B Section 5.1.1.2 requires that organizations verify that user-selected passwords are not present in a “frequently changed list” of compromised credentials, including passwords obtained from previous breach corpuses, dictionary words, repetitive or sequential characters, and context-specific words. The standard requires continuous monitoring against this list, not periodic audits, and requires that users be prompted to choose a different credential when a match is found. SpyCloud Identity Guardians satisfy each element of this requirement. The SpyCloud darknet dataset is continuously updated as new breach records, infostealer logs, and phishing captures are processed — typically within days of new data appearing in criminal markets. Identity Guardians check employee credentials against this dataset on a configurable continuous or scheduled basis, automatically trigger forced password resets when a match is found, and generate audit logs suitable for NIST 800-63B assessment documentation. SpyCloud also provides exportable compliance documentation for SOC 2 Type II evidence packages and federal procurement reviews. Native IdP tools — quarterly manual audits, periodic pen test reports, and annual access reviews — do not satisfy the continuous monitoring requirement. SpyCloud does.
The three Identity Guardians serve the same core purpose — continuously monitoring employee credentials against SpyCloud’s recaptured darknet data and automatically triggering remediation — but they integrate into different identity environments. Active Directory Guardian runs locally on an Active Directory member server or domain controller. It is designed for organizations with on-premises AD deployments and uses native Microsoft calls to replicate user data and NTLM hashes for credential verification. It can trigger password resets via AD directly or via the Okta API for hybrid environments where Okta serves as the authentication layer on top of AD. Entra ID Guardian runs in an Azure container and supports cloud-native and hybrid Entra ID deployments. It is agentless and integrates with Microsoft Defender and Sentinel for organizations already using the Microsoft security stack. Okta Workforce Guardian integrates directly with the Okta Workflows engine and supports the full range of Okta remediation actions: enforcing password resets, revoking active sessions, disabling high-risk accounts, and changing user groups to trigger adaptive authentication policies. For organizations with a hybrid or multi-directory environment, the Guardians can operate in parallel — Active Directory Guardian or Entra ID Guardian handles the directory layer while Okta Workforce Guardian handles the authentication and session layer.
Standard directory scanning checks whether an employee’s current work password appears in a breach record that exposed their work email address. It misses the most common ATO entry point: an employee who uses the same password for a personal account that was breached. The breach exposed a personal email address, not the work one, so the exact-match scan returns nothing. The employee’s work account has effectively the same password as a compromised credential, but the exposure is invisible to the corporate security team. Identity Guardians with IDLink analytics enabled address this directly. IDLink automatically correlates the employee’s work identity against their personal identity footprint — personal email addresses, backup accounts, historical usernames, and other identity artifacts found in SpyCloud’s recaptured dataset. When IDLink finds that a personal account associated with the employee was compromised with a password that matches the employee’s current work account password, it flags the exposure and triggers a forced reset through Active Directory, Okta, or Entra ID. This is what produces the 14x difference in passwords found compared to exact-match scanning. The attack path that most ATO incidents follow — compromise of a personal account, reuse of that password at work — is precisely what IDLink-enabled scanning catches and exact-match scanning misses.
SpyCloud’s darknet database is updated continuously as new breach records, infostealer malware logs, and phishing data are recaptured from criminal sources. New data typically appears in SpyCloud’s corpus within days of surfacing in criminal markets — often before it reaches publicly indexed sources. Identity Guardians run automatic scans that check newly published SpyCloud data against monitored employee identities as it arrives. When a match is confirmed, the remediation action configured in the policy — password reset, account disable, or session revocation — triggers automatically without manual intervention. The window from detection to completed remediation is under five minutes for standard deployments. For SSO environments where Okta Workforce Guardian is deployed, session revocation is immediate and cascades to every downstream application in the SSO instance. The operational significance is that the exposure window — the time between when a criminal acquires the stolen credential and when the organization can act on it — is compressed to hours rather than weeks. Without continuous automated monitoring, that window is typically measured in months: credentials are compromised, circulate in criminal markets, and are tested against corporate login portals before the organization has any indication the exposure exists.