USE CASE: RANSOMWARE PREVENTION
Disrupt the Ransomware Attack Chain
with Identity Threat Protection
Ransomware doesn’t begin with file encryption – it begins with compromised identities. SpyCloud stops ransomware before it starts by detecting and remediating exposed credentials, session cookies, and personal data that adversaries use to gain a foothold.
Whether the exposure results from malware, phishing, or a third-party breach, reclaiming control over exposed data means you can cut off initial access, stop lateral movement, and prevent escalation – keeping your organization one step ahead.
Take down ransomware risk at the root
The key to preventing ransomware is to detect and remediate loss of access.
Ransomware attacks often stem from phishing attacks or infostealer infections. Security professionals report that phishing is the most common entry point in ransomware attacks, and recent research found that one-third of ransomware events were preceded by a stealer infection in the previous 16 weeks.
By remediating exposed access early, you can prevent phishing and malware from escalating into a full-blown ransomware attack.
Uncover user identities targeted by phishing and infostealer malware
Stop attackers from using stolen authentication data to move laterally or escalate privileges
Integrate actionable identity insights into your workflows to shrink dwell time and minimize ransomware risk
EXPLORE PRODUCTS
SpyCloud’s identity intelligence is your ransomware early warning signal. Cut off initial access by remediating exposed identity data and malware-compromised apps.
Neutralize malware threats before they escalate into costly ransomware incidents
Stop cybercriminals from using stolen credentials to take over accounts and escalate ransomware campaigns
Protect session cookies that attackers use to bypass MFA and gain initial access
Whenever we get an alert from [SpyCloud] we always follow it up as it is always fresh intel. Using SpyCloud helps us break into the cycle of identity access brokers and remediate compromised accounts before they are used against us.
EXPLORE WHO USES SPYCLOUD
Defenders
we help
Integrations





Next steps
Ransomware Prevention FAQs
Ransomware attacks begin with stolen identity data. The most common kill chain starts when infostealer malware captures credentials and session cookies from an employee device, those artifacts are distributed through criminal markets, ransomware operators purchase them, and use the stolen credentials to authenticate into the corporate environment and deploy ransomware. Nearly one in three companies that suffered a ransomware attack had a prior infostealer infection on record. In 2025, 85% of organizations reported being hit by ransomware, with phishing accounting for 35% of initial access vectors, up from 25% in 2024.
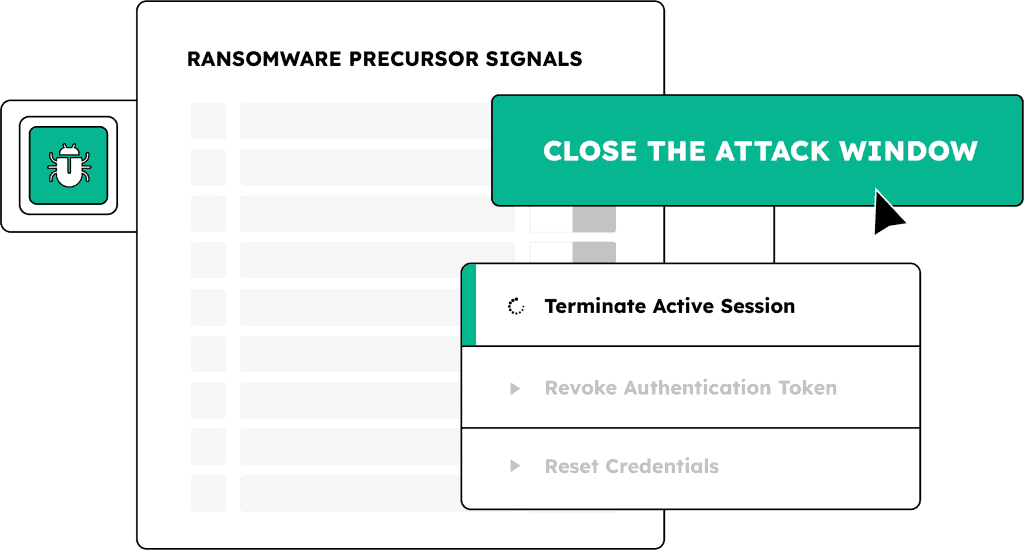
SpyCloud intervenes at the earliest possible point: the credential and session exposure window that precedes any attacker action inside the organization. When SpyCloud recaptures a malware log or phished credential set tied to a customer’s domain, it surfaces the exposure within hours of that data appearing in criminal markets. This is the window between when an attacker acquires the stolen credential and when they test it against the corporate login portal. SpyCloud triggers automated password resets through Identity Guardians and session revocations through Okta Workforce Guardian, Active Directory Guardian, and Entra ID Guardian, removing the attacker’s access path before initial access is established.
Ransomware operators and access brokers increasingly rely on infostealer malware as their primary sourcing mechanism for initial access credentials. Infostealer infections are cheap to deploy at scale, produce high-value credential and session data, and operate silently without triggering EDR or antivirus alerts in 40% of cases. When a ransomware operator purchases a malware log from a criminal market, they receive not just credentials but also the device fingerprint, application access list, and session cookies needed to authenticate as the infected employee, making the initial access attempt look like a legitimate login.
EDR tools detect malicious activity on managed endpoints and can contain active infections. They have no visibility into what happens after data leaves the device: the criminal market transaction, the credential acquisition by a ransomware operator, or the targeting that follows. SpyCloud operates on the criminal side of this gap, recapturing stolen artifacts from the same criminal infrastructure that ransomware operators use to source initial access. When a credential appears in a criminal market before a ransomware operator acts on it, SpyCloud can surface it and trigger remediation before the operator is inside the environment.
At the credential exposure stage, Workforce Threat Protection continuously monitors employee credentials against recaptured breach, malware, and phishing data, surfacing new exposures within hours of criminal market publication. At the malware infection stage, Endpoint Threat Protection recaptures infostealer malware logs and maps the full device-level exfiltration inventory including credential counts, cookie counts, and affected application lists. At the session and access stage, Session Identity Protection and Identity Guardians revoke stolen session artifacts and force password resets through Okta, Entra ID, and Active Directory within minutes of a confirmed exposure.