USE CASE: POST-INFECTION MALWARE REMEDIATION
Neutralize INFOSTEALER Malware Threats
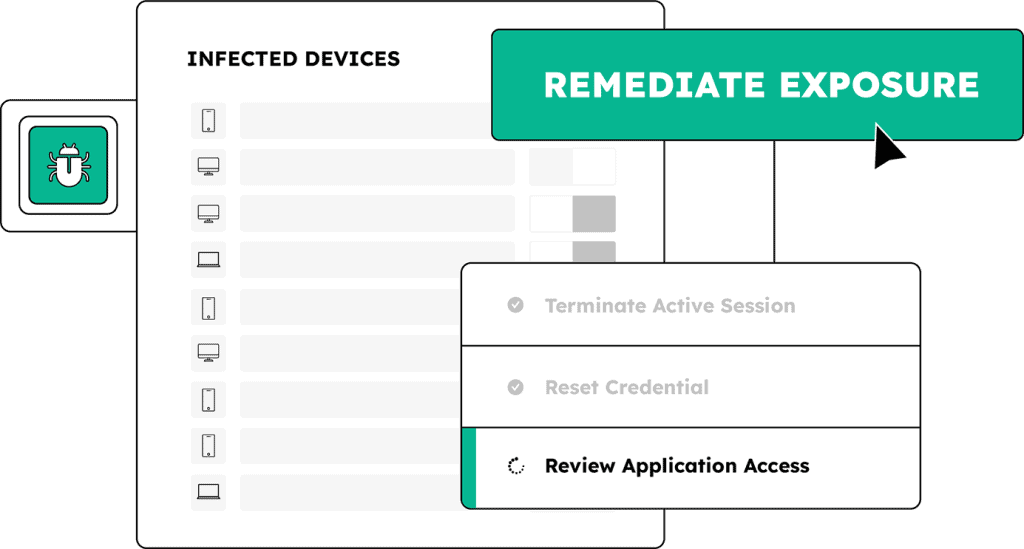
Reimaging an infected device isn’t enough. Infostealer malware captures credentials and session cookies, giving attackers access to your systems. SpyCloud shows you exactly what was stolen from infected devices and enables automated remediation steps to revoke access, reset application credentials, and invalidate session cookies to eliminate post-infection risk.
A more complete malware response workflow with SpyCloud
SpyCloud helps SOC and IR teams uncover the full impact of infostealer infections, even on unmanaged devices like contractors’ laptops. With SpyCloud’s comprehensive exposure data, you can act quickly and decisively to shut down every entry point to reduce ransomware risk and streamline response.
EXPLORE MORE PRODUCTS
Illuminate the infection – and erase the exposure with SpyCloud
EXPLORE WHO USES SPYCLOUD
Defenders
we help
CISOs
Enhance resilience to malware-based threats without expanding headcount or overhauling infrastructure
Integrations





Next steps
Turn infected devices into dead ends for attackers
Post-Infection Remediation FAQs
Infostealer malware exfiltrates far more than passwords. A single infection typically captures every credential stored in the browser across all profiles, active session cookies for every application the user was logged into, device fingerprint information, and PII. A forced password reset addresses only the credential portion. Session cookies stolen in the same infection remain valid and usable by an attacker until they expire or are explicitly revoked. SpyCloud Endpoint Threat Protection surfaces the full inventory of what was exfiltrated from each infected device including cookie counts, PII, and credential scope across every application accessed from that device.
SpyCloud does not rely on device agents or EDR telemetry. It recaptures infostealer malware logs directly from criminal communities where those logs are distributed and traded. Because SpyCloud’s data comes from the criminal underground rather than device monitoring, it surfaces infections on any device whose stolen artifacts appear in those logs, regardless of whether the device had an EDR agent installed. In 2025, 40% of infostealer infections recorded by SpyCloud occurred on devices that had EDR or antivirus tools installed. The gap is structural, not a configuration problem.
SpyCloud surfaces device-level intelligence from each infection including the full list of credentials exfiltrated across every browser profile and application, a count of session cookies stolen alongside those credentials, PII captured by the malware, the malware family responsible, and the infection path and target URLs. The session cookie count is the key triage signal: a device with a high cookie count indicates a broader compromise footprint requiring full device investigation and session revocation across all affected applications. A single malware infection can expose access to an average of 26 business applications.
Infostealer malware is the most common precursor to ransomware deployment. The attack chain runs from infection to credential and cookie exfiltration, to criminal market distribution, to ransomware operator acquisition and exploitation, to lateral movement, to deployment. Nearly one in three companies that suffered a ransomware attack had a prior infostealer infection on record. SpyCloud interrupts this chain by recapturing malware logs from criminal sources in the window between exfiltration and exploitation, giving security teams time to reset stolen credentials, revoke compromised sessions, and close access paths before an attacker acts.
EDR tools detect and contain active malware on managed devices. They alert when suspicious behavior occurs on enrolled endpoints and can quarantine infected systems. What they cannot do is surface the full inventory of what was exfiltrated before detection, cover infections on BYOD and unmanaged endpoints, or provide the credential and session artifact data needed to revoke stolen access across all affected applications. SpyCloud’s post-infection remediation closes the gap EDR leaves open: it tells security teams what was stolen, from which device, across which applications, enabling a complete response that matches the actual scope of the compromise rather than just the device-level containment step.