PRODUCT: VIP GUARDIAN
Protect VIPs from Identity-Based Attacks
Without Invading Their Privacy
SpyCloud VIP Guardian extends employee account takeover prevention to key executives’ personal accounts for an added layer of protection, without invading their privacy – giving VIPs visibility into their exposed credentials and empowering them to protect their digital identities.
Privacy-first identity monitoring for high-value users
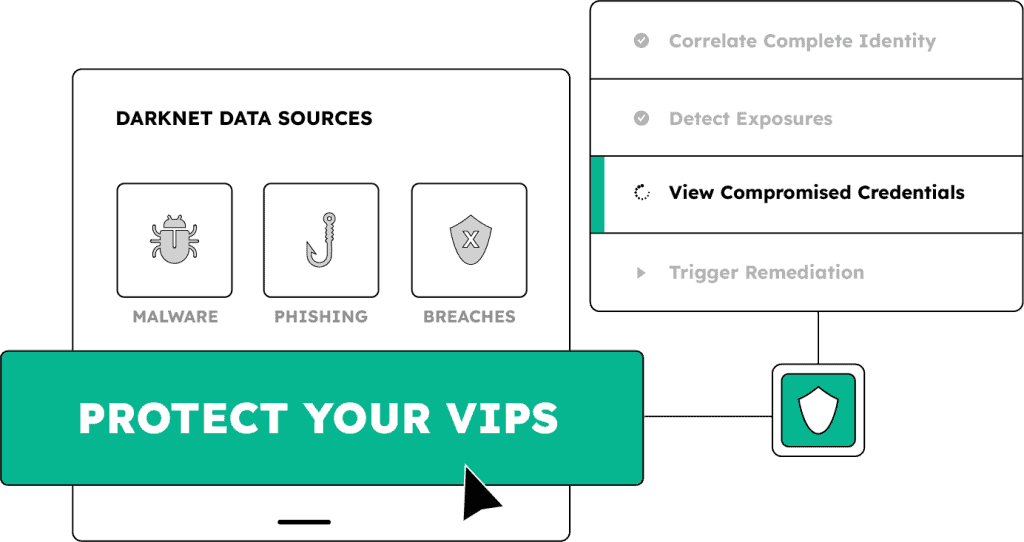
VIP Guardian continuously monitors for identity exposures tied to executives’ personal accounts – including credentials compromised in data breaches, malware infections, or successful phishing attacks – and delivers visibility directly to them, not your SOC.
Use SpyCloud’s recaptured darknet data to track exposures across multiple email addresses for each VIP, including personal, legacy, and family-linked email addresses that often go unchecked
Reduce helpdesk involvement by giving VIPs guided dashboard access to take secure, appropriate remediation steps based on the type of exposure
Enable SSO-based enrollment and privacy-preserving visibility – so your team gets signals and your VIPs get ownership, without friction or overreach
EXPLORE OTHER PRODUCTS
Protect more than your VIPs
Extend identity threat protection across your workforce with early exposure detection and automated remediation.
Workforce Threat Protection
Endpoint Threat Protection
Next steps
Protect your most targeted people – before they become your biggest risk.
Get a demo today.
Executive Identity Protection FAQs
Executives and board members have a combination of attributes that make them priority targets for attackers. They have privileged access to financial systems, approval authority for wire transfers, access to sensitive strategic information, and the organizational trust needed to authorize actions that lower-level employees cannot. Their personal accounts are frequently used to communicate about business matters, and attackers who compromise a personal email account can monitor those communications, intercept deal-related correspondence, and conduct business email compromise operations that are far more convincing than generic phishing. Personal accounts also tend to have weaker credential hygiene than corporate accounts — executives are less likely to follow corporate password policies on personal email, social, and financial accounts. A compromised personal account that shares a password variation with a corporate account, or that is used to reset a corporate account, can serve as a direct entry point into the corporate environment. SpyCloud VIP Guardian addresses this by monitoring executive personal accounts against the same recaptured breach, malware, and phishing data SpyCloud uses for corporate workforce protection, surfacing exposures across personal and professional identity footprints before attackers can weaponize them.
VIP Guardian operates on a split-visibility architecture specifically designed to address the privacy concern that makes executive protection programs difficult to implement. The executive enrolls through an SSO-based invitation and then adds their personal email addresses to their own private portal. Those personal email addresses are visible only to the executive, not to the employer or the security team. When SpyCloud detects that one of those personal accounts has appeared in a breach record, infostealer malware log, or phishing dataset, the exposure details are delivered to the executive through their private portal and via email alert. The security team receives a risk signal indicating that the executive has an active exposure requiring attention, but does not see which personal email address was affected or what the specific breach data contains. This architecture lets the security team track whether executives have remediating outstanding exposures and measure VIP protection program effectiveness without gaining surveillance capability over executives’ personal digital lives. The executive retains ownership of their personal data; the security team gets the protection signal without the privacy overreach that has historically made executive monitoring programs a political and HR challenge to deploy.
VIP Guardian monitors up to ten personal email addresses per executive, including current personal accounts, legacy accounts from previous employers, backup addresses, and email addresses associated with family members. The scope matters because attackers frequently research executive targets before launching BEC or spearphishing campaigns, and that research often surfaces personal accounts that executives have used for years. A Gmail address an executive used in 2015 may have been breached multiple times and still share password patterns with current accounts. SpyCloud monitors against its full recaptured dataset, which includes over ten years of breach records, infostealer malware logs, and phishing captures. New exposures are surfaced as they appear in criminal markets. Historical exposures already in SpyCloud’s corpus are visible from the moment the executive enrolls, giving them immediate visibility into accumulated risk they may not have been aware of before enrollment. Coverage spans all three primary exposure sources: third-party breaches where the executive registered with a personal email, infostealer malware infections that exfiltrated browser-stored credentials from a personal or family device, and successful phishing attacks that captured personal account credentials.
The connection from a compromised personal account to organizational impact follows several documented attack paths. In the most common pattern, the attacker uses the personal email to reset access to corporate services that the executive linked to their personal address as a recovery option. In the BEC pattern, the attacker monitors the personal inbox to understand ongoing business deals, then impersonates the executive or a counterparty to redirect payments or intercept contracts. If the personal account password is similar to or the same as a corporate account password, credential stuffing against the corporate login portal becomes viable. In all of these cases, the window between when the personal credential is compromised and when the attacker uses it is the only window for intervention. When VIP Guardian surfaces a personal account exposure, the executive receives specific guidance in their portal on the remediation steps for that exposure type: changing the compromised password across all accounts where it was reused, enabling two-factor authentication on the affected account, and reviewing account recovery options for any linked corporate services. The security team receives the signal that a high-priority remediation is in progress without needing to manage the details of the executive’s personal account.
Executive digital risk protection services like those offered by 360 Privacy, Chainalysis, or similar vendors provide a broader scope of executive protection: personal information removal from data broker sites, social media monitoring, physical address suppression, and in some cases managed services with human analysts. SpyCloud VIP Guardian occupies a specific, complementary lane: darknet credential exposure monitoring for executive personal accounts, built on SpyCloud’s recaptured identity dataset. It is purpose-built to detect when executive credentials have been stolen and are circulating in criminal markets, and to deliver that signal in a privacy-preserving way that integrates with the corporate SpyCloud deployment. The 360 Privacy case study on SpyCloud’s website illustrates the natural pairing: 360 Privacy uses SpyCloud’s recaptured darknet data as the intelligence foundation for their executive protection service because SpyCloud’s data arrives earlier from criminal sources than what surface-level monitoring can detect. Organizations that want self-managed, corporate-integrated credential monitoring for their executive population should use VIP Guardian directly. Organizations that want a fully managed executive protection program — including physical privacy, social monitoring, and analyst support alongside credential monitoring — should evaluate whether a managed service that uses SpyCloud data as its intelligence layer fits their program requirements.