Supply Chain Exposure Response Guide
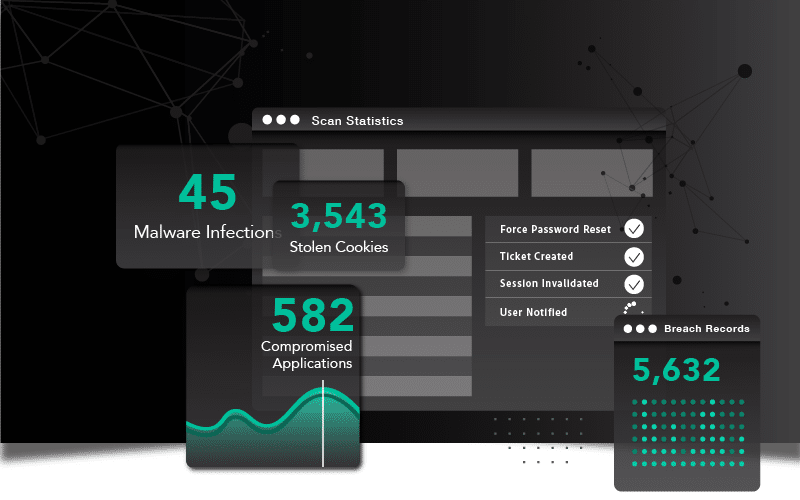
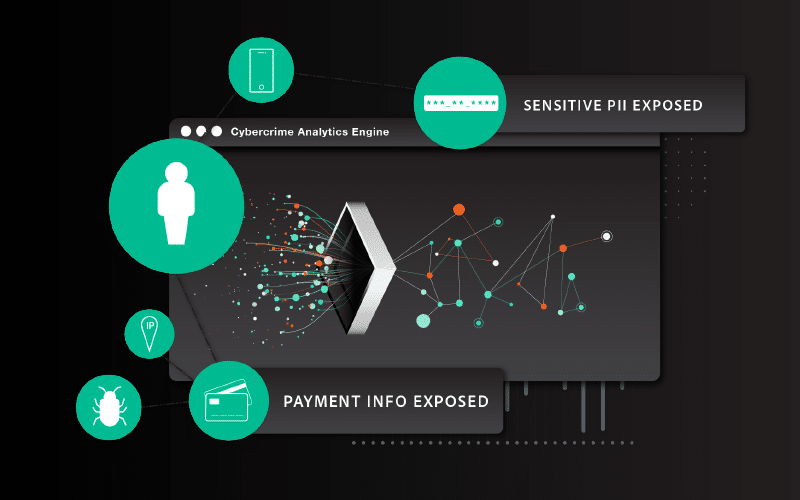
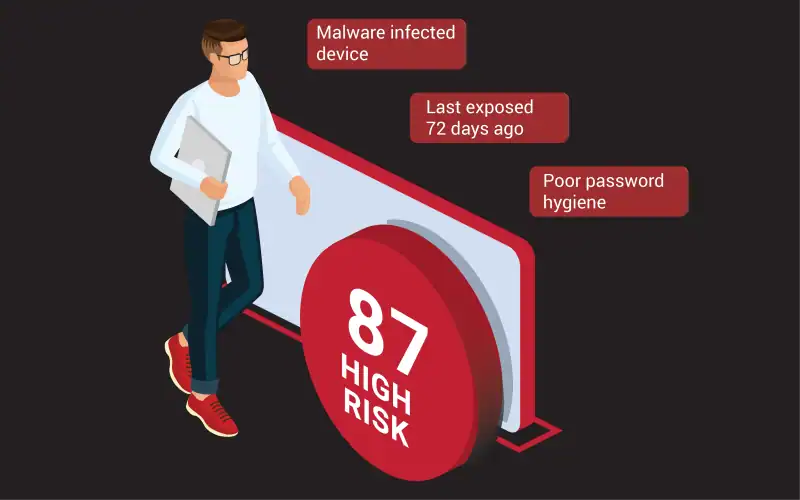
Your vendors’ compromised credentials are your problem too. This guide walks security teams through how to interpret exposed identity signals across your supply chain – malware infections, phishing exposures, password reuse, combolists – and respond with evidence-based action before an incident occurs.