You’ve probably heard about infostealers or information-stealing malware by now. It can take the form of trojans, viruses, and botnets, but there’s levels to this stuff – and it’s all much more insidious than you might think.
I grew up a Windows kid in the 80s, before the internet was really a thing. As you can imagine, if you wanted to download software or send someone a message, your options were extremely limited (back then, magazines included articles with pages of BASIC code you could type in hopefully without error – thus downloading was preferred!). Sure, CompuServe and Prodigy were around, but they were terribly expensive, so many of us were stuck using a modem to dial up Bulletin Board Systems (BBSs).
And with downloading software came the potential threat of infecting your personal computer with a virus. But the world was different back then. By today’s standards, computer viruses in the 80s were simply a nuisance. Today, bad actors infect your computer with the worst of intentions – specifically, cybercriminals are looking to monetize your data, including the data you use to authenticate into websites and apps.
With that in mind, this article focuses on the most nefarious of infostealer malware – botnets – and how to protect yourself and your organization from related malicious activity.
What are botnets?
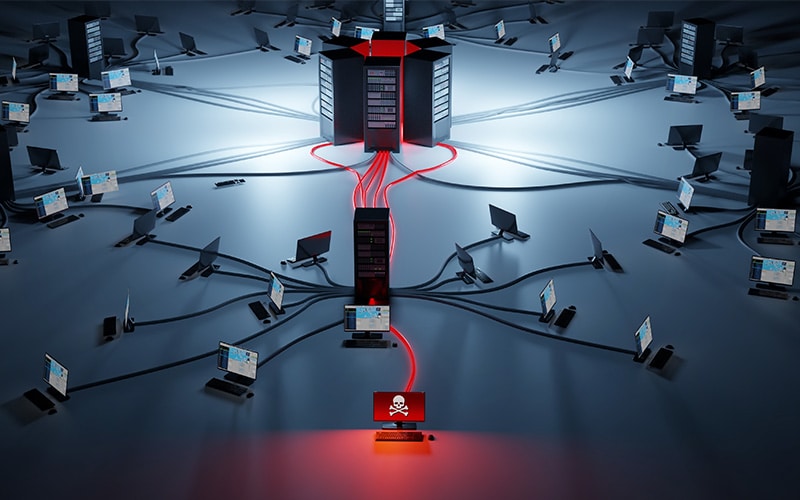
Built on the client/server model, botnets (short for “robot network”) are networks of computers infected by malware that are under the control of a single threat actor known as the “bot-herder.” The bot-herder relies on a Command & Control Server (C2) to administrate the bots, and since the infected computers are under the control of the C2, a botnet infection is like having a malicious hacker inside your network.
When used by cybercriminals, botnets are especially useful for carrying out large-scale attacks systematically.
How do botnets work?
A Distributed Denial of Service (DDoS) attack is a traditional botnet attack example. Botnets were originally used to carry out DDoS attacks or propagate spam. As they matured, some botnet infections evolved to include keyloggers to record your keystrokes, allowing bad actors to capture the usernames and passwords that you use to log into your favorite services like email, streaming services, financial institutions, and social media.
The botnets of today are much more sophisticated. A botnet attack is typically delivered in the form of a trojan – as an email attachment or maliciously embedded in software that you might download. And while antivirus software might provide some protection, oftentimes the botnet delivery methods are sophisticated enough to evade detection even by the best antivirus software.
Once botnet malware is installed, it steals information from your computer, including:
- Usernames and passwords
- Passkeys
- Hostnames from browsers & FTP clients
- Browser cookies / tokens
- Autofill data
- Crypto wallet addresses
- Files with specific extensions
- Screenshots of the desktop
- Chat history
- List of installed programs and running processes
- Machine globally unique identifier (GUID) as well system architecture, system language, username and computer name
An emerging threat: botnets unlock the door for session hijacking
Another insidious aspect of infostealer malware is session cookie theft. Criminals are diversifying their tactics by leveraging botnets to steal cookies for already-authenticated sessions to then hijack active user sessions.
Stolen session cookie data can even be used to bypass all forms of authentication, including multi-factor authentication and even passkeys. While user identifiers (email addresses, usernames, phone numbers, etc.) and passwords remain the most popular targets of information stealing malware, the proliferation of multi-factor authentication and SSO has reduced the effectiveness of stolen credentials for cybercriminals. With that in mind, bad actors have added session cookie theft to their repertoire as a form of accessing accounts, stealing sensitive data, perpetrating fraud, and carrying out cyberattacks.
We’re seeing a significant increase in the number of infostealer malware families that target cookies and information stored by browsers, with more than 22 billion device and session cookie records stolen by criminals last year.
Other botnet targets: credit cards, bank account logins, and digital assets like cryptocurrency wallets
Increasingly, criminals are also taking advantage of stolen credit card details and credentials for cryptocurrency exchanges and bank accounts – all using exfiltrated data from devices that have been infected by infostealer malware. A recent example is the Vidar AnyDesk campaign, which tricked users into downloading infostealer malware that targeted browser history, account credentials, passwords, cryptocurrency wallet data, and banking details.
Crypto wallet data in particular gives cybercriminals a host of follow-up options, from exploiting login credentials and private keys, to even transfering funds from the device owner’s wallet to the criminal’s own account. The Blackguard malware campaign is another recent example of just how much financial data can be stolen and used against you.
Contrary to popular belief, cybercriminals can also leverage anonymous cryptocurrency wallet data. Anonymous crypto wallets allow users to sell and trade digital assets without revealing private information about the owner or transactions completed by the owner – and some anonymous crypto wallet providers even offer IP address obfuscation support. But while these wallets are intended to offer more privacy and security than public blockchains, they can still be compromised when correlated to the owner’s emails, usernames, and passwords.
Botnets and the dark web
Once cybercriminals have your data, the next step is to monetize it. Typically, this means trading your data with other bad actors they know, or openly commoditizing it on the dark web. That means your video streaming credentials, bank login information, along with the other best kept secrets harvested from your computer may be for sale on an open market. And if you are a bad actor, you can even pay to install your own malware on previously infected hosts to help you carry out large-scale attacks or other bad behaviors en masse.
Some of the largest botnets can sport 600,000 to 1 million bots, resulting in huge revenue streams for threat actors. According to botnet research from the University of Twente in the Netherlands:
Distributed denial-of-service attacks using a network of 30,000 bots can generate around $26,000 a month. Spam advertising with 10,000 bots generates around $300,000 a month, and bank fraud with 30,000 bots can generate over $18 million per month. But the most profitable undertaking is click fraud, which generates well over $20 million a month of profit.
How to protect your enterprise against botnet attacks
Deploy antivirus / anti-malware software, keep it up to date, and run frequent scans on downloads and machines
It’s a critical first step to protect yourself from many cyber threats, but it’s not a silver bullet due to the growing sophistication of malware. Our team at SpyCloud recently uncovered that 20 percent of all recaptured infostealer logs had an installed antivirus application at the time of execution – but infostealers were still able to sneak in and steal data undetected
Think before downloading anything
While that free program looks tempting, it could be malware in disguise. Be suspicious of attachments from unknown sources; malware is primarily delivered by email and very commonly enters your inbox as a Microsoft Office document. Even those of us who work in security and are highly-suspicious can be tricked
Educate yourself and your users constantly
Some of us have gotten complacent with once-a-year security awareness training. It’s not enough. We need reminders not to click suspicious links and avoid downloading attachments from untrusted sources. I believe in the benefit of the Baader-Meinhof phenomenon, where after noticing something for the first time, you see it all the time. The goal of security training isn’t to make you afraid to use the tools you need to do your work, but instead to make you cautious about clicking that link or downloading that invoice from that new vendor’s finance contact.
Be vigilant about your online account security
Malware can result in breached accounts, particularly from keyloggers that can siphon your login credentials. If you notice an uptick in suspicious activity on several of your accounts (especially if you’re doing the right thing and using a unique, complex password for each account), the cause could be malware. I recommend installing an antivirus program and running a scan, then going through accounts and changing passwords once the machine has been cleaned.
Monitor for compromised users and devices
With the rise of session hijacking, expand your monitoring to programmatically account for stolen web sessions, and develop a process to invalidate web sessions related to infected users. Reacting quickly will give you the upper hand and prevent criminals from reaping the benefits of malicious activity.
We created a guide to remediating infections from malware, and I encourage you to check it out to learn how to handle these situations for your employees and consumers.