PRODUCT: ENDPOINT THREAT PROTECTION
Remediate
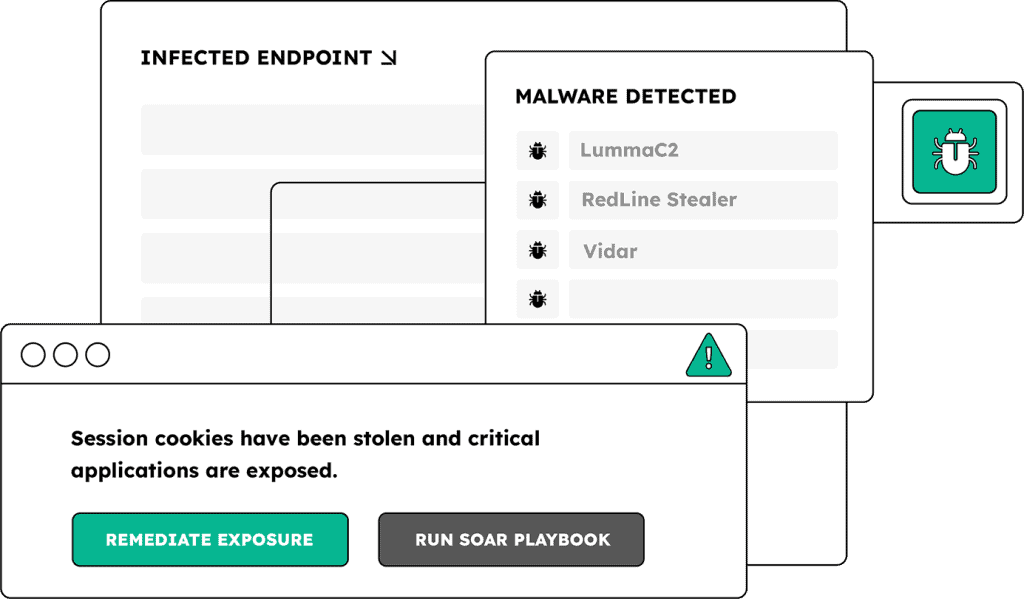
Malware-Infected Users & Applications
Where EDRs fall short, Endpoint Threat Protection fills the gap
Trigger password resets, invalidate sessions, and review access using context-rich identity exposure data for post-infection remediation
Explore how SpyCloud's continuous endpoint threat protection works
Built for the stack you already run
SpyCloud Endpoint Threat Protection integrates into your EDR, SIEM, and SOAR tools – enriching the workflows your SOC already uses to detect and contain identity threats without extra lift.



EXPLORE OTHER PRODUCTS
Protect more than logins
Identity Guardians
Automatically remediate exposed users in Active Directory, Okta Workforce, or Entra ID
Next steps
Don’t let malware-exfiltrated data lead to a full-blown incident. Get a demo today.
Endpoint Threat Protection FAQs
When infostealer malware infects a device, it exfiltrates far more than the user’s passwords. A single infection typically captures every credential stored in the browser across all profiles, active session cookies for every application the user was logged into, browser autofill data, device fingerprint information, and PII. A forced password reset addresses only the credential portion of that exfiltration. The session cookies stolen in the same infection remain valid and usable by an attacker until they expire or are explicitly revoked. An attacker holding those cookies can replay them inside an anti-detect browser to impersonate the victim’s authenticated session without triggering any login event or MFA prompt. The device fingerprint can be used to spoof the trusted device and bypass device-based risk controls. SpyCloud Endpoint Threat Protection surfaces the full inventory of what was exfiltrated from each infected device, including cookie counts, PII, and credential scope across every application accessed from that device, so security teams can scope and execute a complete response rather than issuing a credential reset and assuming the incident is closed.
EDR and MDM solutions only see enrolled corporate devices. BYOD laptops, contractor machines, and personal devices that employees use to access corporate applications through a browser are invisible to these tools. Infostealer malware infects those devices just as effectively as managed ones and exfiltrates the same corporate credentials and session cookies to criminal markets. SpyCloud does not rely on device agents or EDR telemetry. It recaptures infostealer malware logs directly from criminal communities where those logs are distributed and traded. Because SpyCloud’s data comes from the criminal underground rather than from device monitoring, it surfaces infections on any device whose stolen artifacts appear in those logs, regardless of whether the device was enrolled in corporate MDM or had an EDR agent installed. In 2025, 40% of infostealer infections recorded by SpyCloud occurred on devices that did have EDR or antivirus tools installed, which means even managed device coverage has a meaningful detection gap. Endpoint Threat Protection closes both gaps simultaneously.
SpyCloud surfaces device-level intelligence from each infection in recaptured malware logs, including: the full list of credentials exfiltrated from the device across every browser profile and application, a count of session cookies stolen alongside those credentials, PII captured by the malware, the malware family responsible for the infection (RedLine, LummaC2, Vidar, Raccoon, MetaStealer, and others), and the infection path and target URLs. The cookie count is a particularly important triage signal. A device with a high cookie count from an infection indicates a broader compromise footprint than a device where only credentials were taken, because those cookies represent active authenticated sessions across multiple applications that can each be independently exploited. SOC teams can use this signal to tier their response: infections with high cookie counts warrant full device investigation and session revocation across all affected applications, while lower-severity infections may be handled with targeted credential resets. Without this data, teams treat every infection the same way and either under-respond to high-severity cases or waste analyst time on low-priority incidents.
Infostealer malware is now the most common precursor to ransomware deployment. The attack chain follows a predictable path: infostealer infects a device and exfiltrates credentials, session cookies, and application access data; those artifacts are packaged into logs and sold or shared in criminal markets; a ransomware operator or affiliate purchases or acquires access to those logs and uses the stolen credentials or session cookies to gain initial access to the target environment; lateral movement follows using additional stolen access from the same log; ransomware is deployed. Nearly one in three companies that suffered a ransomware attack had a prior infostealer infection on record. SpyCloud interrupts this chain by recapturing malware logs from criminal sources in the window between exfiltration and exploitation. When SpyCloud surfaces a log match for an employee’s device, security teams have an opportunity to reset the stolen credentials, revoke the compromised sessions, and close the access paths before an attacker can act on them. The intervention point is the gap between the infection and the first use of the stolen artifacts — a window that can be hours to weeks depending on how quickly the logs reach criminal markets and how quickly the buyer acts.
Both products use SpyCloud’s recaptured infostealer data, but they serve different purposes and operate at different scopes. Workforce Threat Protection identifies which employee credentials have been exposed across breaches, malware logs, and phishing data, and triggers automated remediation through Active Directory, Okta, or Entra ID when a match is found. It answers the question: which of our employees have compromised credentials right now? Endpoint Threat Protection goes deeper into the device and infection layer. It surfaces the full inventory of what was stolen from each specific infected device — credential counts, cookie counts, PII, device fingerprint, malware family, infection path, and all affected applications — not just the credential match. It answers the question: what exactly was taken from this infection, and what is the full response scope? For standard credential hygiene and automated remediation workflows, Workforce Threat Protection is the right starting point. When a known or suspected infostealer infection requires investigation, or when a SOC team needs to understand whether a cookie count warrants a broader response beyond a password reset, Endpoint Threat Protection provides the device-level intelligence to scope and execute that response.