Security Orchestration, Automation, and Response (SOAR) platforms are valuable tools for security teams, providing a centralized platform for building and executing incident response workflows. At SpyCloud, we focus on layering on top of the SOAR solutions and workflows you already have in place to deepen your visibility into threats, and then make it easier to quickly fix known exposures that could lead to follow-on attacks.
Which brings us to the subject of this blog: our newest integration with Palo Alto Cortex XSOAR.
Why integrate SpyCloud with Cortex XSOAR?
SpyCloud surfaces exposed employee credentials from billions of recovered breach and malware records from the deep and dark criminal underground so enterprise security teams can decrease their exposure window and remediate compromised identities. For teams already using Cortex XSOAR, SpyCloud Enterprise Protection for Cortex XSOAR bridges gaps between identity-related exposure incidents and corresponding incident response and remediation workflows.
You can enrich your incident response by using Cortex XSOAR’s machine learning-powered bot, DBOT, to build out calls to SpyCloud’s API, and leverage SpyCloud’s extensive database of recaptured darknet data to quickly uncover hidden connections, identify potential threats, and gain a deeper understanding of related events surrounding each incident.
With the combined power of both tools, your team can have more confidence in its prevention efforts for targeted account takeover and cyberattacks.
What is Cortex XSOAR?
Cortex XSOAR® is the extended Palo Alto Networks SOAR platform that automates security workflows, streamlines incident response and improves overall security posture. It is a highly scalable and customizable platform that can be deployed on-premises, in the cloud, or as a hybrid solution. Enterprise security teams commonly use it to detect, investigate, and respond to security threats and incidents.
How the SpyCloud Cortex XSOAR integration works
With SpyCloud’s integration for Cortex XSOAR, breach and malware data from SpyCloud is ingested into XSOAR to create incidents and provide the ability to automate remediation. Security teams can use provided incident response playbooks or create their own automated playbooks for responding to compromised credentials and malware exposures.
The integration calls SpyCloud’s API to fetch new SpyCloud breach and malware records, and then generates corresponding incidents within Cortex XSOAR. Playbooks run automatically when incidents are created, pulling in additional enriched data for security teams to triage, assign, and remediate specific incidents. To complement the response to breach exposures, SpyCloud’s integration ingests contextual, highly actionable malware records from our reclaimed dataset to help remediate malware infections across users, devices, and applications.
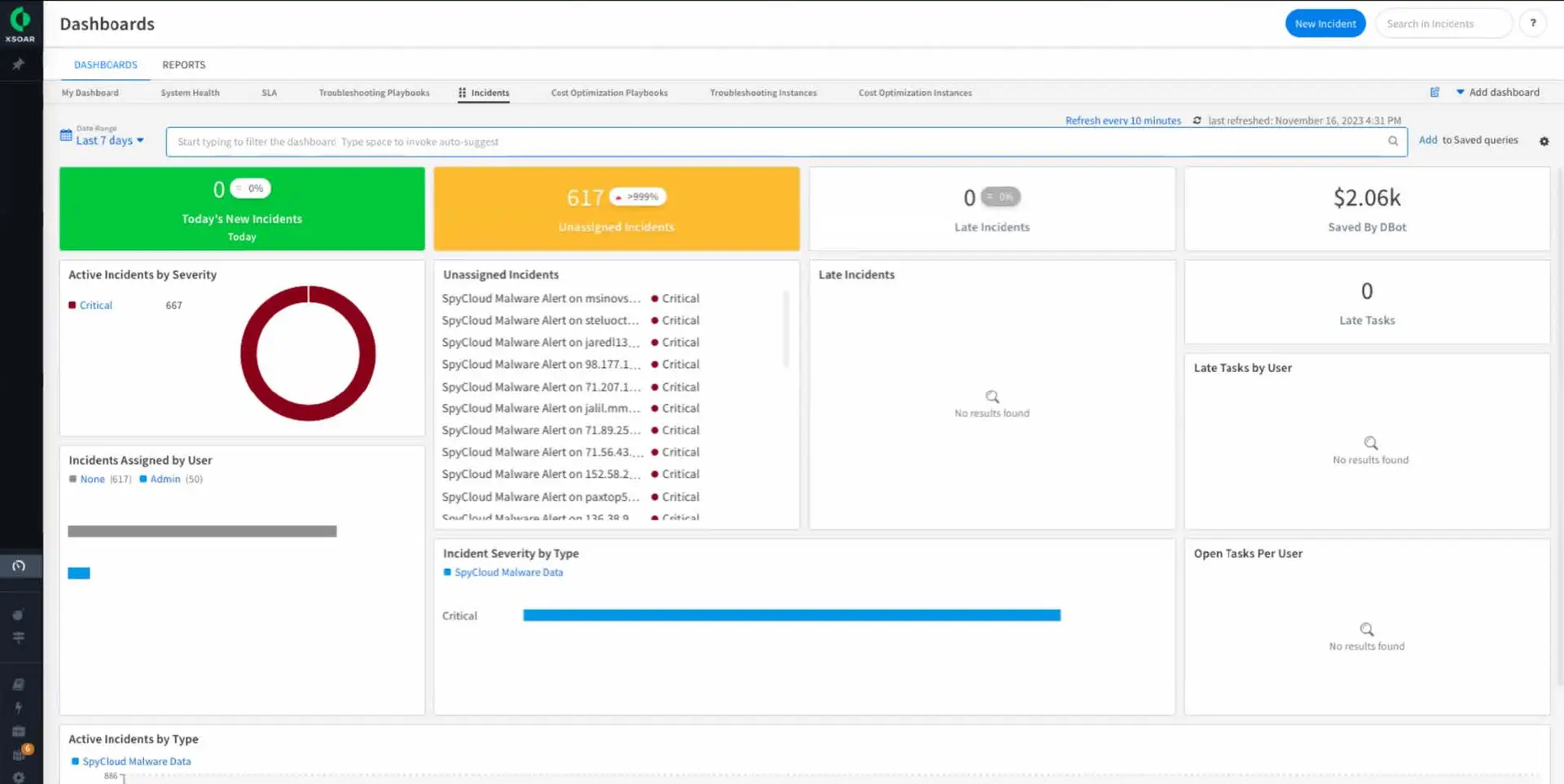
A view of the Cortex XSOAR Dashboard displays incidents generated by SpyCloud based on known exposures.
How to use the SpyCloud Cortex XSOAR integration
The Cortex XSOAR integration offers two playbooks for teams to leverage: a malware incident playbook and a breach playbook.
- SpyCloud’s Malware Incident Playbook enables follow-on actions once a malware incident is created to help you remediate malware exposures and remove all blindspots across users, applications, and devices. Customers with a license for SpyCloud’s ransomware prevention product, Compass, can view all SpyCloud malware records within XSOAR for exposed application credentials outside their primary watchlist to fully remediate all threats caused by malware infections.
Find out more about SpyCloud’s Post-Infection Remediation framework to optimize malware incident response protocols – designed to shut down follow-on attacks from stolen application credentials and session cookies siphoned by infostealer malware.
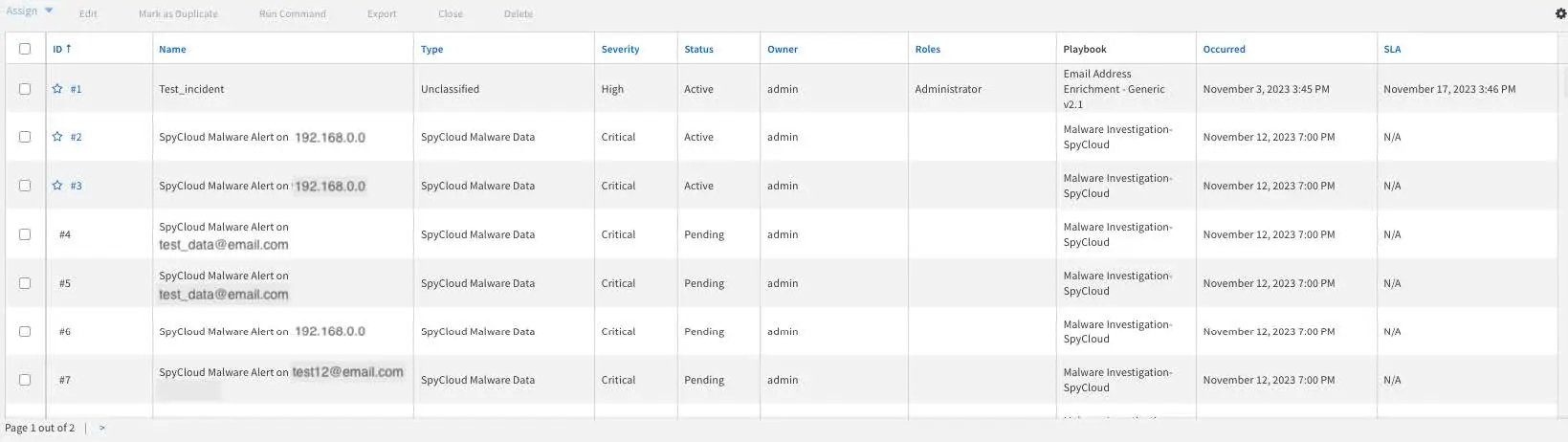
SpyCloud’s Breach Investigation playbook pulls in the latest records and checks the password length and employee status to help you triage the incident.
- In addition, SpyCloud’s Breach Playbook automatically acts on breach incidents. In the event of a breach where plaintext passwords were exposed, SpyCloud creates and flags the event as a high-priority incident in XSOAR and offers additional automated steps. Examples include: Checking the string length and password length to confirm it’s a threat; confirming it’s an active user and verifying their current passwords for a match; and then resetting the password and any additional steps.
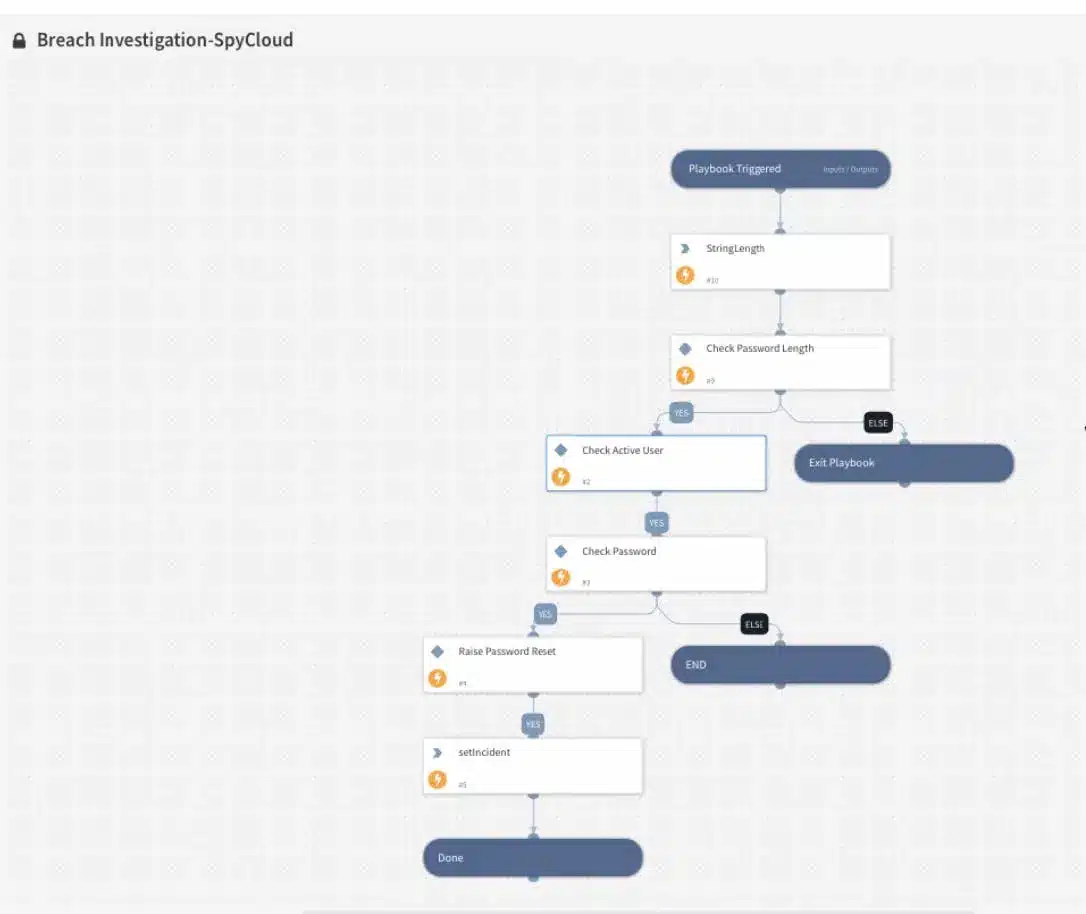
SpyCloud’s Breach Investigation playbook pulls in the latest records and checks the password length and employee status to help you triage the incident.
Here’s what you can expect using the SpyCloud integration with Cortex XSOAR:
Next-gen threat intelligence: SOC teams gain a holistic view of potential risks to their employees and can prioritize remediation efforts effectively.
Streamlined workflows: SpyCloud insights within XSOAR’s automated playbooks simplify the remediation process by reducing manual intervention and improving efficiency.
Advanced remediation: Teams can use XSOAR’s DBOT interface to easily create custom API calls to fetch information from SpyCloud’s database for more advanced remediation.
Technical requirements for the SpyCloud Cortex XSOAR integration
Analyzing SpyCloud breach or malware data within Cortex XSOAR requires:
- A license for SpyCloud Employee ATO Prevention
- An additional SpyCloud Compass license is required if you want to ingest malware records for applications outside the primary enterprise watchlist
SpyCloud plus your existing response and remediation workflows
Not a Cortex XSOAR user? Find other compatible SpyCloud integrations to augment your incident response or automated remediation workflows.
See it in action
SpyCloud offers out-of-the-box API integrations with top technology vendors across SIEM, SOAR, XDR, TIPs and more – delivering enterprise protection at scale.