TL,DR:
- Modern botnets deploy infostealer malware to harvest credentials and session cookies at scale, enabling attackers to bypass multi-factor authentication (MFA) and hijack active user sessions.
- These infections pose severe enterprise risks, including financial fraud and operational disruption, as stolen identity data is rapidly monetized on the dark web or used to launch secondary attacks like ransomware.
- Security teams must implement layered detection strategies that combine network monitoring and Endpoint Detection and Response (EDR) with dark web monitoring to identify and remediate compromised credentials immediately.
- To prevent future compromises, organizations should enforce strong access controls, maintain rigorous patch management, and establish protocols to programmatically invalidate stolen web sessions.
You’ve probably heard about information-stealing malware by now. It can take the form of trojans, viruses, and botnets. But the reality of this threat is much more insidious than you might think.
I grew up a Windows kid in the 80s, before the internet was a household item. Back then, we dialed up Bulletin Board Systems (BBSs) to download software. With those downloads came the risk of computer viruses, but by today’s standards, they were merely a nuisance.
Today, bad actors infect your computer with the worst of intentions. They are running a business focused on monetizing your data and, more specifically, your digital identity. This article focuses on one of their most powerful tools, the infostealer-driven botnet, and how to protect your organization from this hidden threat.
What are botnets? Definition and identity theft risks
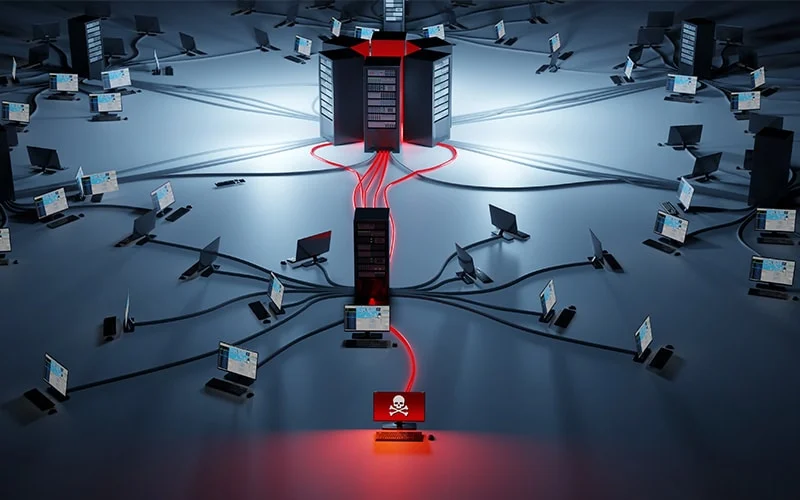
A botnet, or “robot network,” is a network of hijacked internet-connected devices controlled by a single cybercriminal. Each compromised machine, called a “bot” or “zombie computer,” is infected with malware that allows it to be controlled remotely. These bots are then networked together to carry out large-scale, automated attacks.
The entire network is managed by a criminal known as a “botmaster” or “bot-herder.” They use a central hub to issue commands and steal data from thousands or even millions of devices at once. For a business, this creates a persistent and dangerous internal threat.
This structure makes botnets a critical risk for identity-based attacks. Here’s how:
- Scale: Botnets automate theft across countless devices, harvesting massive volumes of credentials and session data.
- Stealth: Bots operate silently in the background, often going undetected by the device owner.
- Control: A botmaster has a direct foothold inside a user’s device, enabling deep data exfiltration.
Key components of a botnet
Every botnet consists of three core components working together. Understanding these parts is key to grasping the threat.
- Bots (Zombie Computers): These are the individual compromised devices, from laptops to smartphones. The device owner is typically unaware their machine has been hijacked and is awaiting commands.
- Command & Control (C&C) Server: This is the central hub that the botmaster uses to send instructions to the bots. It acts as the brain of the operation and helps conceal the botmaster’s identity.
- The Botmaster (Bot-Herder): This is the criminal operator who controls the botnet. Their goal is to grow the network and use its collective power to steal data or launch attacks.
How do botnets work?
A botnet’s operation is a multi-stage process focused on infection, control, and execution. While often associated with Distributed Denial-of-Service (DDoS) attacks, modern botnets are sophisticated platforms for a wide range of cybercrime. Understanding their lifecycle is key to recognizing the threat.
The botnet lifecycle: from infection to attack
A botnet is built through a methodical, four-stage lifecycle.
- Infection: Botmasters deliver malware through phishing emails, malicious downloads, or software vulnerabilities to compromise a device.
- Connection: The malware ‘phones home’ to the C2 server, registering the device as a new bot in the network and awaiting instructions.
- Command: The botmaster issues commands to the botnet through the C2 infrastructure, such as ‘steal data’ or ‘launch an attack.’
- Execution: The bots receive the commands and execute them, allowing the botmaster to leverage the entire network’s power.
Types of botnets and attacks
Botnets can be categorized by their technical architecture or their primary function. This helps illustrate the versatility of the threat.
Botnet architectures: centralized vs. peer-to-peer
The structure of a botnet determines its resilience and how it’s managed.
- Centralized (Client-Server): All bots connect to a single C2 server. This is easier for botmasters to manage, but has a single point of failure; if the C2 is taken down, the botnet is disabled.
- Peer-to-Peer (P2P): Bots communicate directly with each other to relay commands. This is a decentralized model that is much harder to dismantle, as there is no single server to target.
Common botnet attack types
Botnets are the Swiss Army knife of cybercrime, used for many malicious activities.
- DDoS attacks
- Spam and phishing campaigns
- Financial fraud and cryptocurrency mining
- Information stealing (infostealers)
How botnets enable session hijacking and MFA bypass
One of the most dangerous uses of modern botnets is session cookie theft. As enterprises adopt multi-factor authentication (MFA), criminals have pivoted their tactics. They now focus on stealing the session cookie created after a user has already authenticated.
This allows them to hijack the active, trusted session and bypass MFA entirely. Here is what that means:
- Theft: A bot on an infected device steals the active session cookie from the user’s browser.
- Bypass: The attacker uses that cookie to impersonate the user, gaining access to their account without needing a password or MFA code.
- Impact: This technique is effective against nearly all forms of authentication, enabling account takeover at scale.
The scale of this problem is staggering. SpyCloud researchers recaptured more than 8 billion stolen cookie records from the darknet in 2025.
What botnets steal: from credentials to cryptocurrency
Infostealer botnets are digital vacuum cleaners, designed to exfiltrate a vast array of valuable data from a compromised device. This stolen information provides the raw material for nearly every form of cybercrime. Key targets include:
- Usernames and passwords
- Session cookies and tokens for MFA bypass
- Credit card numbers and bank account logins
- Cryptocurrency wallet data and private keys
- Browser autofill data (names, addresses, etc.)
- System and network information for future attacks
Campaigns involving modern infostealers show how a single infection can lead to the total loss of a user’s digital and financial identity. Even crypto wallets are not safe, as botnets can steal the associated credentials needed to access them.
The business impact of botnet infections
For an enterprise, a botnet infection is not just a technical problem – it’s a significant business risk.
- Financial Losses: This includes direct fraud, high remediation costs, and regulatory fines for data breaches.
- Reputational Damage: A public breach erodes customer trust and damages the brand, leading to customer churn.
- Operational Disruption: Service outages from DDoS attacks or system compromises can halt business operations entirely.
- Compliance Risks: A botnet-driven breach can violate regulations like the General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA), leading to legal action.
How cybercriminals monetize botnets on the darknet
Once a botnet has harvested data, the botmaster’s next step is monetization. The darknet serves as the primary marketplace for this underground economy. Stolen data is packaged into logs and sold, while access to the botnet itself is rented out as a ‘Botnet-as-a-Service’.
This creates massive revenue streams for criminals. According to research, the economics are staggering:
- DDoS-as-a-Service platforms have lowered the barrier to entry, allowing criminals to launch attacks for as little as $30 per month.
- Spam and phishing campaigns facilitate Business Email Compromise (BEC), which is projected to cause globally in 2025.
- Digital ad fraud remains a massive revenue driver for botnets, with global losses projected to reach $100 billion in 2025.
While there are costs to maintain the network, the return on investment is enormous. This is why botnets remain a persistent and growing threat. This darknet activity is also a critical signal that a compromise has occurred.
Notable botnet attacks and what we can learn
Studying past botnet attacks provides valuable lessons for building future defenses. Here are a few landmark examples.
- Mirai (2016): This botnet used hijacked Internet of Things (IoT) devices with default passwords to launch massive DDoS attacks, disrupting major websites.
Lesson: IoT security and changing default credentials are not optional. - Emotet (2014-2021): Originally a banking trojan, Emotet became a ‘Botnet-as-a-Service’ that delivered other payloads like ransomware to enterprise networks.
Lesson: A botnet infection is often the precursor to a more devastating attack. - Raccoon Stealer (Ongoing with major disruptions): This modern infostealer specializes in harvesting credentials and cookies specifically for session hijacking and financial fraud.
Lesson: Defenses must account for post-infection data theft, not just prevention.
How to detect and prevent botnet infections
Protecting an enterprise from botnets requires a layered strategy. This includes both proactive prevention and reactive detection.
Detecting botnet activity
Since botnet malware is designed to be stealthy, detection often relies on identifying its side effects. Key methods include:
- Network Monitoring: Look for unusual outbound traffic patterns, such as connections to known C2 servers or unexpected spikes in data usage.
- Endpoint Behavioral Analysis: Use Endpoint Detection and Response (EDR) tools to spot signs of compromise like unexpected processes or system file changes.
- Darknet monitoring: Proactively monitor for compromised credentials from your domain, as this is the most reliable sign of an active infection.
Prevention methods for enterprises
While detection is critical, preventing the initial infection is the first line of defense. Follow these prevention methods:
- Deploy Layered Security Tools: Use and update endpoint protection, but remember it is not a silver bullet; SpyCloud research found that 66% of malware infections occur on devices with endpoint security solutions installed.
- Enforce Strong Access Controls: Implement strong, unique passwords and enforce MFA across all services.
- Conduct Continuous Security Training: Go beyond annual training with regular reminders about phishing and safe downloading.
- Implement Patch Management: Keep all systems and applications up to date to close vulnerabilities.
- Monitor for Post-Infection Exposure: Have a plan to programmatically identify and invalidate stolen web sessions to mitigate session hijacking.
For a detailed plan, see our guide to remediating malware infections.
Botnets are the primary engine for large-scale identity theft and corporate data breaches. A modern defense strategy should focus on post-infection remediation by monitoring the darknet for signs of compromise and neutralize threats before they escalate into a crisis.
Learn how SpyCloud helps you see beyond the breach and protect your digital identity.
FAQs
The Mirai botnet is a famous example that used IoT devices to launch massive DDoS attacks. Modern examples include infostealers like Raccoon Stealer, which focus on stealing credentials and session cookies.
Signs include unexpected slowdowns and strange network activity, but modern botnets are stealthy. For businesses, the most reliable sign is finding employee credentials or session cookies on the darknet.
Yes, creating or operating a botnet is a serious crime in most jurisdictions. Operators face charges for computer fraud, identity theft, and other related offenses.
Not exactly. A virus is a type of malware, while a botnet is the network of infected devices that have been compromised by malware (which could be a virus, trojan, or worm).
Ransomware is a loud attack that encrypts files for a ransom, while a botnet operates silently in the background. However, a botnet can be used to deliver ransomware as its final payload.