One question we get a lot from security teams is, “How does SpyCloud work with my existing tool stack?” The good news is that SpyCloud is not a “rip-and-replace” solution for organizations where you have to decide what to get rid of in order to reap the rewards of our Cybercrime Analytics solutions. Instead, we’re focused on layering on top of the solutions and workflows you already have in place to deepen your visibility into threats, and then make it easier to quickly fix known exposures.
Take, for example, our integration with Microsoft Sentinel…
Why integrate SpyCloud with Microsoft Sentinel?
SpyCloud Enterprise Protection for Microsoft Sentinel helps security teams triage and remediate identity-related exposure incidents – shutting down threats to prevent targeted account takeover and cyberattacks. SpyCloud publishes exposed employee credentials from billions of recovered breach and malware records from the deep and dark web, decreasing the exposure window and allowing for rapid action against compromised identities.
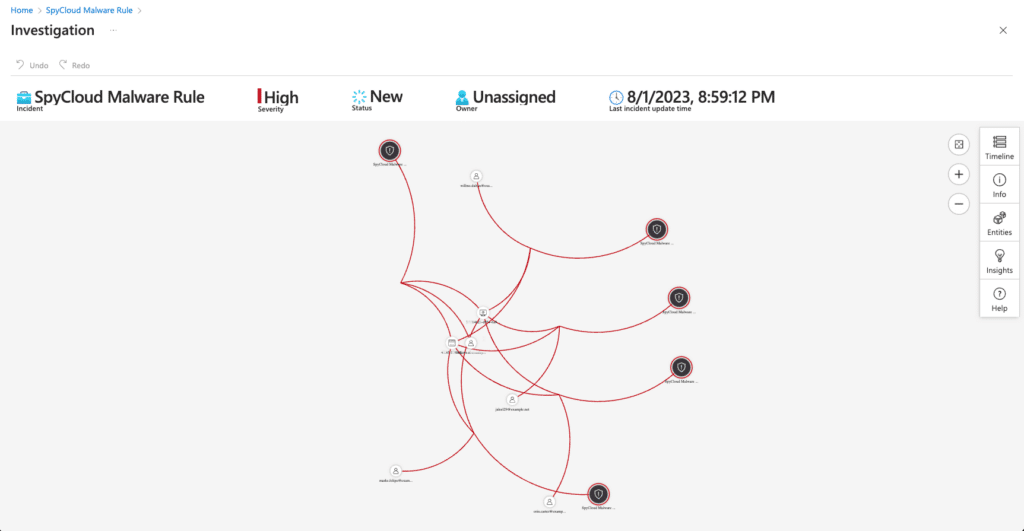
With SpyCloud Enterprise Protection for Microsoft Sentinel, breach and malware data from SpyCloud is ingested into Sentinel to create incidents and automate remediation. Security teams can take advantage of built-in incident response playbooks, or create their own automated steps for responding to breached credentials and malware exposures – calling SpyCloud’s API directly to gather enriched data for specific incidents.
What is Microsoft Sentinel?
Microsoft Azure Sentinel is a cloud-native security information and event management (SIEM) and security orchestration automated response (SOAR) solution provided by Microsoft. It’s commonly used by enterprise security teams to detect, investigate, and respond to security threats and incidents.
How the SpyCloud Microsoft Sentinel integration works
The integration calls SpyCloud’s API daily to look for new SpyCloud breach or malware records to then create incidents within Microsoft Sentinel. Teams can then run playbooks to automate responses, pulling in additional information to help with triage, assignment, and remediation. SpyCloud attaches contextual, highly actionable malware records from our reclaimed dataset to help remediate the full extent of malware infections across users, devices, and applications.
The integration includes access to SpyCloud’s API to check against SpyCloud entities (emails, Log IDs, host names, and IPs), add lookups in playbooks for deeper correlation within Microsoft Sentinel, or to build out custom automation tactics. By identifying exposed assets that are available to criminals, enterprises can protect exposed employee credentials before criminals have a chance to use them for follow-on cyber attacks.
How to use the SpyCloud Microsoft Sentinel Integration
You can run SpyCloud’s Malware Playbook to trigger the following actions when a malware incident is created:
Decide the appropriate response if the infection is related to a managed device or from accessing applications on a personal, unmanaged device
Ingest additional malware records for a specific incident to better understand the extent of the exposure
Alternately, you can run SpyCloud’s Breach Playbook to take action on breach incidents:
Check if the employee is still active or if the breached password length meets your requirements; if not, close the incident
Check against your IAM tool if the exposed password is in use on key applications
Automate a password reset trigger if the password is in use
Customers can use the provided playbooks as a starting point, with access to query SpyCloud’s API to pull additional context for more automation. Search the entire SpyCloud database by domain, email, IP, username, or passwords to pull entire user records of recaptured darknet data. Or search for specific applications or subdomains to identify any exposed credentials to enrich your Post-Infection Remediation.
Technical requirements for the SpyCloud Microsoft Sentinel Integration
SpyCloud Enterprise Protection for Microsoft Sentinel requires a Microsoft Power Apps or Power Automate plan with custom connector feature, along with an active Azure subscription. Analyzing SpyCloud breach or malware data requires a license for SpyCloud Employee ATO Prevention, and an additional SpyCloud Compass license is required to ingest malware records for applications outside the primary enterprise watchlist.
Get more details on the SpyCloud – Microsoft Sentinel integration here.
Other Microsoft integrations: Active Directory
A cybercriminal who gains access to your users’ Active Directory credentials through a third-party breach or malware infection can easily log into your network – accessing business-critical services such as remote file shares, Microsoft Exchange email services, SharePoint collaboration tools, and more. SpyCloud offers Active Directory Guardian as a seamless integration into your Active Directory environment to continuously monitor and take action on compromised credentials – safeguarding employee identities and securing access to corporate data and critical IP.
SpyCloud plus your existing response and remediation workflows
Not a Microsoft Sentinel or Active Directory user? Find other compatible SpyCloud integrations to augment your incident response or automated remediation workflows.



