What is the dark web, exactly?
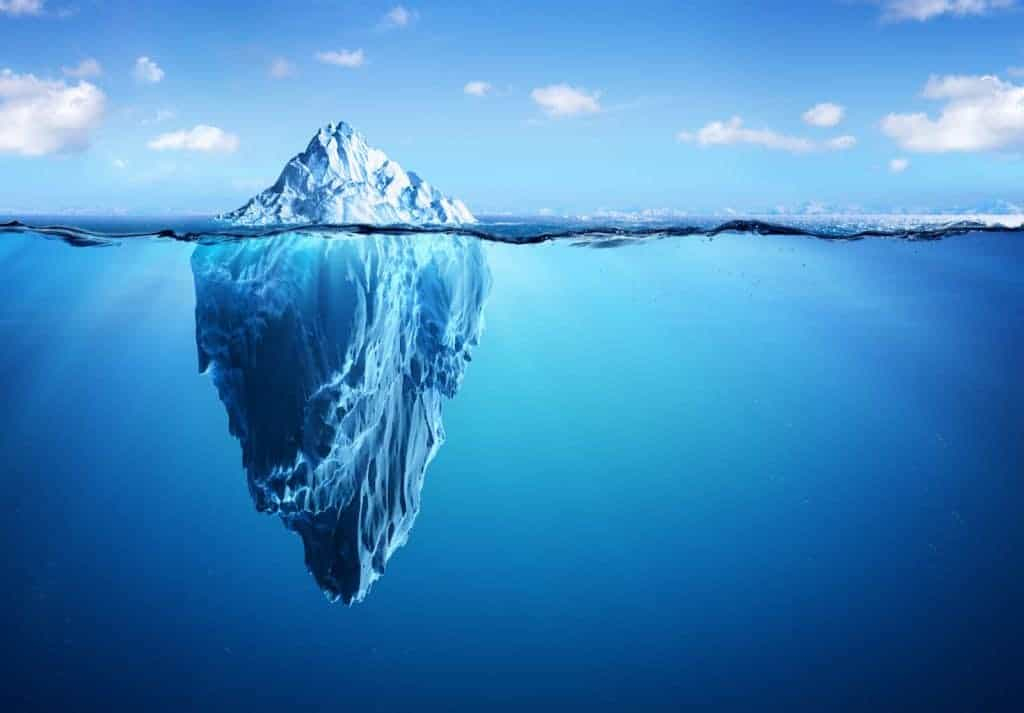
By now we’ve all heard of the dark web, but it’s often misunderstood. One of the best ways to visualize the internet is as an iceberg. The exposed portion we can see is literally only the tip. This is where the search engines and public websites can be found. We are comfortable with this “Surface Web” as it is where most of us spend the majority of our time.
What lies beneath is less known, but can be nefarious the deeper you go. What’s just under the surface is considered the “Deep Web.” This level contains a vast store of information, websites and files that have not been indexed by search engines. It also contains more sensitive websites that require the user to authenticate themselves through a username and password, such as a university’s resources. Company intranet sites, medical portals, subscription-based websites, government resources and other entities websites are located here.
The bottom-most level of the iceberg is what is referred to as the “Dark Web,” which has become infamous for its seedy reputation as a hotbed of drugs, pornography, and a general haven for questionable transactions. From illegally-obtained data to human trafficking sites, the dark web is not for the faint of heart. It requires specific software to access and is the playground for many types of criminals.
Why is the dark web so scary?
The dark web is not-so-secret, but it does contain plenty of information that is hidden from the majority of the population. For the cybercriminal and those who seek to discover their communities, it is the preferred sliver of the iceberg.
Cybercriminals hide in the dark web, communicating with each other and selling their stolen goods while aiming to evade detection. In the case of a data breach, such as Yahoo and LinkedIn, massive amounts of stolen personal information are sold on the dark web. It’s where usernames, passwords, social security and driver’s license numbers, credit card numbers, bank account information and much more is bought and sold to the highest bidder. They typically use cryptocurrencies such as bitcoin, z-cash, and monero which were designed to be virtually untraceable.
Often, we what we fear most is the unknown. Because we, as the general public, do not have access to the dark web, we aren’t certain of what’s there. What’s even scarier is that most of us realize that something about us is likely there, but we have no idea what it is or how it may be leveraged against us. In this case, money is power.
How does information get into the dark web?
Stealing personal information is a cybercriminal’s full-time job. Some criminals specializing in credential theft can bring in as much as $2 million per year. They use sophisticated technologies, such as specific software and bots, to crack passwords. They break through company firewalls and infiltrate even the largest companies. Data breaches have become so common, we often ignore the warnings to change passwords.
This brings us to another issue. Passwords are meant to provide unique access to sensitive websites and information. Unfortunately, most people choose weak passwords – those that are too short, too simple and too easily guessed. To make things worse, people use the same password (or a slightly modified version) across multiple accounts. As soon as one account is breached, criminals can use those stolen credentials to break into all of the other accounts that use the same password. This can happen regularly and at scale in a within seconds.
Once criminals breach a company’s system, they take ownership over all of their newfound data. They either use that data to take over user accounts in order to steal money or they advertise their bounty on the dark web in an attempt to get other cybercriminals to purchase the data. Often, they do both.
Which dark web monitoring tools are used and do they work?
The only way to catch the thieves and discover stolen credentials is to invest in a dark web monitoring tool. Consumers and organizations hoping to protect their employees and customers (and thus their sensitive data) cannot monitor the dark web on their own. They must hire a monitoring service that has the right technology and techniques to do it for them.
Scanners, crawlers, and scrapers
Dark web monitoring most commonly involves scanners, crawlers and scrapers that spend time in dark web forums where the stolen credentials are being advertised and sold. Once they pick up a match, they alert the account owner or company that their credentials have been compromised.
Unfortunately, scanners, crawlers and scrapers find stolen credentials too late for the victim to do much about it. By the time the stolen credentials are discovered on dark web forums, they have been used, abused and sold multiple times. The key is to find exposures as soon as they happen before criminals have time to do anything with them.
Password resets, notifications and multi-factor authentication
Once exposed credentials are discovered, some dark web monitoring tools automatically force the victim to change their password to an uncompromised one before they can log back into the system. Others simply notify the user their credentials were discovered in the dark web and prompt them to change their passwords. Sometimes they require a second authentication factor to verify the user is actually who they say they are and not a cybercriminal who has taken over the account.
While these extra steps do help with authentication, they are only enacted after the fact. None of the aforementioned dark web monitoring efforts do much to actually prevent stolen credentials from being used to take over an account.
Tools that find exposed credentials before ATO can happen
The only way to stop account takeover is to catch the exposure as soon as it happens. Not many tools have this capability. It requires the monitoring service to use technology that is as sophisticated or more so than what the criminals use. Human intelligence can be used to establish covert relationships with cybercriminals. This strategy provides a one-two punch, digging deeper into the dark web, well-beyond forums and uncovering data breaches within hours of the breach.
The best dark web monitoring tool will do more than simply find exposed data. It will cleanse the data and crack hashed passwords so that victimized companies and organizations can actually use the data. It will empower victims with context around the exposure so the frequency and severity of the exposure are understood in order to direct the appropriate remediation techniques.
Not all dark web monitoring tools work. Some don’t go far enough, others are too late, and many don’t operationalize the data they uncover. Find one that goes deeper, discovers exposures earlier and makes the data usable. It’s the only way to prevent account takeover and give you the return on your investment you expect.