PLATFORM
Protect Customer
Accounts & Stop Fraud with
Consumer Protection
Accounts & Stop Fraud with
The window between compromise and fraud is measurable – and actionable. SpyCloud Consumer Protection enriches your decisioning workflows with continuous identity exposure data, so your teams can identify at-risk accounts, step up authentication selectively, and stop fraud before it starts – without adding friction for the consumers who aren’t compromised.
Protect the person, not just the password
Unlike traditional solutions focused solely on login credentials, SpyCloud protects the full digital identity – including exposed session cookies and stolen device fingerprints – giving you an early warning system for targeted fraud.
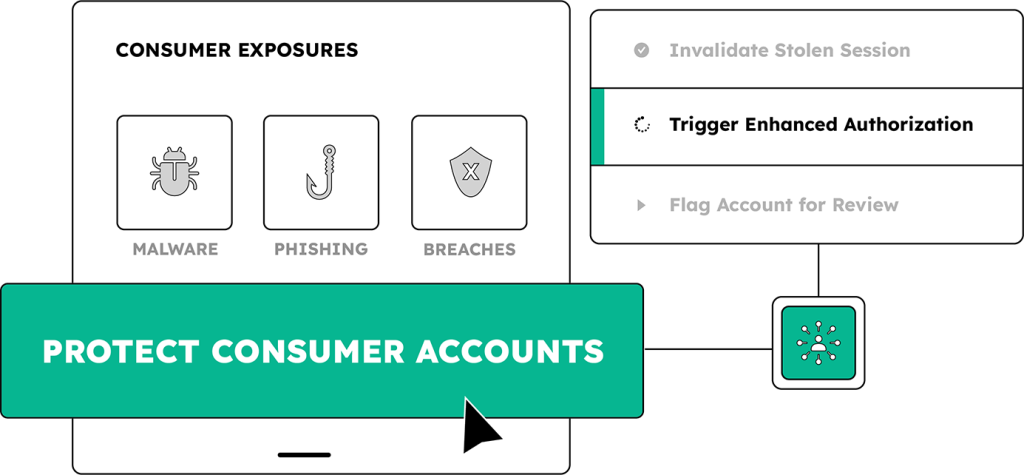
Detect compromised accounts whose exposed identity attributes – stolen from malware infections, successful phishes, combolists, and breaches – pose an active fraud risk to your business
Identify when an attacker has the means to hijack an authenticated session and bypass MFA – and take decisive action to invalidate the session, require reauthentication, or apply risk-based controls
Use SpyCloud’s enriched dark web identity data to uncover vulnerable users, detect risky behavior patterns, and take proactive steps to prevent fraud – before transactions occur or customer trust is compromised
WHEN TO USE SPYCLOUD
Deploy SpyCloud to protect consumer identities across every stage – without adding friction for legitimate users
SpyCloud Consumer Protection APIs integrate at four points in the consumer identity lifecycle. These approaches work independently or together for comprehensive coverage from account creation through active sessions.
Prevent consumers from creating accounts with exposed identity artifacts – checking credentials and associated exposure signals against SpyCloud’s recaptured identity data during registration, password creation, and password reset.
Enrich authentication decisions in real time as users log in – surfacing compromised identity exposure and triggering step-up authentication selectively for high-risk identities, without adding friction for users who aren’t at risk.
Continuously monitor your entire consumer account base for new identity exposures – catching compromised accounts regardless of login activity, so risk teams can act before customers are affected.
Protect consumers even after a successful login – by detecting and invalidating stolen session cookies and authentication tokens before attackers can act.
EXPLORE PRODUCTS
SpyCloud Consumer Protection Products
Secure your consumers’ digital identities with malware, phished, combolist, and breach data insights from the criminal underground, integrated directly into your application or workflows.
Get early warning of compromised cookies and tokens to protect authenticated sessions
Remediate stolen payment card data before it’s monetized by bad actors
Maintain persistent visibility into evolving exposures of customer credentials, PII, and other data
Our customers are everything to us. We have a core value around protecting them at all costs. So by adding Session Identity Protection to the rest of our SpyCloud instance, we basically get rid of the threat of account takeover, whatever the source – which means our customers and their data are safe.
EXPLORE WHO USES SPYCLOUD
Defenders
we help
THREAT INTELLIGENCE
Track breaches involving consumer data and triage high-severity threats to consumer identities