REPORT
2022 Report: Identity Exposure of London's FTSE 100
(And Their Subsidiaries)
As data breaches and malware infections continue to leak employees’ credentials and PII at a massive scale, their password reuse remains critically high, creating significant security risks for organisations and the consumers who rely on them to keep their data safe.
A single set of employee credentials that have been exposed in a third-party breach can leave the door wide open for bad actors to gain entry into a corporate network – but we found that London’s FTSE 100 and their subsidiaries have 2.7 million pairs of exposed plaintext credentials in the criminal underground.
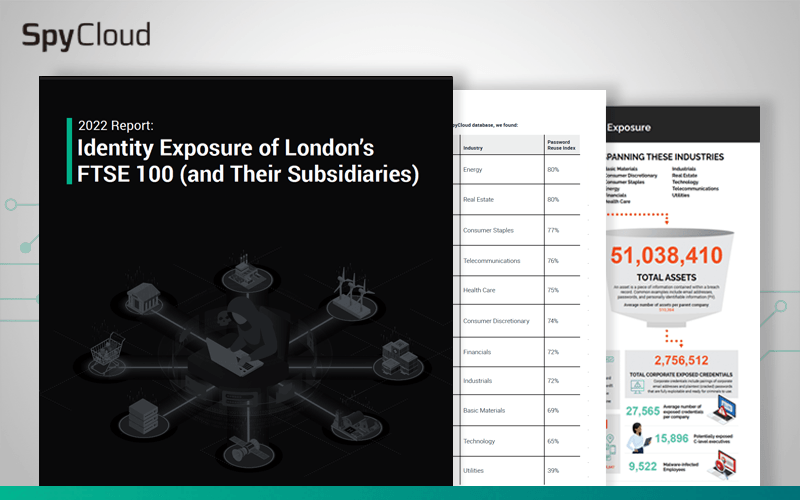
To provide a snapshot of employee identity exposures affecting major enterprises, SpyCloud analyzed the data we’ve recaptured from breaches, malware-infected devices, and other underground sources tied to FTSE 100 and subsidiary employees. We examined over 51 million assets, all of which are available on the criminal underground and can be used for malicious purposes.
- The types of stolen FTSE 100 employee data criminals have access to, and the danger it presents to these organisations
- The most popular exposed passwords of FTSE 100 employees
- Which industries lead in exposed data and severity
- The impact of malware-infected employees and consumers
2022 Report: Identity Exposure of London’s FTSE 100
Our annual analysis of exposed credentials and PII tied to London’s FTSE 100 employees uncovered insights about password reuse and malware-infected devices that put these organisations and the companies that rely on them at risk.
Trusted by market leaders
With 500+ customers around the world, including more than half of the Fortune 10, SpyCloud is the leader in operationalizing Cybercrime Analytics to protect businesses.
We’re on a mission to make the internet a safer place by disrupting the criminal underground. Together with our customers, we aim to stop criminals from profiting off stolen data.
#1 Global
Streaming Service
#1 Global
Airline
#1 Global Software
Company
Leading
US Banks
#1 Global
Online Retailer
#1 US Crypto Exchange
Check Your Exposure
See your real-time breach exposure details powered by SpyCloud data.
