TL,DR:
- Cybercriminals use Discord's private servers to trade stolen credentials and account cracking tools, fueling large-scale credential stuffing attacks against enterprise systems.
- Many monitoring tools lack visibility into these invite-only communities, leaving organizations blind to exposures data circulating in criminal hands – like reused passwords and vendor credential exposures that can lead to account takeover and other attacks.
- Security teams should implement automated password resets triggered by identity intelligence to neutralize identity-based threats stemming from exposures.
How Discord became a dark web alternative
Discord became a dark web alternative after law enforcement takedowns of traditional markets pushed criminals to its convenient, semi-private platform. Originally a gaming app, its features proved ideal for creating resilient, invite-only servers. This migration happened because criminals traded the high anonymity of the dark web for Discord’s ease of use and real-time collaboration.
Several key features made the platform attractive for illicit activities:
- Invite-only servers: Criminals create private communities that are invisible to outsiders and traditional security tools, requiring a specific link to join.
- Resilient structure: Groups operate ‘backup’ servers, allowing them to regroup instantly if their main server is shut down by Discord’s moderators.
- Real-time communication: Unlike static forum posts on the dark web, Discord offers instant text, voice, and video chat for faster collaboration and trade.
From darknet markets to Discord: a criminal migration timeline
The 2017 takedowns that changed everything
In July 2017, coordinated law enforcement operations shuttered the two largest darknet markets, AlphaBay and Hansa. This created a power vacuum and scattered the criminal community. Vendors and buyers initially migrated to platforms like Reddit to regroup, but a 2018 ban on such communities forced another migration.
The rise and fall of third-generation markets (2019-present)
In the wake of major takedowns, a wave of unstable markets rose to fill the void. However, they proved unstable, frequently falling victim to law enforcement pressure and exit scams, which eroded trust in centralized darknet markets.
Discord emerges as a criminal hub (2020-present)
The COVID-19 pandemic accelerated the adoption of digital platforms for all purposes, including crime. Criminals found Discord’s feature set ideal for their needs: easy to access, built for real-time community interaction, and harder to monitor than a public forum.
As of 2026, Discord exists alongside Telegram and other encrypted apps as a hub for displaced darknet communities. They often use sophisticated backup server strategies to attempt to evade takedowns, demonstrating their continued adaptation.
What criminals sell on Discord servers
The Discord servers we are focused on in this article function as specialized black markets. They are often organized by topic, with different channels dedicated to specific types of illicit goods and services.
Stolen credentials and breach data
One of the most common commodities is stolen identity data, the raw fuel for account takeover attacks. Examples include:
- Username and password combinations (‘combolists’)
- Email and password pairs from recent data breaches
- Targeted credential lists for high-value services
Fraud tools and methods
Bad actors also share and sell detailed tutorials and tools for committing fraud. This ranges from guides on exploiting government benefit programs to methods for defrauding digital payment apps and e-commerce sites.
Account cracking resources
These servers are central to the account cracking ecosystem. They provide all the necessary components for credential stuffing attacks, including:
- Configuration files for cracking tools
- Proxy lists to hide attacker origins
- Account checkers to validate stolen credentials
Discord's credential stuffing and account cracking ecosystem
The clearnet ‘cracking’ community has migrated some of its operations to Discord. These servers are dedicated to credential stuffing – the automated process of testing stolen usernames and passwords against websites. This ecosystem directly enables large-scale account takeover (ATO) fraud.
This ecosystem operates on a mix of free sharing and paid sales, creating a self-sustaining engine for identity theft. The success of these tools hinges on a single, widespread vulnerability: password reuse. When an employee reuses a password that appears in a combolist traded on Discord, their corporate account becomes an easy target.
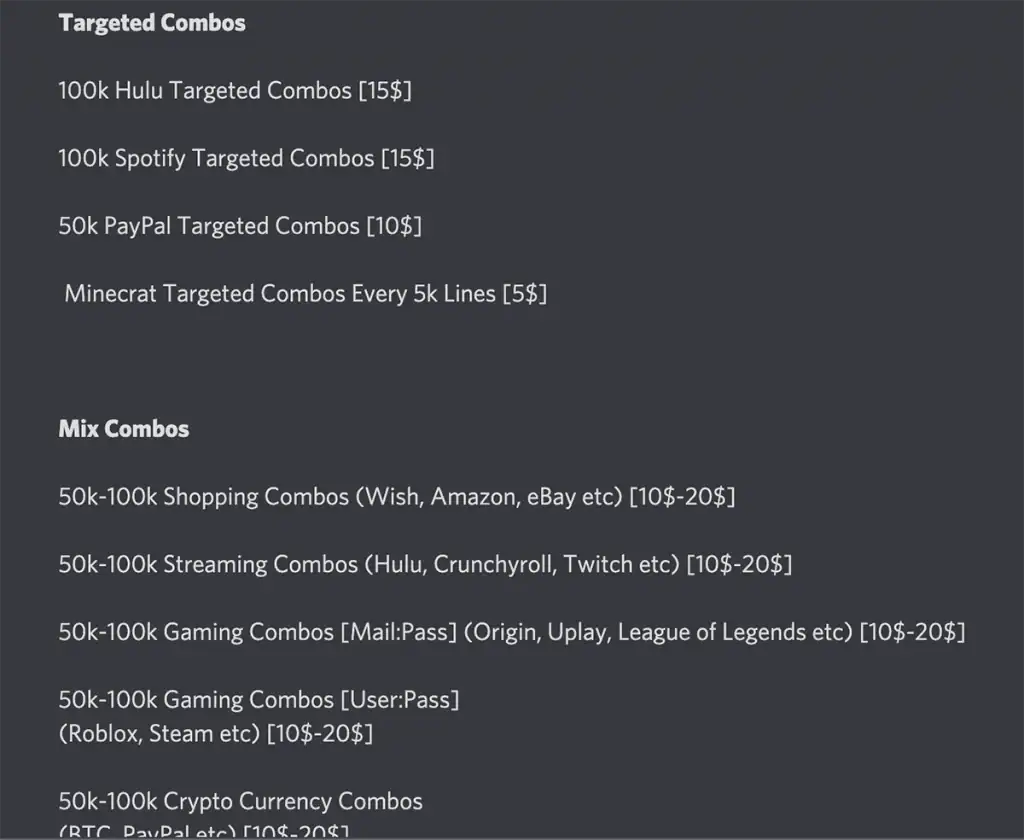
Figure 1: Screenshot of an advertisement for targeted combolists for popular services such as Hulu, PayPal, Spotify, Minecraft, and others. This screenshot was taken from a cracking Discord channel.
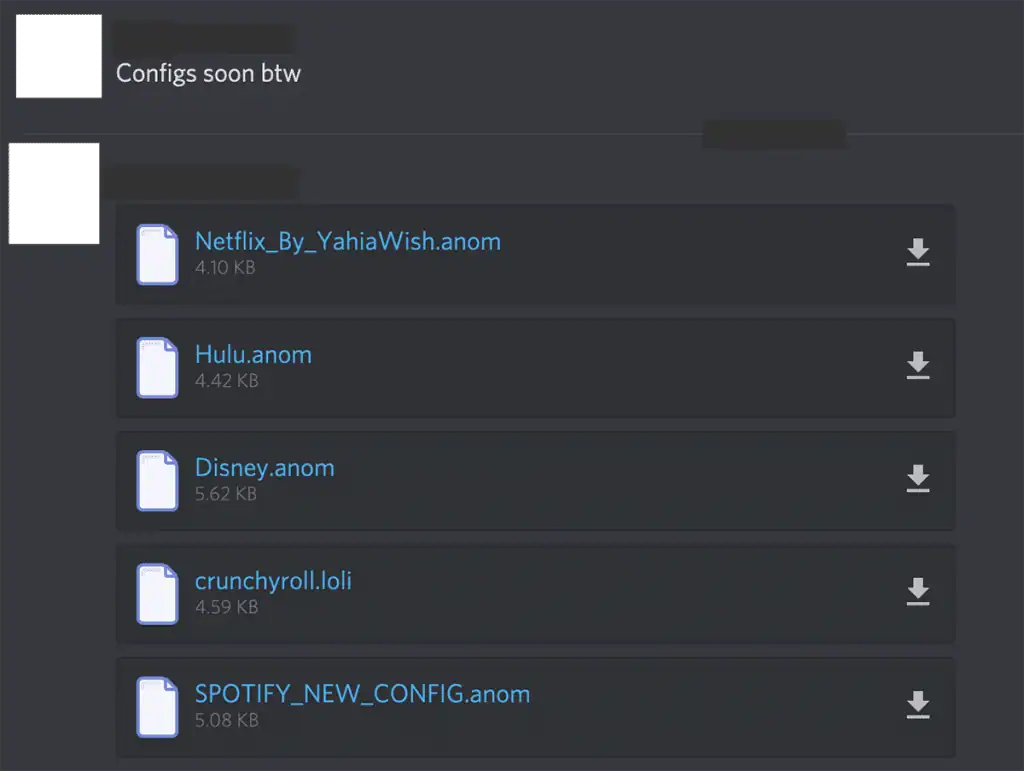
Figure 2: Configuration files posted to a cracking Discord server for services such as Hulu, Disney, and Netflix.
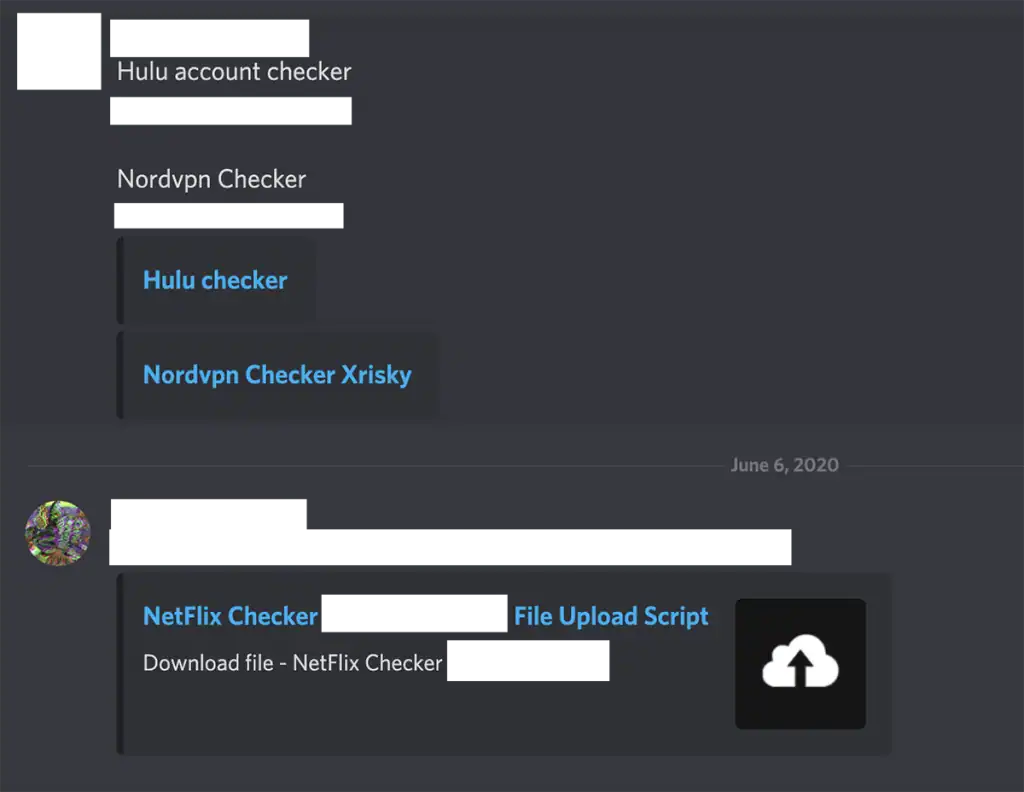
Figure 3: Custom account checkers being shared on a cracking Discord Server.
Why Discord dark web activity threatens organizations
While seemingly a consumer platform issue, criminal activity on Discord can pose a direct threat to enterprise security.
– Employee Credential Exposure: The most immediate risk comes from password reuse. When an employee’s personal credentials from a data breach are traded on Discord, attackers can then use them to attempt logins on your corporate systems.
– Supply Chain Threats: The threat extends beyond your immediate organization. Credentials belonging to contractors and vendors are also in circulation, creating vectors for supply chain attacks through compromised partners.
The detection challenge: why traditional security misses Discord threats
Detecting these threats is notoriously difficult for enterprise security teams. Traditional security tools lack visibility into Discord’s closed-off ecosystems for several reasons:
- Invite-only access: Most criminal servers are private and require an invitation link, which is not publicly accessible.
- Evasive tactics: Criminals use coded language and resilient backup server strategies to evade detection and takedowns.
- Lack of infiltration: Corporate security tools cannot infiltrate these criminal communities to see if employee or customer data is being shared.
The only effective way to gain visibility is through intelligence and data recapture from within these criminal circles.
How to detect and prevent Discord-based identity threats
Protecting your organization from threats originating on Discord requires a proactive, multi-layered approach focused on identity protection.
Monitor for credential exposures
Continuously monitor dark web intelligence sources that include recaptured data from closed criminal communities on Discord. This allows you to know immediately when employee or customer credentials appear, enabling you to act before account takeover occurs.
Detect malware-stolen data
Deploy solutions that can identify when data exfiltrated by infostealer malware is recovered. This allows security teams to remediate the full scope of an infection, including stolen session cookies that can bypass MFA.
Implement automated response workflows
Integrate your identity intelligence with your IAM (Active Directory, Entra ID, Okta) to trigger automated password resets. This closes the window of opportunity for attackers the moment an exposure is detected.
Report criminal Discord servers
While reactive, it is still important to report criminal activity to Discord’s Trust & Safety team and to law enforcement. Include any backup server links you can find to help disrupt the community’s ability to regroup.
SpyCloud also supports Trust & Safety teams directly with powerful investigative capabilities for threat actor attribution and platform abuse investigations.
Learn about SpyCloud Cybercrime Investigations for Trust & Safety teams >>
How SpyCloud protects against Discord-based identity threats
SpyCloud provides a critical layer of defense against threats emerging from Discord and other communities in the criminal underground. Our platform recaptures stolen data directly from criminal sources, including private Discord servers, giving you visibility that traditional security tools lack.
SpyCloud maintains a repository of billions of identity assets and can automatically detect when your monitored identities appear in these communities. This enables your security team to remediate exposures in minutes, preventing account takeover, ransomware, online fraud, and other attacks.
Give your security team the head start they need to prevent attacks stemming from dark web exposures
FAQs
Yes, criminals create invite-only servers that replicate darknet market functionality for selling stolen credentials, fraud tools, and compromised accounts. They use backup channels and coded language to evade detection.
Traditional security tools cannot monitor private Discord servers. However, identity threat protection platforms like SpyCloud recapture data directly from these criminal sources, allowing you to detect exposed employee credentials.
Discord offers easier access and real-time communication, but with less anonymity than Tor-based markets. Criminals trade operational security for convenience and speed.
Teams should monitor for credential exposures using dark web intelligence that includes Discord data. They must also implement automated password resets and deploy endpoint protection for protection against the infostealer malware that sources this data.
