Editor’s Note: This article analyzes BidenCash’s October 2022 free dump of 1.2 million credit card records. For updates on BidenCash’s subsequent activities and industry responses, see the Update section at the end of this article.
TL,DR:
- The primary risk from the BidenCash dump is not the credit cards, which were mostly old, but the accompanying permanent PII (SSNs, addresses, phone numbers) aggregated from past breaches and malware. Attackers use this data to execute targeted phishing campaigns and identity fraud, leading to enterprise account takeover.
- Security teams must implement continuous monitoring for exposed employee and customer PII across the dark web and malware logs. Upon detection, automate remediation by enforcing password resets and applying step-up authentication to mitigate account takeover risk.
- These large "free" dumps are a common marketing tactic by threat actors, not a new breach, but the exposed PII creates a permanent risk. A proactive defense requires ongoing monitoring and user education on phishing, as the data will be used for attacks indefinitely.
What BidenCash released in the October 2022 dump
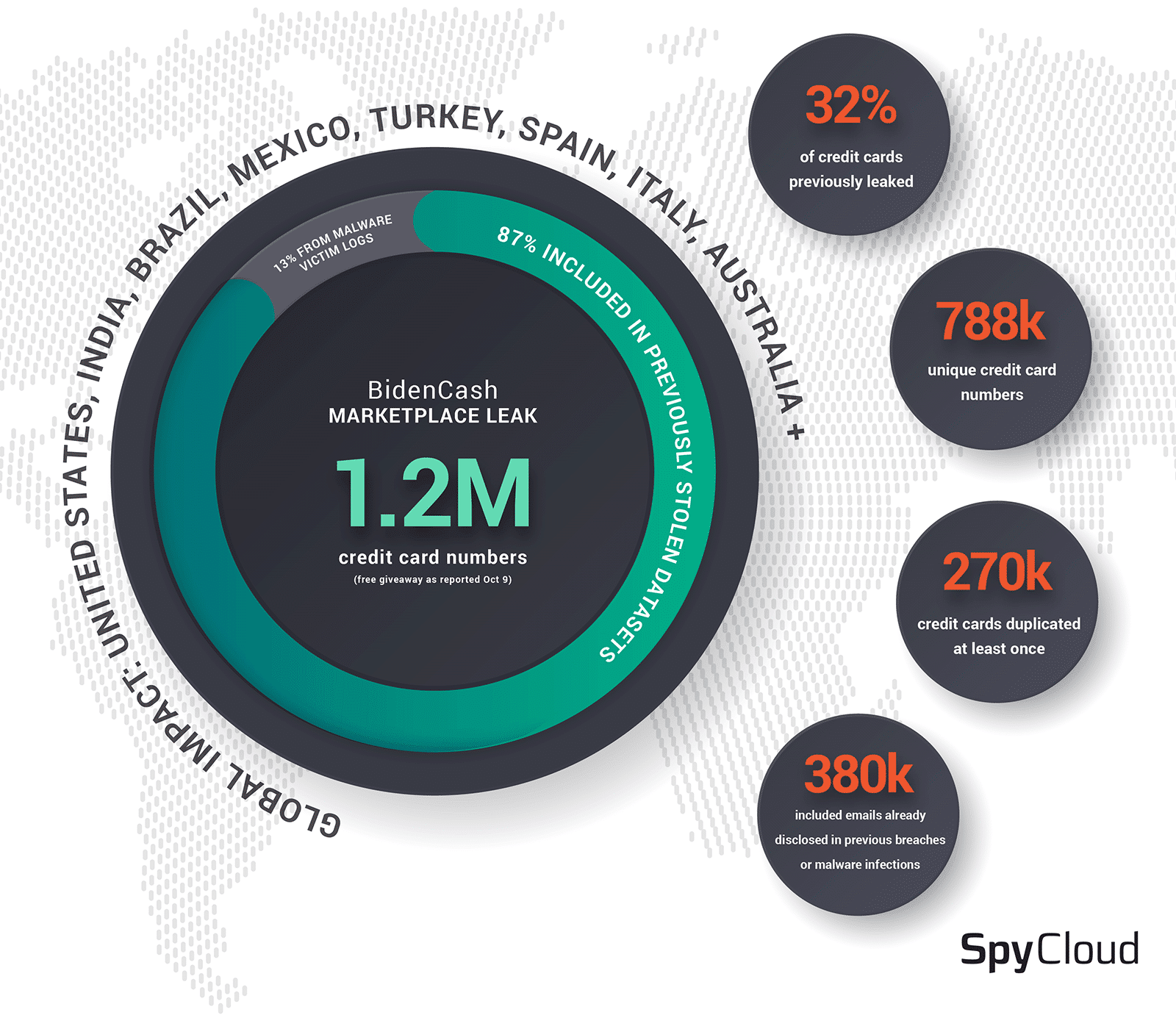
In October 2022, the underground marketplace BidenCash released a file for free download containing a purported 1.2 million credit cards. This release was a marketing tactic to attract customers to their platform, which had launched a few months prior in June 2022.
The dump included a wide range of sensitive data associated with the cards, including:
- Full credit card numbers, expiration dates, and CVVs
- Email addresses and phone numbers
- Physical addresses
- Social Security numbers and dates of birth
SpyCloud's validation methodology: Analyzing BidenCash against 800B+ records
To determine the authenticity and origins of the BidenCash dump, SpyCloud researchers conducted an in-depth analysis. We compared the dump’s information against our datalake of over 800 billion recaptured breach and malware assets.
Correlation and Sourcing: This cross-referencing process allowed us to connect exposed data to known breaches and infostealer malware logs. This validation accurately determines the data’s age and identifies its original sources.
Key findings: Data quality and authenticity in the BidenCash dump
Only 68% of records contain unique credit card numbers
Our analysis revealed significant duplication, calling into question the 1.2 million figure advertised by BidenCash. In reality, only 788,233 unique credit card numbers were present in the data.
This inflation is a common tactic for cybercriminals to overstate the value of their data. Our validation reveals the true scale of the unique records.
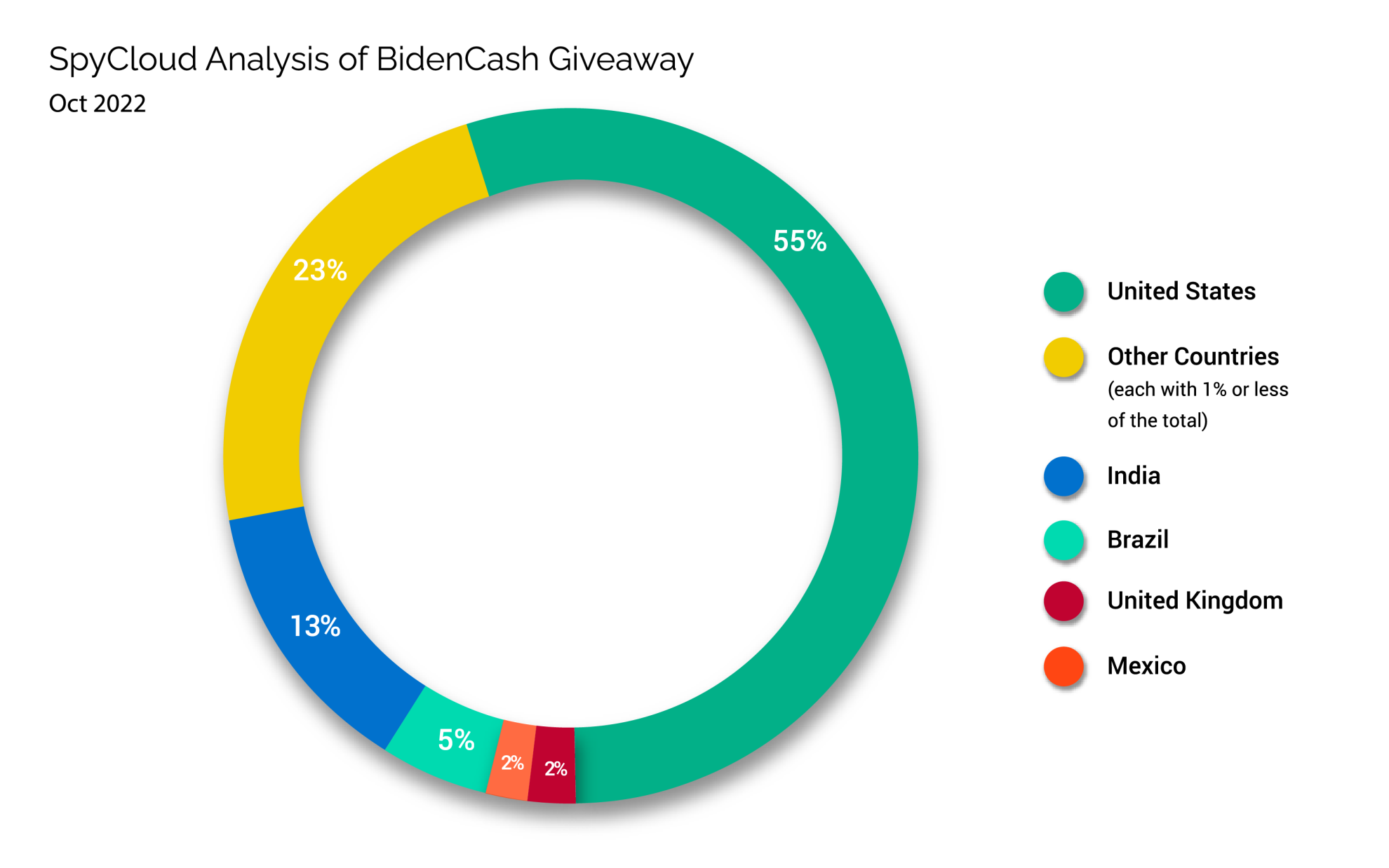
Geographic distribution: US-dominant but global impact
Approximately 50% of the victims were US-based, but the dump had a global reach with significant victim counts in India, Brazil, the UK, and Turkey. The fidelity of the associated data varied widely by country. For example, 40% of records from Turkey included a date of birth, compared to only 1.2% of US-based records.
Data sources: 87% breaches, 13% malware infections
By cross-referencing the data, we identified the source for 139,619 of the credit cards. The vast majority (87%) originated from previously known public breaches and dark web forum compilations.
The remaining 13% were traced to infostealer malware logs, primarily from RedLine and Raccoon stealers. This indicates the dump was largely a compilation of older data, not a fresh breach from a single source.
Timeline: Most cards were 6-14 months old at release
The age of the data further reduces its immediate value. While the most recent card was captured just before the dump in October 2022, the peak exposure period for the data was between July and August 2021.
The majority of cards were 6-14 months old, meaning many were likely already flagged and canceled by issuing banks.
Email and phone number overlap reveals hidden patterns
Of the 380,405 email addresses in the dump, SpyCloud had previously identified half in other breaches. Similarly, of the 578,524 phone numbers, we had already seen 242,556.
Observation dates for this PII stretched as far back as 2017, confirming that the personal data was aggregated from numerous older sources.
BidenCash's marketing strategy: A pattern of free dumps
The October 2022 dump was not an isolated incident but a calculated marketing move. This tactic of releasing large quantities of data for free is designed to achieve two goals in the competitive carding market:
- Establish credibility: Proving possession of a large data inventory builds a reputation among potential buyers.
- Attract customers: Media attention from a free dump drives traffic to their paid marketplace.
This strategy mirrors tactics used by other marketplaces, such as the 1 million free cards released by AllWorldCards in 2021.
The real risk: Beyond expired credit cards
While many of the credit cards in the BidenCash dump were old and likely canceled, the true, long-lasting risk lies in the accompanying personal data.
Why immutable personal data poses long-term threats
Unlike a credit card, which can be easily replaced, personal identifiable information (PII) is often permanent. This dump exposed a significant volume of immutable data, including:
- 847,000 physical addresses
- 508,000 phone numbers
- 10,000 Social Security numbers
- 18,000 dates of birth
This data, especially SSNs, provides criminals with the foundational elements for persistent identity-related crimes.
Synthetic identity fraud and downstream attacks
Armed with this PII, fraudsters can engage in far more damaging activities than simple card fraud. They can create convincing synthetic identities, apply for new lines of credit, and commit various forms of fraud.
Downstream Attacks: This data also enables highly targeted phishing attacks against individuals and the enterprises they work for. Defending against these attacks is a long-term battle, as the exposed data remains a permanent risk.
How organizations can respond to BidenCash exposures
Organizations must be proactive in defending against the fallout from large-scale data dumps. A multi-layered approach is essential for protection.
- Monitor for exposures: Implement continuous dark web monitoring to detect when employee or customer data appears in breaches or malware logs.
- Automate remediation: Deploy solutions that can force password resets and flag accounts for step-up authentication upon exposure detection.
- Protect against payment fraud: Leverage tools to proactively identify and block transactions associated with compromised cards before fraud occurs.
- Educate users: Inform employees and customers about the risks of phishing and account takeover that arise from their personal data being exposed.
Update: BidenCash developments since October 2022
Since the October 2022 dump, the BidenCash marketplace has remained active, continuing its strategy of periodic free data releases to promote its platform.
- Subsequent Dumps: The group released another 2.1 million cards in February 2023 and 1.9 million Visa cards in December 2023.
- Industry Response: In March 2024, Visa reported it had identified 556,000 at-risk accounts from these dumps and notified issuing banks to mitigate fraud.
These developments confirm that free dumps remain a popular cybercriminal marketing tactic, making continuous monitoring for exposed PII essential.
You can protect your business and consumers from darknet data leaks. Check your exposure now.
Frequently Asked Questions
BidenCash is a dark web carding marketplace known for selling stolen credit card data. It has also released large dumps of data for free as a marketing tactic.
Financial institutions typically notify affected cardholders directly if their card is at risk. Individuals can also use identity monitoring services to check for exposures.
Many cards were old and likely blocked by banks at the time of the dump. However, the associated personal data remains valid and exploitable for identity fraud.
Unlike most marketplaces that sell all their data, BidenCash released millions of records for free. This was a marketing tactic to attract paying customers and build their reputation.
SpyCloud validates dumps by cross-referencing exposed data against our repository of over 900 billion recaptured breach and malware records. This process identifies the data's original source, age, and any duplication.