TL,DR:
- Credential stuffing exploits password reuse using stolen breach data, whereas password spraying targets common passwords across multiple accounts to evade detection.
- These automated attacks threaten enterprises with severe financial and regulatory consequences by facilitating large-scale account takeovers and lateral movement.
- Security teams should immediately implement phishing-resistant MFA, enforce National Institute of Standards and Technology (NIST)-aligned password policies, and utilize intelligent rate limiting to block bot traffic.
- Prevent future compromises by continuously monitoring for breached credentials on the darknet and automating remediation to neutralize exposures before exploitation.
Credential-based attacks are a persistent threat for enterprise security teams. As digital footprints expand and employees manage hundreds of accounts, the attack surface for credential exploitation grows. Two methods dominate this landscape: credential stuffing and password spraying.
Both attacks exploit weak password practices to facilitate account takeovers, but they use different mechanisms that require tailored defenses. Understanding these differences and overlaps is critical for building a comprehensive identity threat protection program.
This guide examines both attack types, comparing their methodologies and the proactive measures security teams can implement to stop them.
What is credential stuffing?
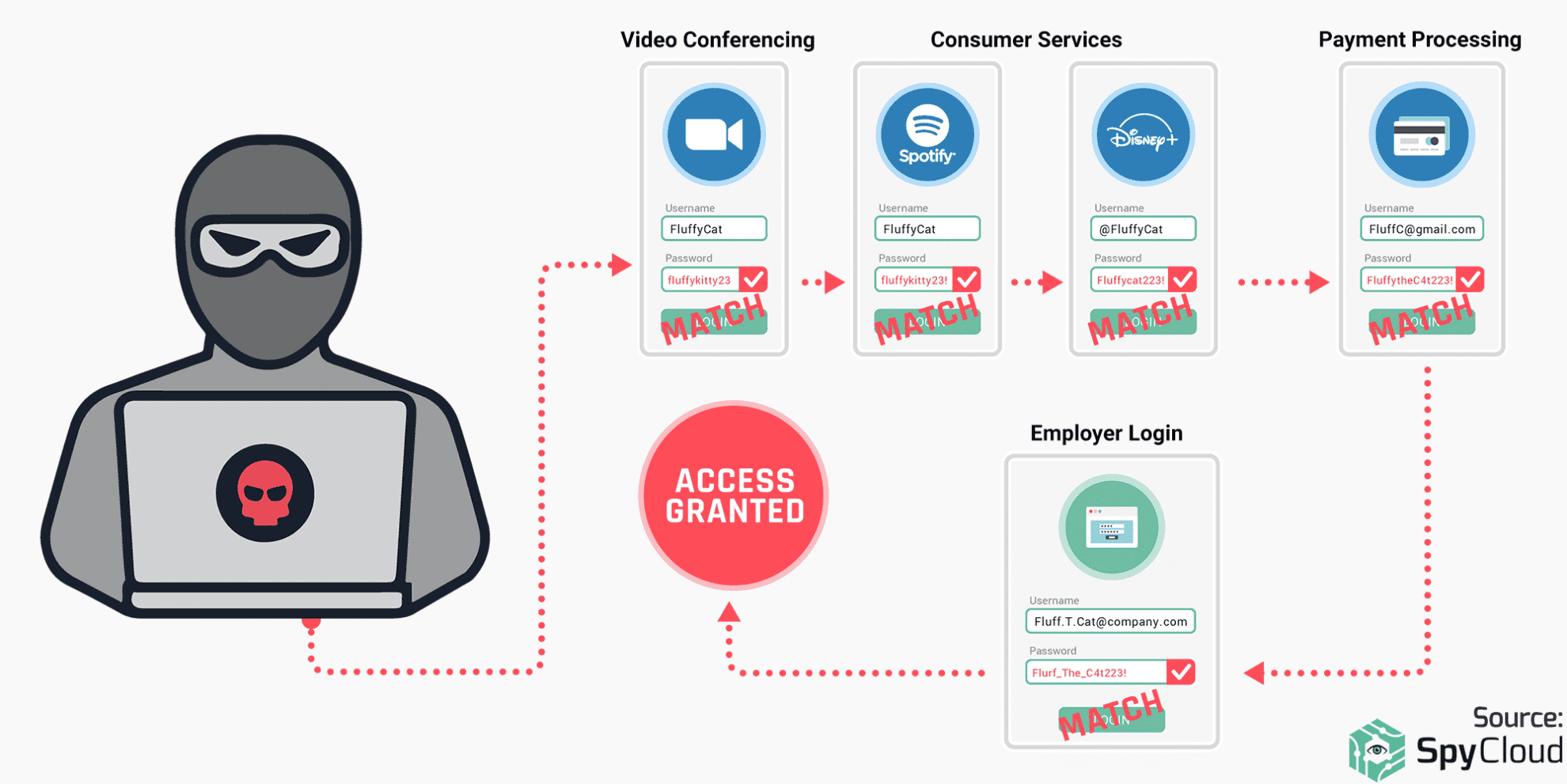
Credential stuffing is a brute-force attack where criminals use automated tools to test large volumes of stolen usernames and passwords across multiple websites. The attack’s success relies on the common user behavior of reusing the same password for different accounts. When the attacker’s tools find a match on a new site, they compromise the account.
How credential stuffing attacks work
The attack lifecycle is straightforward but effective. First, criminals acquire stolen credentials from data breaches or darknet marketplaces. They then use automated ‘account checker’ bots to test these credentials against many different online services.
Even with a low success rate of 0.1-2%, testing millions of credentials can yield thousands of compromised accounts. Attackers then harvest these compromised accounts for fraud, data theft, or resale.
Real-world credential stuffing breaches
Several high-profile breaches highlight the impact of credential stuffing:
- Disney+: Soon after its launch in November 2019, thousands of accounts were compromised due to users reusing passwords from other breached services.
- 23andMe: In October 2023, attackers compromised 14,000 accounts via credential stuffing, which they then used to access the genetic data of millions more users.
These incidents demonstrate the significant financial, reputational, and regulatory consequences for the enterprise.
What is password spraying?
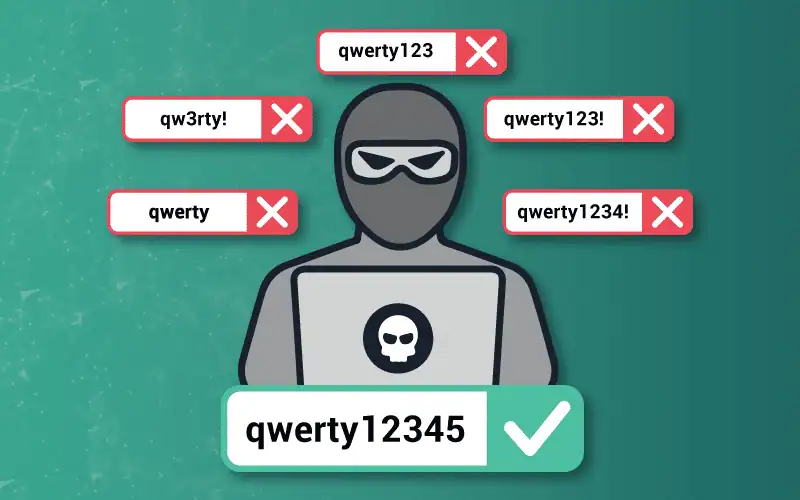
Password spraying is an attack that attempts to access a large number of accounts with a few commonly used passwords. Instead of trying many passwords for one account, attackers ‘spray’ one password across many accounts. This method helps them avoid triggering account lockout policies.
How password spraying attacks work
Attackers begin by compiling lists of valid usernames, often from public sources like corporate directories or LinkedIn. They select common passwords like ‘Password123’ or ‘Spring2026!’. The attacker then tests that single password against all usernames.
After a waiting period to avoid detection, they repeat the process with the next common password. This technique is effective at scale in large organizations, where even a 1% success rate can compromise dozens of employee accounts.
Why password spraying targets enterprises
Enterprises are prime targets for password spraying due to several factors:
- Predictable Patterns: Corporate password policies can inadvertently create predictable patterns, such as ‘CompanyName2026’.
- High-Value Targets: Access to enterprise systems via VPNs or remote access portals provides a gateway for lateral movement.
- Large Attack Surface: A larger number of employee accounts increases the statistical probability of a successful compromise.
Key differences: credential stuffing vs. password spraying
While both attacks aim for account compromise, they differ in their data requirements, execution, and detection patterns. Understanding these distinctions is key to implementing the right controls.
Data Source:
- Credential Stuffing: Requires stolen username-password pairs from previous data breaches.
- Password Spraying: Requires a list of usernames and a separate list of common passwords.
Methodology:
- Credential Stuffing: Tests many known, valid credential pairs against many different websites.
- Password Spraying: Tests one common password against many different user accounts on a single website.
Core Vulnerability:
- Credential Stuffing: Exploits user tendency to reuse the same password across multiple services.
- Password Spraying: Exploits user tendency to choose weak, common, or predictable passwords.
Detection:
- Credential Stuffing: Harder to detect; attacks often come from distributed botnets and mimic legitimate login attempts.
- Password Spraying: Easier to detect; security systems can spot patterns of one password being tried against many accounts.
How credential stuffing and password spraying overlap
Despite their differences, both attacks exploit the same fundamental weaknesses in password-based authentication. They also share common enablers that security teams must address.
Shared exploitation of weak password hygiene
Both attacks succeed because users choose predictable and reusable passwords. Credential stuffing exploits password reuse across different sites. Password spraying exploits the use of common passwords within a single organization.
The root cause is the same: users are overwhelmed and resort to poor password habits. Organizations that fail to screen for compromised or common passwords enable both attack types.
Dependence on automation and scale
Both attacks rely on automation to test thousands or millions of login attempts rapidly. The tools are readily available, making these attacks accessible even to less-skilled criminals. Because of this, defenses like rate limiting, bot detection, and MFA are effective against both threats.
How to prevent credential stuffing and password spraying
Defending against these attacks requires a layered strategy that combines policy enforcement, exposure detection, and authentication hardening. The following controls mitigate both threats.
Enforce strong, unique password policies
Implement NIST 800-63B guidelines, which recommend a minimum length and screening against known-breached passwords. Prohibit the use of common passwords and complexity requirements that create predictable patterns. This active screening should be continuous, not just at account creation.
Implement multi-factor authentication (MFA)
MFA is a critical defense that renders stolen credentials useless without the second factor. Deploy MFA across all critical access points, including VPN, SSO, and privileged accounts. Phishing-resistant MFA like FIDO2 offers the highest level of protection.
Deploy breach exposure detection
Continuously monitor for employee and customer credentials on the darknet and in breach databases. This allows you to detect exposures before criminals can exploit them. Automated remediation, such as forced password resets, can shrink the exposure window from weeks to minutes.
Use rate limiting and account lockout policies
Implement intelligent rate limiting that flags suspicious patterns, such as one IP trying many accounts or one account seeing logins from multiple locations. This goes beyond traditional per-account lockouts. Monitor for distributed attacks that rotate IPs to evade simple limits.
Protecting your organization with SpyCloud
While traditional defenses are important, proactive exposure detection and automated remediation offer the most effective defense. SpyCloud provides the darknet intelligence and automation to shut down these threats before they escalate.
Automated credential remediation
Identity Guardians integrates with Active Directory, Entra ID, and Okta to continuously screen employee credentials. It checks passwords against over 600 billion exposed assets from our recaptured data. The platform automatically flags and remediates exposures with zero administrative effort.
Proactive employee ATO prevention
Our solutions provide continuous detection of workforce credential exposures from malware logs and darknet sources. This enables security teams to remediate compromised accounts within minutes of discovery. SpyCloud gives organizations the earliest possible warning to prevent account takeover.
Protect your business from credential stuffing with SpyCloud
FAQs
Credential stuffing uses known username-and-password pairs stolen from breaches to break into other accounts, exploiting password reuse. Password spraying tests a few common passwords against many different usernames on a single service.
Both are dangerous, but credential stuffing often has a higher success rate per attempt because the credentials are known to be valid. However, password spraying can compromise more accounts at once within an organization that has weak password policies.
The best defense is a combination of implementing MFA and proactively monitoring for and remediating employee credential exposures from third-party breaches.
Password spraying avoids detection by trying only one password against many accounts over a slow period, which stays below the typical account lockout threshold designed to stop brute-force attacks on a single account.
A password is just one part of a credential, which is the complete set of information needed to authenticate, such as a username and the password combined.