— Yoda
Cybercriminals aren’t just stealing individual credentials anymore – they’re able to access vast amounts of users’ exposed identity data, making it easier than ever to slip past security defenses. With each breach, malware infection, or successful phishing campaign, their playbook expands, giving them new ways to infiltrate organizations with alarming precision.
The 2025 SpyCloud Identity Exposure Report takes a deep dive into just how much stolen identity data is out there – and how criminals are weaponizing it. SpyCloud’s total collection of recaptured data grew 22% in the past year, from 43.7 billion to 53.3 billion distinct identity records – representing a growing underground economy that thrives on compromised accounts and exposed credentials. And with 91% of organizations experiencing an identity-related incident last year, it’s clear that criminals are after more than just passwords.
Attackers are going beyond stolen logins. They’re hijacking session cookies, device fingerprints, personally identifiable information (PII) and more to impersonate users and gain access to sensitive systems, all while sidestepping security measures.
This year’s findings paint a clear picture: identity security strategies that focus on isolated threats leave organizations exposed. A more holistic identity security approach is the only way to get ahead of the game.
The Hidden Scale of Identity Exposure
Attackers will always look for the path of least resistance, and their method for gaining access have expanded exponentially in the form of rich, exposed identity records that have been leaked in breaches, exfiltrated by malware, or successfully phished.
Our research shows just how much identity exposure has escalated. Using holistic identity matching – where past, present, professional, and personal exposed data is correlated to individual users – the average corporate user now has 146 stolen records tied to their identity circulating in the criminal underground. That’s 12x more than the 11 records typically found using traditional methods. It’s trivial for threat actors to stitch these details, including stolen credentials, session cookies, and PII, together to perpetrate targeted attacks against individuals and organizations.
It’s even more alarming on the consumer side. The average exposed individual has 52 usernames and 141 credential pairs across 229 exposure records tied to their identity, often containing highly sensitive PII beyond full names and phone numbers – including physical addresses, passport numbers, and Social Security numbers. With that kind of data, cybercriminals can slip past fraud detection tools, impersonate victims, and pull off financial crimes with ease.
And it doesn’t stop there. Stolen data isn’t just a one-time risk – it’s a long-term problem. Cybercriminals don’t just use old credentials and move on; they repackage, resell, and cross-reference stolen identity data to refine their attack strategies and find new ways in, like using active session cookies to bypass multi-factor authentication (MFA). This is why resetting a password is a good first step, but is not the only step needed to minimize the risk stolen data presents to organizations.
How Attackers Exploit Stolen Identities
With billions of identity records at their disposal, attackers can bypass security measures, impersonate legitimate users, and infiltrate organizations – often without triggering any red flags.
Infostealer malware
One of the biggest culprits that makes this possible? Infostealer malware.
Our research shows that nearly 50% of corporate users have been infected with malware, whether through a personal or work-related device. Infostealers are calibrated to take immense amounts of data from swiping browser session cookies, autofill data, and even login credentials for business applications and AI tools; they have the power to give attackers instant access to corporate systems with one infection.
To better understand the full scale of what infostealer malware can exfiltrate and the ways in which cybercriminals are leveraging this data, in 2024 alone SpyCloud recaptured:
malware-exfiltrated credentials (email addresses, usernames, and passwords plus login domains), revealing the vast scale of data harvesting.
An average of 44 exposed credentials were harvested per infection, showcasing the depth of data extracted from individual infections.
cookies siphoned by malware – emphasizing the scale of session hijacking opportunities for cybercriminals.
An average of 1,861 cookies were harvested per infection, showcasing the depth of information extracted from a given device.
Phishing
Phishing is another major player in this growing crisis. But it’s more than just a well-crafted email scam. Cybercriminals have leveled up, using AI-driven phishing campaigns and Phishing-as-a-Service (PhaaS) platforms to make data theft easier and more convincing than ever.
Our research uncovered just how much information is being stolen. An analysis of the millions of SpyCloud recaptured phished data records shows:
of phishing logs included an email address, a critical foothold for identity fraud
contained IP addresses, making it easier for attackers to impersonate victims
included location data, enabling highly targeted social engineering attacks
Infostealers and phishing can go hand in hand. While infostealers quietly harvest large volumes of data from infected machines, phishing attacks that leverage previously stolen data can be more targeted and believable – like a tailored phishing email that mentions a service a user frequently accesses, based on browser history data exfiltrated from an infected device. It’s a more credible attack, with an increased likelihood of success – underscoring the need for early detection of infostealer malware and successful phishing attacks.
Data Breaches
One breach that highlights the scale of the exposed identity problem is the National Public Data (NPD) Breach – a dataset that surfaced in 2024, with 2.7 billion records containing 272 million unique Social Security numbers (accounting for roughly 80% of the US population) and 420 million addresses.
While this breach wasn’t caused by malware or phishing, its fallout makes both more effective. Cybercriminals cross-reference exposed PII with stolen credentials to create more convincing phishing lures, bypass identity verification, and carry out synthetic identity fraud. Meanwhile, malware operators use detailed PII to craft highly targeted social engineering campaigns, increasing the likelihood of infections that steal even more sensitive data – like session cookies, business application logins, and MFA tokens.
The takeaway? Attackers aren’t just relying on recent breaches. They’re compiling years of stolen data to bypass fraud detection and security measures in a variety of ways.
The Password Problem
Despite years of warnings about weak passwords, they remain one of the easiest ways for cybercriminals to infiltrate organizations. As the old saying goes, attackers don’t need to “hack” their way in – they log in using weak, reused, recycled, or stolen credentials.
We recaptured 3.1 billion exposed passwords in 2024, a staggering 125% increase from the previous year. But the bigger problem? Seventy percent (70%) of users exposed in breaches reused old, compromised passwords across multiple accounts. This means that a single exposed password can be the key to multiple corporate and personal accounts, fueling cyberattacks like credential stuffing and account takeovers.
But it’s not just a password reuse problem. Many passwords are laughably easy to guess or replicate Some of the most commonly exposed passwords in 2024 – unbelievably – included:
- “123456”
- “Admin”
- “qwerty”
As we’ve reported in years past, pop culture has an impact on password security. Millions of exposed passwords referenced trending topics, including:
- US Open/Tennis/Grand Slam (7.5 million)
- The Legend of Zelda (2 million) & Super Mario (almost 1.5 million)
- Taylor Swift (1.5 million) & Charli XCX / brat (295,000)
Cybercriminals track these trends, incorporating them into dictionary-based password-cracking techniques that allow them to guess weak credentials in seconds. This means that if a password is easy to remember, it’s probably easy to steal.
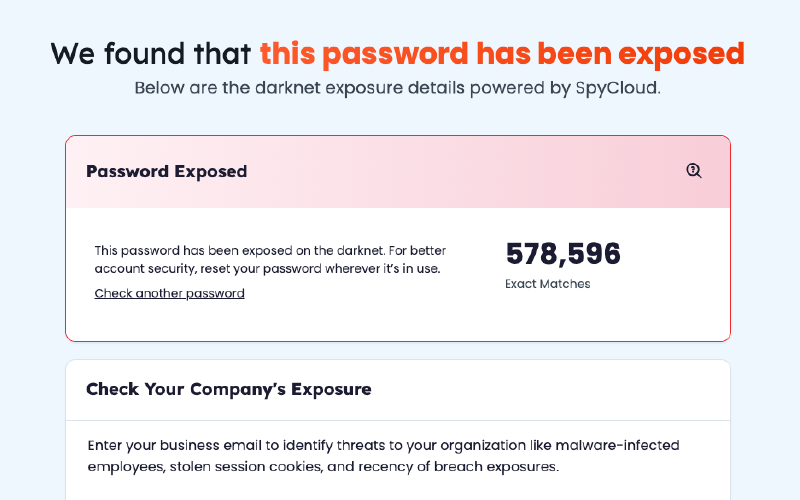
Don’t Pass on Checking your Passwords for Exposure
Are your passwords at risk? Enter the baseword to your password in SpyCloud’s Free Exposed Password Checker to see if it’s circulating the criminal underground.
Beyond Passwords: Why MFA Alone Isn’t Enough
Eighty-seven percent (87%) of large organizations rely on MFA as a safeguard, but cybercriminals are bypassing MFA using session cookies exfiltrated by infostealers. Session hijacking, an attack that hijacks an active web session, skipping the login process altogether, has become widespread. It’s no surprise, considering that in 2024 there were 17.3 billion stolen session cookies circulating the dark web, allowing attackers to impersonate legitimate users without the need for credentials, MFA, or passkeys.
Session hijacking is now a preferred method for next-generation account takeover, particularly when it comes to financial accounts and enterprise applications.
The Future of Identity Security
As cybercriminals evolve, organizations can’t afford to stay stuck in reactive security mode. Traditional defenses aren’t enough to keep up with the scale and sophistication of modern identity threats. Because the identity has become the perimeter.
So, what’s the next move?
It’s time for a proactive, holistic identity security approach – one that illuminates the full scope of users’ exposure on the dark web and automates remediation before criminals can leverage the stolen identity data.
Our 2025 Identity Exposure Report points to four critical areas where businesses should augment their identity security strategy:
- Identity analytics: Organizations must correlate exposed credentials, session cookies, and PII across breaches, malware infections, and phishing campaigns to fully understand and take action on the risk presented by the employees, third parties, and consumers interacting with their business.
- Automated remediation: Identity exposures should be immediately and automatically remediated before attackers weaponize the data – which can be as quickly as a few minutes. Best practice? Remediation that’s just as fast. SpyCloud handles it within five minutes from detection.
- Session hijacking protection: Billions of stolen session cookies allow attackers to bypass MFA and passwordless authentication entirely. Organizations must be able to rapidly detect and invalidate compromised sessions in real time.
- Zero Trust implementation: Security teams should continuously evaluate access permissions based on an individual’s full identity exposure, including how their data is perceived by cybercriminals.
A holistic, proactive identity security strategy can disrupt identity-based cybercrimes once and for all. The key is comprehensively understanding the data that makes any given user a risk and making it useless to attackers.
The Identity War is Here – Are You Ready?
Cybercriminals have perfected the art of weaponizing stolen identity data, and most organizations aren’t prepared for the scale of the threat. From infostealer malware that siphon valuable identity and authentication data to phishing campaigns that prompt users to provide even more, attackers have more information than ever at their disposal.
But there’s a way to fight back.