Most identity threats are invisible at the moment they matter most: a credential stolen in a third-party breach, or a username and password captured by an AI-powered phishing kit before the victim even realizes they clicked. Stolen identity data floods the criminal underground continuously, at the speed of automation, and it’s being used by criminals to illegitimately authenticate as enterprise employees and customers right now.
Most authentication flows can’t see any of it. They only see what is presented at login.
SpyCloud is proud to announce, in partnership with Ping Identity, two integrations that embed SpyCloud’s recaptured darknet identity data directly into PingOne DaVinci and PingOne Advanced Identity Cloud. At every identity event – user login, account creation, password reset – credentials are checked against SpyCloud’s leading database of stolen identity artifacts. When there is a match, the configurable Ping flows act automatically by blocking access, forcing a credential reset, or escalating to MFA.
No manual intervention, no delays, and no blind spots.
Illuminate the hidden risk, then eliminate it instantly
SpyCloud’s mission is to uncover hidden identity risks across your users’ digital footprint in data breaches, malware infections, and phishing attacks, and automatically remediate them before they become account takeover, ransomware, session hijacking, or fraud. That mission requires two things working together:
- The intelligence and insight to see what criminals already have in hand
- The infrastructure to act on it at the moment it matters
SpyCloud provides the intelligence. Ping Identity provides the infrastructure. Together, we empower enterprises to stop identity threats before they become incidents. Not an alert to investigate later or a dashboard to review in the next meeting, but holistic identity threat protection that fuels automated remediation at runtime – the moment a compromised identity presents itself.
The AI-driven threats jeopardizing your identity flows – and how these integrations help
The SpyCloud integrations with Ping Identity come at the perfect time – a time when we’re seeing AI and cybercrime enablement services escalate identity threats faster than any of us would like.
Phishing: The industrial-scale problem training can’t solve
AI-driven phishing campaigns and phishing-as-a-service (PhaaS) platforms have changed the game. These are not generic spam campaigns, nor are they poorly spelled emails and landing pages. Modern phishing campaigns are coordinated, automated operations that produce massive volumes of stolen identity data, siphoning anything they can from victims, including credentials, session cookies, authentication tokens, and MFA workflow data, at a scale that has outpaced most organizations’ ability to respond.
SpyCloud’s 2026 Identity Exposure Report underscores the acceleration. Successful phishing attacks surged 400% year over year. In 2025, SpyCloud recaptured 28.6 million phished records, approximately half of which included IP addresses and physical location data. These datasets increasingly include session cookies and authentication tokens that allow attackers to assume already-authenticated sessions without triggering a traditional login alert, making MFA bypass a routine capability rather than an advanced technique.
In March 2026, Europol, working with Microsoft and other private organizations, executed a coordinated seizure of Tycoon 2FA, one of the most prolific PhaaS platforms enabling MFA bypass through adversary-in-the-middle (AitM) techniques. SpyCloud contributed victim identity intelligence and operational analysis drawn from criminal underground sources to support the disruption effort. Even with that takedown, the pipeline of AI-generated phishing data flooding criminal markets continues at scale. Tycoon 2FA is one platform, but the underlying capability is everywhere.
Infostealer malware: The hidden threat inside the perimeter
Phishing gets the attention, but infostealer malware is often the quieter and more consequential threat.
Infostealer malware silently infiltrates devices, including personal devices employees use to access corporate systems, and extracts everything: credentials, session cookies, browser autofill data, business application logins, and authentication tokens. The infection happens outside the corporate perimeter, it doesn’t trigger an alert, and the stolen data arrives in criminal markets before anyone knows to look.
Last year, SpyCloud recaptured 642.4 million exposed credentials from 13.2 million infostealer malware infections, an average of 50 credentials per infection. Across those same infections, SpyCloud recaptured 8.6 billion stolen session cookies, each one a potential key to an already-authenticated session. Critically, 40% of those infections occurred on endpoints protected by EDR or antivirus tools.
Endpoint controls are not sufficient. The malware slipped through silently, on devices that either looked clean or were outside of corporate controls.
SpyCloud analysis of underground combolists found that 51% of records overlapped with previously observed infostealer logs, meaning criminals continuously repackage and recycle malware-exfiltrated data, combining it with breach data and phishing results to build richer identity profiles for more targeted follow-on attacks. Our research shows that nearly one in three companies that suffered a ransomware attack had a prior infostealer infection on record. The infection is the first step. The credential or session theft is the entry point. The ransomware event follows.
SpyCloud gets there first
The reason most organizations can’t see this exposure isn’t a lack of tools, everyone’s got plenty of those. It’s a data problem – both lacking quality and missing actual context.
SpyCloud infiltrates criminal communities directly, recapturing stolen identity artifacts from the source: breaches, infostealer malware logs, combolists, and phishing kits. SpyCloud’s recaptured data lake now totals 65.7 billion distinct identity records, a 23% increase year over year. Of the 5.3 billion credential pairs we recaptured last year, 80% contained plaintext passwords, which means SpyCloud customers can automatically check true credential-level matching rather than hash comparisons. This data arrives in SpyCloud’s collection weeks to months before it surfaces publicly, within minutes of appearing in the criminal underground, directly from the source.
That lead time transforms what is possible at authentication. When SpyCloud identity data is embedded in a Ping Identity flow, every login becomes a real-time check against the full scope of what criminals already have, not a check against yesterday’s breach notification. SpyCloud provides an instant comparison against the most comprehensive recaptured identity dataset on the planet, applied at the exact moment a credential is presented.
Two purpose-built integrations for workforce and consumer identity protection
SpyCloud’s Ping Identity integrations address the two distinct authentication environments Ping customers operate, each requiring different remediation approaches.
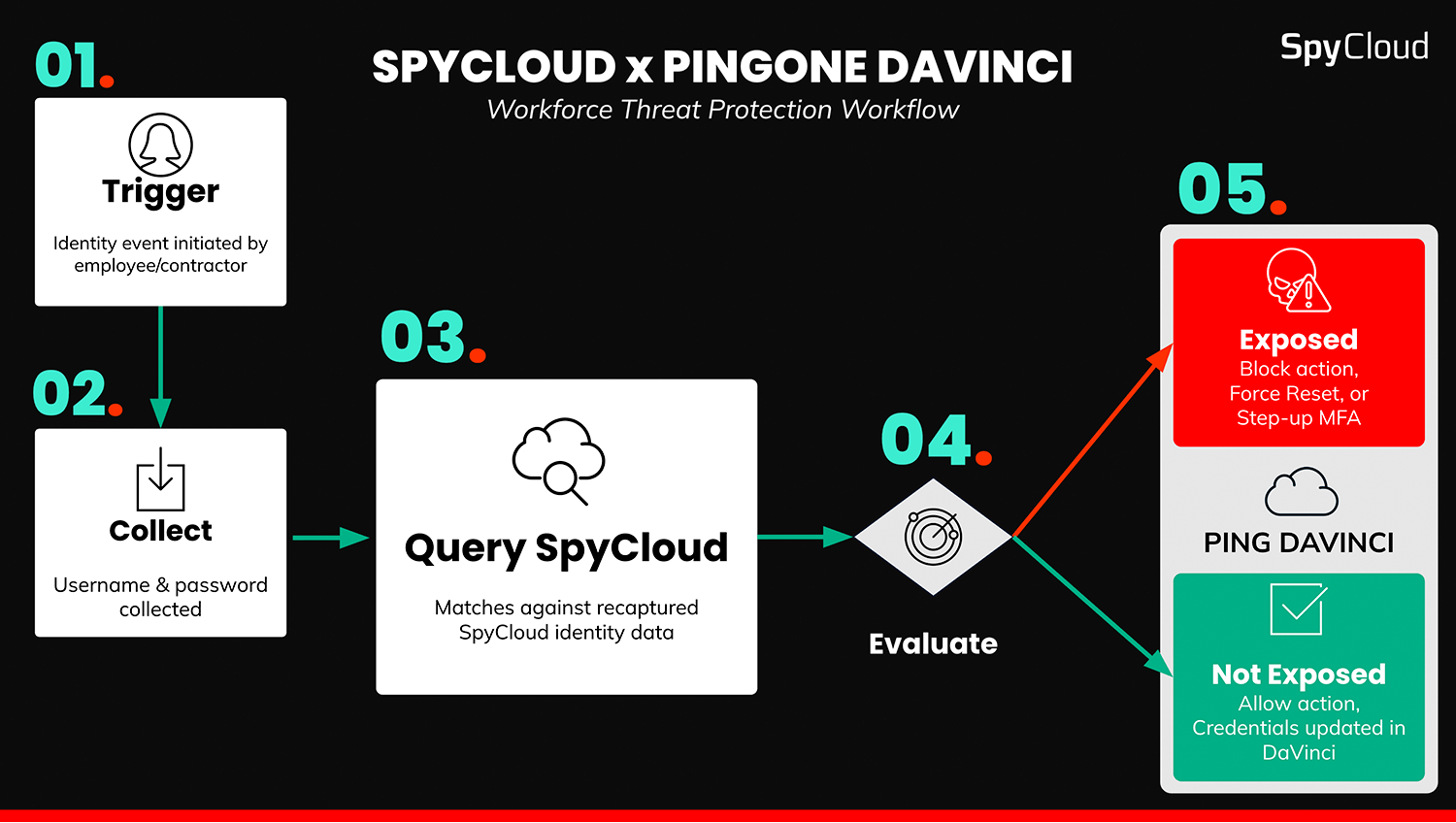
SpyCloud DaVinci Connector: Workforce Threat Protection
Your workforce is now three times more likely to be targeted by phishing than infostealer malware. Any organization becomes vulnerable the next time an infected employee logs in. The exposure risk is massive and most of it is invisible to your existing cybersecurity stack. The SpyCloud Davinci Connector for Ping Identity DaVinci remediates that risk automatically, at the moment it can actually be stopped.
The SpyCloud DaVinci Connector plugs into PingOne DaVinci, the no-code identity orchestration engine powering workforce authentication flows. At any workforce identity event, including login, registration, password reset, and IT onboarding, the DaVinci flow checks the presenting credential against SpyCloud’s continuously refreshed recaptured darknet data. When a match is detected, the flow can be configured to automatically block access, force a credential reset, or escalate to MFA.
No custom development is required. IAM architects add the connector to their existing DaVinci flow and configure the remediation logic. Compromised identity data that happened entirely outside the organization’s control is automatically surfaced and acted on at the moment of authentication.
SpyCloud Auth Node: Consumer Threat Protection
Most consumer fraud solutions detect anomalous behavior after an attacker is already inside the account or fraudulent activity occurred. SpyCloud stops compromised credential use before the attacker authenticates and before fraud happens, by checking what is already known to be compromised and before the access decision is made. That is the shift from reactive fraud detection to proactive identity threat protection.
The SpyCloud Auth Node is a Journey Node for PingOne Advanced Identity Cloud, Ping’s enterprise CIAM platform built for consumer authentication at scale. It connects into the no-code Journey builder, enabling identity teams to add SpyCloud’s exposure checks to login, registration, and account modification flows without a development sprint.
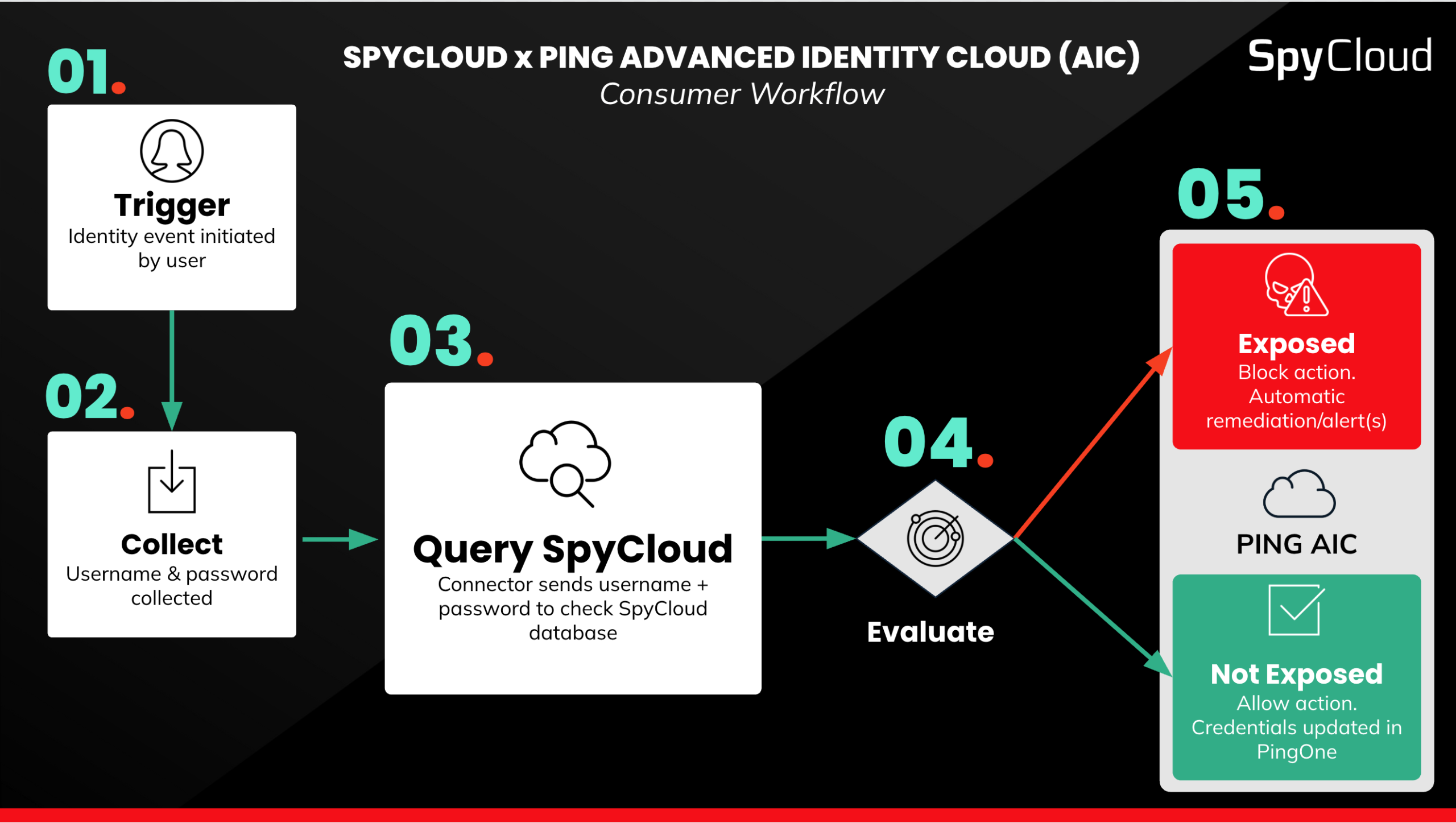
At each consumer identity event, the Auth Node checks the presenting credential against SpyCloud’s recaptured data and routes the journey to a configurable, risk-proportionate response: enforce MFA for moderate risk, block access or force a password reset for high risk, and alert fraud teams for investigation. Remediation can be configured to be automatic and proportionate, applying friction only where real exposure is detected, keeping the experience smooth for legitimate users while stopping compromised identities before authentication.
Case study: Real customer, real results
A Fortune 500 enterprise retailer operating consumer identity flows across millions of accounts has deployed SpyCloud with PingOne Advanced Identity Cloud to detect and block compromised credentials. At account creation and login, the SpyCloud Auth Node checks each credential against SpyCloud’s recaptured data and dynamically routes the journey based on risk: triggering mandatory password resets, blocking the creation or update of compromised credentials, and prompting users toward more secure choices. Zero additional development effort was required.
SpyCloud illuminates the hidden identity risk. Ping Identity workflows instantly eliminate it.
Stop cybercrime before it starts with SpyCloud + Ping Identity
SpyCloud exists to disrupt cybercrime. Breaches, account takeover, ransomware, and fraud are not random events; they are the downstream consequences of stolen identity data that most organizations never see.
SpyCloud recaptures that data before it becomes an identity attack. Ping Identity runs the authentication flows where those attacks are attempted. By embedding SpyCloud’s intelligence inside Ping Identity flows, organizations can automatically remediate identity threats at scale, at runtime, at the exact moment of an identity event, for both their workforce and their consumers.
The data fueling the next attack against your organization is already circulating in the criminal underground. SpyCloud sees it. Now your Ping Identity flows can act on it.
FAQs
Most authentication flows evaluate only what is presented at login — they have no visibility into whether those credentials have already been stolen and are circulating in criminal ecosystems. SpyCloud recaptures stolen credentials, session cookies, and authentication tokens directly from criminal communities, often weeks to months before they surface on public dark web forums. When SpyCloud’s intelligence is embedded in a Ping Identity flow, every login becomes a real-time check against the full scope of what criminals already have. If a credential matches SpyCloud’s recaptured dataset, the Ping flow responds automatically — blocking, resetting, or escalating — before access is ever granted.
The SpyCloud DaVinci Connector is a drag-and-drop connector for PingOne DaVinci, Ping’s no-code identity orchestration engine for workforce authentication. IAM architects add the connector to an existing DaVinci flow without custom development. At any workforce identity event — login, registration, password reset, or IT onboarding — the flow checks the presenting credential against SpyCloud’s recaptured darknet data in real time. On a match, the flow can be configured to automatically block access, force a credential reset, or route to MFA. The connector addresses compromised credentials from third-party breaches, infostealer malware, and phishing campaigns — threats that originate entirely outside the organization’s environment and that existing endpoint and identity tooling typically cannot detect.
A password reset addresses the specific credential that was exposed, but it doesn’t remediate the full scope of what an attacker may have already captured. Infostealer malware exfiltrates not just passwords but session cookies, authentication tokens, autofill data, and device fingerprints — data that can be used to hijack active sessions or bypass authentication entirely, even after a password has been reset. Additionally, if a user resets their password but chooses a credential that was independently compromised in a different breach or phishing campaign, the reset creates a false sense of remediation. SpyCloud’s integrations with Ping Identity continuously check credentials against a live dataset of recaptured darknet data, including data from breaches, malware logs, and phishing kits — so remediation reflects the actual current exposure, not just a single known event.
Dark web monitoring tools alert security teams after stolen credentials have already been posted to public dark web forums — at which point attackers have typically been exploiting the data for weeks or months. SpyCloud recaptures stolen identity data directly from criminal communities before it reaches public forums, providing a meaningful lead-time advantage. SpyCloud also captures data types that dark web monitoring misses entirely, including session cookies, authentication tokens, and infostealer malware logs. When embedded in Ping Identity flows via the DaVinci Connector or Auth Node, SpyCloud’s data enables automated, inline remediation at the moment of authentication — rather than generating an alert that requires a manual analyst response.
The SpyCloud integrations with PingOne DaVinci and PingOne Advanced Identity Cloud protect against the three primary sources of credential and identity exposure: data breaches that expose usernames and passwords from third-party services; infostealer malware infections that exfiltrate credentials, session cookies, and authentication tokens directly from infected devices; and phishing attacks, including AI-driven campaigns and Phishing-as-a-Service platforms, that capture credentials before victims realize they have clicked. SpyCloud recaptured 642.4 million exposed credentials from 13.2 million infostealer infections in 2025, along with 8.6 billion stolen cookies and session artifacts and 28.6 million phished identity records — all of which feed the recaptured dataset that Ping Identity flows check against at every authentication event.
No. Both integrations are designed for deployment without a development sprint. The SpyCloud DaVinci Connector is a drag-and-drop connector for PingOne DaVinci — IAM architects add it directly to existing flows and configure remediation logic through the DaVinci interface. The SpyCloud Auth Node is a native Journey Node for PingOne Advanced Identity Cloud and connects into the no-code Journey builder. Remediation responses — including MFA escalation, credential reset, access block, and fraud team alerting — are configuration decisions, not engineering projects.