After years of tracking the criminal underground, we can confidently state a universal truth: financially-motivated threat actors tend to focus on value. They want to derive the best return for the effort and money expended in their criminal activity.
In all of the activities we cover in this month’s cybercrime update, we see that value proposition at play – actors like TeamPCP, new LAPSUS$, and Scattered Lapsus$ ShinyHunters (SLSH) are increasingly removing the encryption from ransomware-style operations. Instead, they’re focusing on efficient data theft extortion centered around the compromise of cloud service accounts, which are often easier to access than corporations’ internal networks.
We also see this trend toward “efficiency” driving the continued lack of a dominant English-language criminal forum. Actors simply don’t rely on the forum ecosystem as much as they used to because chat apps have made it much easier to communicate. Telegram and other chat apps continue to supply a free, feature-rich, and relatively frictionless user experience for criminals looking to network.
With all that being said, in this cybercrime update, we cover:
- The recent exploits of TeamPCP – a group specializing in supply chain compromises of popular open-source tools
- Continued data-theft extortion campaigns by SLSH
- Another update in “the Forum Wars” – our name for the continued jockeying for a successor to BreachForums since it went dark in early 2025
So, let’s get into it!
TeamPCP continues to compromise supply chains and leak data
TeamPCP is a new threat actor responsible for multiple supply chain compromises against developers of widely-used open source packages. With their targeting of these packages, TeamPCP has been able to steal data, publish malicious versions of those packages, and then steal even more data from the victims. This in turn supplies them with more access to conduct further attacks.
Most recently, the group compromised the popular PyTorch Lightning Python package – pushing malicious versions of the package that then infected users with credential-stealing malware. The malware in question also has worm-like attributes – it gathers any GitHub tokens on the infected device, validates them using the GitHub API, and then pushes payloads to writable GitHub repositories. Malicious commits are named with the prefix EveryBoiWeBuildIsAWormyBoi. It also modifies local npm packages so that if a developer were to publish any npm packages from their infected device, those packages would also be infected with TeamPCP’s malware.
Data apparently related to these incidents continues to be released by multiple data theft extortion actors, and has so far been posted by LAPSUS$, VECT, and SLSH. This has led to public infighting between these groups, with accusations flying around of data theft and LARPing on Telegram and X. Additionally, at least one incident that appeared to follow TeamPCP’s modus operandi – the supply chain compromise of the Xinference PyPI package – was publicly rejected by TeamPCP as a copycat on X.
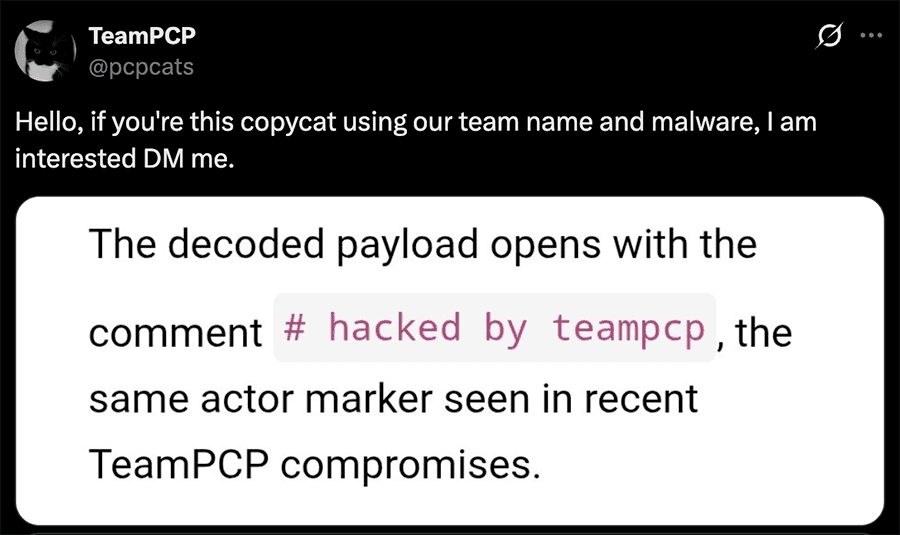
Post by @pcpcats on X alleging that the Xinference PyPI package compromise was the work of a different group. Screenshot courtesy of JFrog Security Research.
While TeamPCP’s exact allegiances remain unclear, their methodology is both extremely noisy and very effective. They take advantage of the inherent trust developers have in popular open-source software packages and efficiently leverage that access by infecting whatever they can reach downstream before they get noticed. When a new TeamPCP campaign does finally get noticed, it creates a frantic response by the entire InfoSec industry, as defenders must then collectively try to unwind package dependencies in their own environments to determine if they were affected. Not ideal for blue teams, but great for TeamPCP.
TeamPCP’s activity also underscores two major trends of increasing importance that we have observed developing in the identity security space:
- The growing targeting of non-human identities (NHIs): NHIs are credentials assigned to software applications, services, scripts, bots, or devices that authenticate and access resources without direct human involvement, such as GitHub tokens with write permissions. As password security for human users has gotten better (thanks to developments like 2FA) and while automation continues to become more prevalent, threat actors have started adapting to targeting NHIs more and more.
- Cybercriminal targeting of cloud services over internal network compromises: Cloud SaaS offerings are more and more widely used across enterprises, so much so that many organizations’ critical data is no longer stored on their internal networks, but is instead stored in a range of externally-managed cloud services. Therefore, if a cybercriminal can access a single cloud service account and steal a company’s most valuable data, why would they waste their time trying to access a well-protected corporate network, move laterally, escalate their privileges, and get access to the domain controller anymore? In the case of TeamPCP, even while they are able to infect endpoints en masse, they appear to really be after credentials for cloud services, particularly GitHub.
More data theft extortion by SLSH
ShinyHunters also continues to perpetrate data theft extortion against large organizations by targeting cloud services where their victims store critical data. Two of their most prominent breaches this month – that of the Udemy e-learning platform and the Vimeo video-sharing service – were both compromises of the organizations’ cloud service accounts. For Udemy, ShinyHunters appears to have compromised their Salesforce cloud CRM instance. For Vimeo, ShinyHunters appears to have accessed and stolen data from their Snowflake cloud database service.
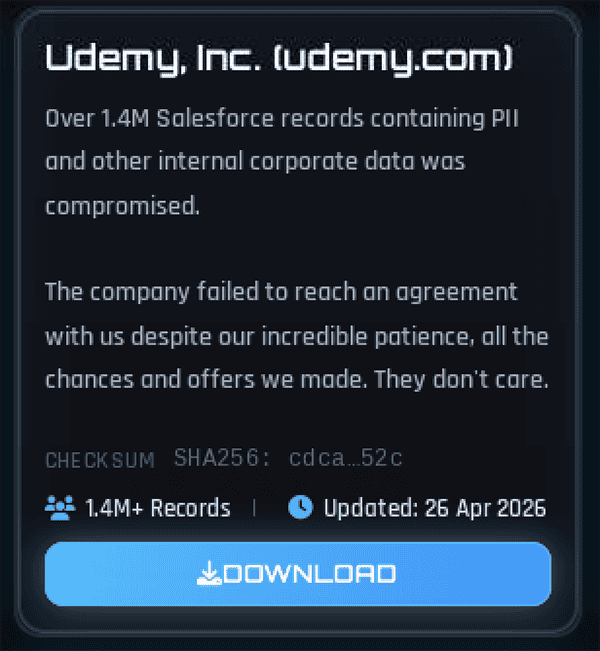
ShinyHunters’ post about their alleged breach of Udemy.
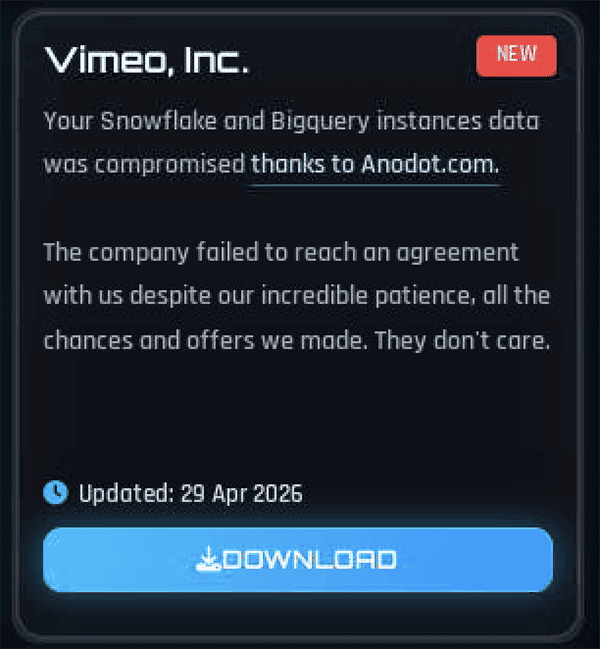
ShinyHunters’ post about their alleged breach of Vimeo.
This ShinyHunters data also appears to be frequently reposted across many of the English-language breach forums, both with and without credit to ShinyHunters as the source. This speaks to ShinyHunters’ success in generating buzz around these compromises – they are so successful in driving attention towards these breaches that other threat actors can generate clout for themselves by simply resharing the data on other platforms. It is sort of like when Taylor Swift announces her new album and then every major consumer-facing brand makes an instagram post with orange sparkles to try and hijack the news cycle (or sometimes referred to as “newsjacking”).
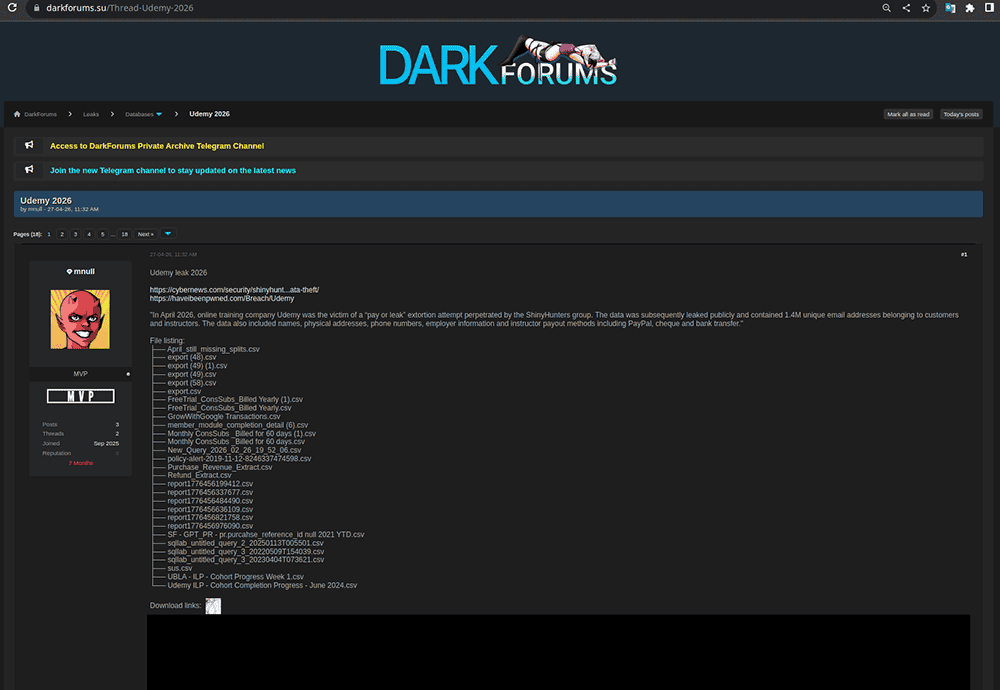
Example of an unrelated threat actor reposting ShinyHunters’ data to the Dark Forums data breach forum and crediting ShinyHunters as the original posters of the data.
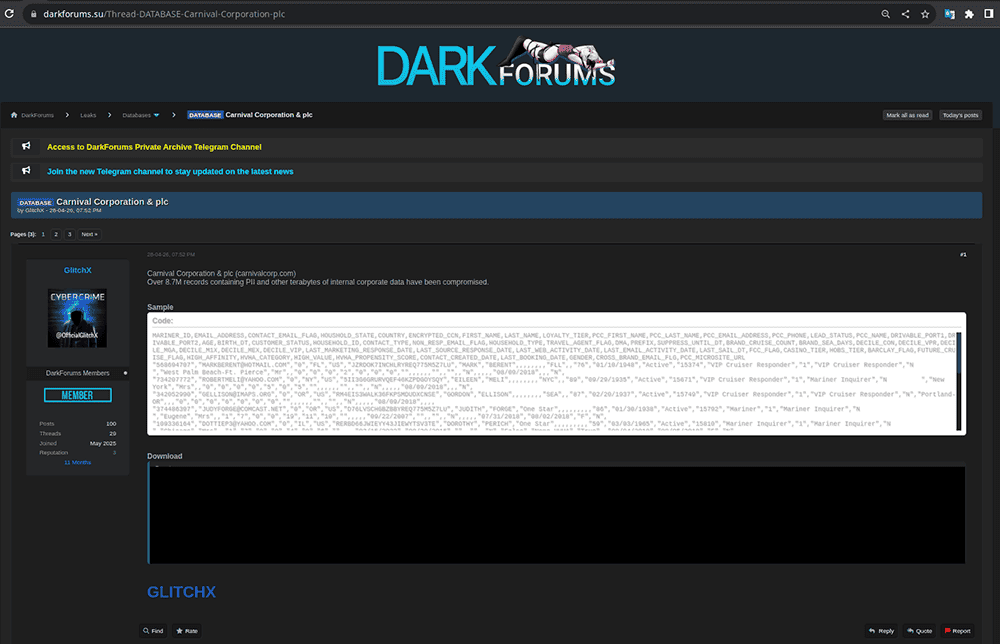
Example of an unrelated threat actor reposting ShinyHunters’ data to the Dark Forums data breach forum without ShinyHunters as the original posters of the data.
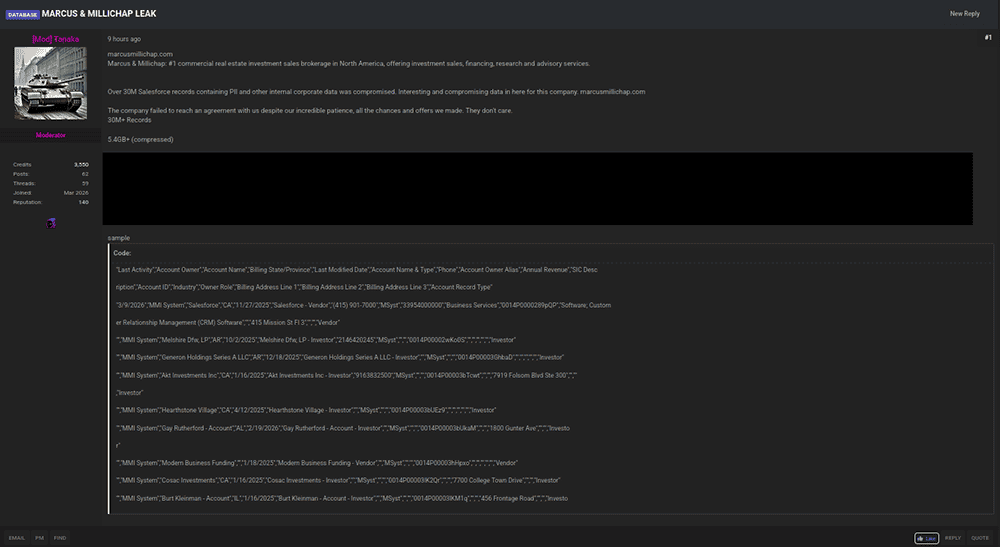
Another example of an unrelated threat actor reposting ShinyHunters’ without acknowledging ShinyHunters as the original posters of the data – this time on Spear Forums.
The Forum Wars: Now there’s a purple forum
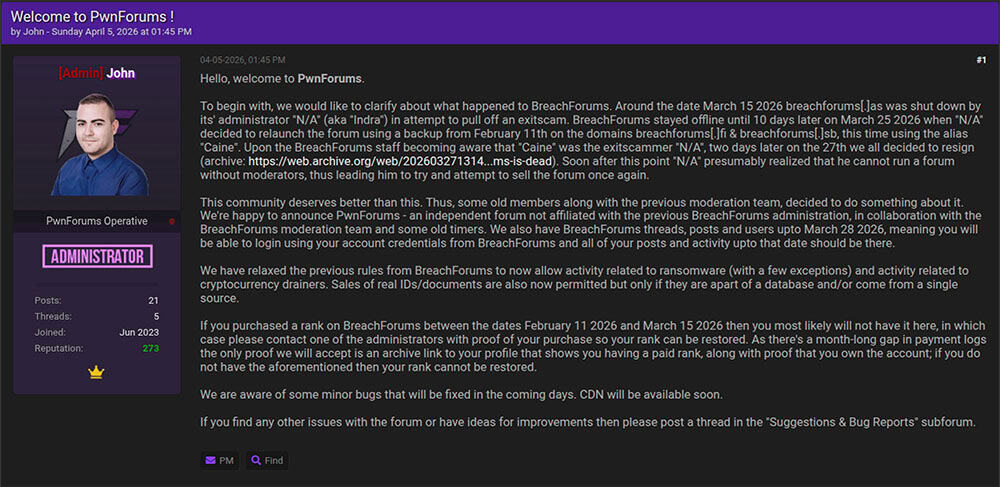
Opening announcement on PwnForums about the origins of the new site. The profile picture is a photo of the alleged real-life identity of the threat actor N/A, who was doxxed by other threat actors after attempting an exit scam with BreachForums.
It’s a lot to keep straight, and with so much changing so fast it’s sometimes confusing where a darknet forum post being shared on X or in the news even came from. To help our team quickly track down posts, we made the following chart of colors and user rank titles for the most prominent English-language breach forums that we are currently tracking. This ecosystem continues to rapidly evolve – and this chart will probably be out-of-date by tomorrow – but we are hoping it helps some other cybercrime researchers track down posts!
| Forums | Ranking Titles | Color |
| Hasan’s BreachForums | Citizen, VIP, MVP, Legend, IMMORTAL | Red |
| Other BreachForums | Member, VIP, MVP, GOD | Blue |
| Pwn Forums | Member, VIP, MVP, GOD | Purple |
| Dark Forums | Member, VIP, MVP, GOD | Blue |
| Spear Forums | Member, Insider, Hitter, Com Boss | Gray |
Colors and user rank titles from the most prominent currently active English-language data breach forums.



