Spring has finally sprung, although here at SpyCloud Labs we pretty much get all of our vitamin D from our laptop screens anyway. (Don’t worry, we know that screens don’t actually emit UV in the spectrum, but you get the point.)
In this month’s cybercrime update, we’re breaking down:
- The arrest of Chucky – the prolific owner of the LeakBase hacking forum
- The operation of ransomware-style DLS sites by both LAPSUS$ and ShinyHunters
- Iranian state-directed hacktivists targeting independent journalists and the FBI director
- And more!
Let’s dig into it.
LeakBase taken down again & Chucky arrested in Taganrog
As we wrote about last month, LeakBase – one of the most prominent data breach and hacking forums – was taken down by a coalition of international law enforcement agencies including the FBI and BKA in early March 2026. A couple of days later, the forum came back under a new domain leakbase[.]bz. Then, that new .bz domain was promptly seized by Russian law enforcement. This time – before the forum could be reconstituted on different infrastructure – the forum’s owner Chucky was arrested by the Russian Ministry of Internal Affairs (MVD) in Taganrog.
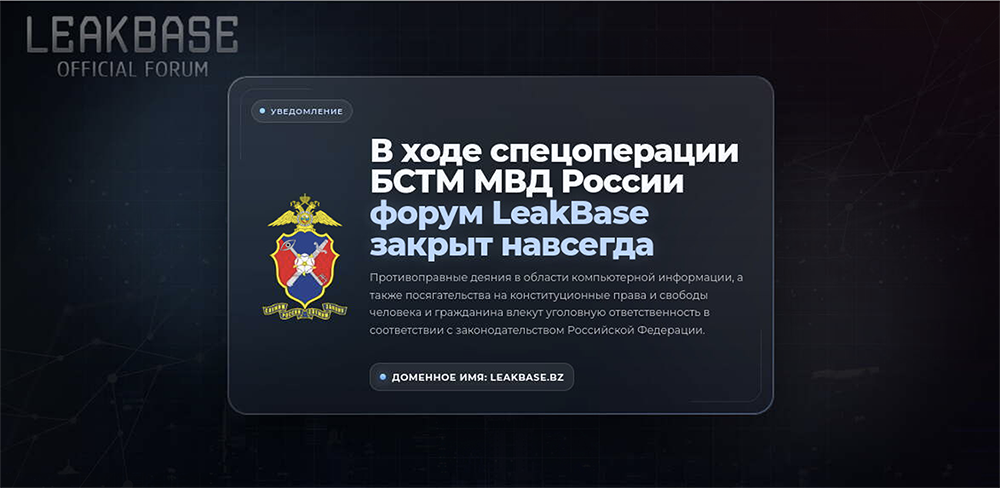
MVD splash page on the LeakBase website.
This development was somewhat surprising to us as Chucky has been operating out of Russia for many years. It’s an established norm that Russian authorities allow cybercriminals to operate with impunity against foreign targets as long as they refrain from hacking victims in Russia or Commonwealth of Independent States (CIS) countries, so it’s not immediately clear to us exactly which victim’s data was exposed to violate this rule and put him on MVD’s radar. However, it does seem like the reason he was arrested was definitely for breaking this norm – MVD spokesperson Irina Volk was quoted as saying “over 147,000 users registered on the [LeakBase] forum were able to buy and sell this [hacked] data, and even use it to commit fraud against [Russian] citizens.”
Discord RAT variant developer infects himself with malware
Many of the newer malware-as-a-service (MaaS) offerings, particularly amateurish, vibecoded MaaS offerings, use Telegram or Discord as a primary C2. We recently looked into one such MaaS offering in particular – Rafi’s Monitor Client, which is a modified Discord RAT that allows for basic computer control and token theft.
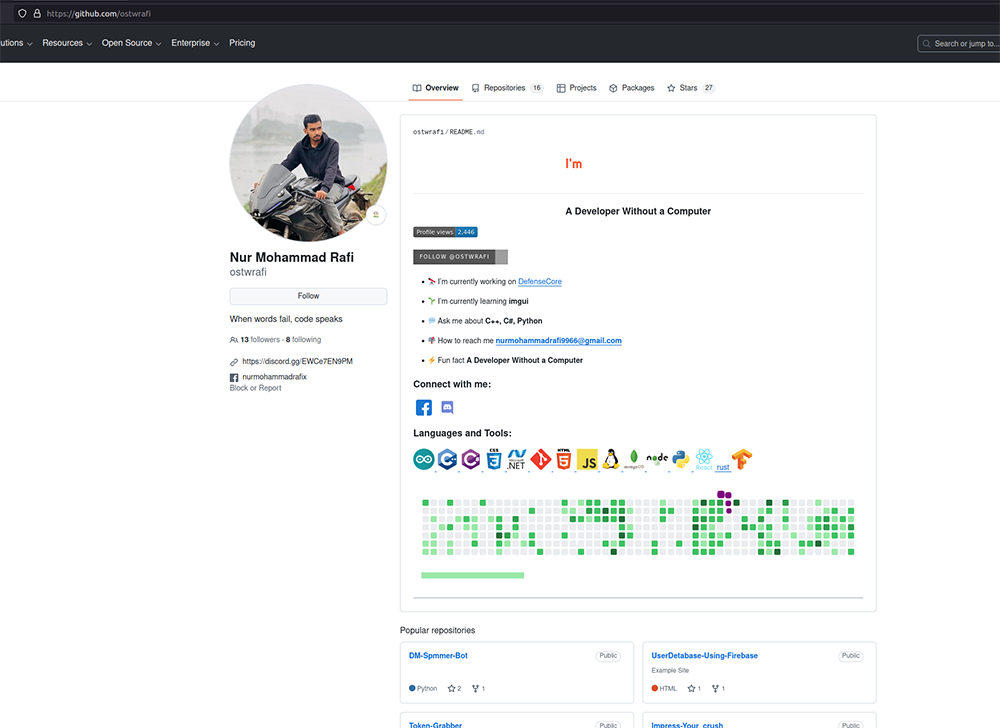
The developer, Rafi, offers this MaaS as well as other services like a Discord server nuking service that uses a modified NoMercy client. Rafi appears to have recently infected himself with infostealer malware, giving us some further insight into his identity and illicit service offerings.
The actor Rafi appears to be Nur Mohammad Rafi, a developer who lives in Bangladesh and uses the personal email addresses nurmohammadrafi9966[@]gmail[.]com, nurmohammadrafi[@]gmail[.]com, and rafipipuser[@]gmail[.]com. Pivoting on that first email address, we can also see that he appears to use the GitHub account ostwrafi, where he’s posted a photo of himself on a motorcycle and refers to himself as “a developer without a computer.”
Some of the public repositories on this profile include Discord “tools” that he states are intended for “educational purposes only.” These include a Discord token grabber that looks for tokens stored on a local machine and sends the stolen tokens to a webhook URL and a Discord “DM spammer bot.”
BreachForums update: The ‘clone wars’ continue
As we’ve reported on in past updates, there are currently two iterations of BreachForums fighting over which is the “real” BreachForums. Both sides are continuing to cast aspersions at one another; and both sites also keep going down and changing domains, making the whole situation difficult to keep straight.
While it originally had a shaky start, Hasan’s version of Breachforums, breached[.]st – which features light Nazi imagery – seems like it might be here to stay. Hasan has continued to publicly align his forum with Com-affiliated actors like the new data-theft extortion group calling themselves LAPSUS$ (although with no apparent connection to Arion Kurtaj’s original LAPSUS$ gang beyond shared values); and the form also features ads for vishing (phishing-over-voice call) tools popular with that community of threat actors.
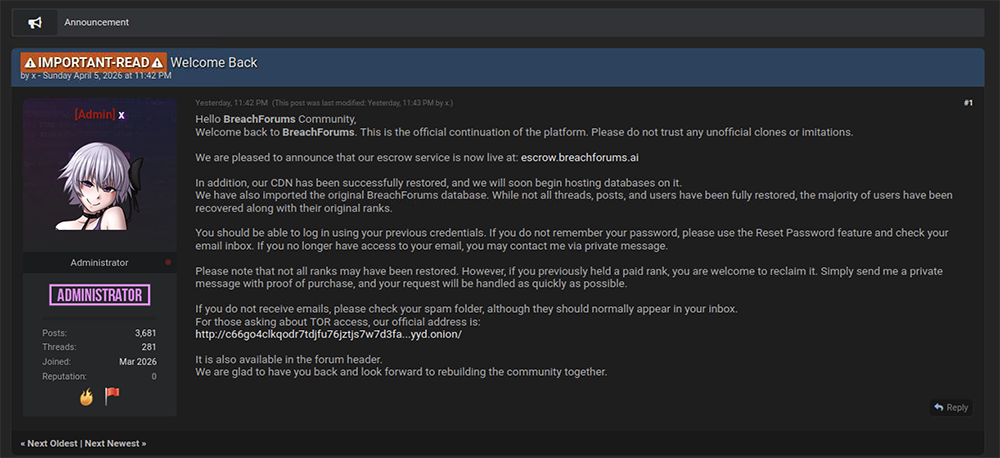
The other BreachForums, which is apparently associated with some of the moderators and admins of the former BreachForums (which went dark in April 2025), appears to have gone through multiple domain changes just in the last month, from a .as domain, to a .ac domain, to a .sb as well as a .fi domain and finally to its current .ai domain.

X post regarding the sale of BreachForums being announced in a Telegram group.
Sometime between March 10 and March 15 of this year, the real Indra came back and attempted to regain control and kick out N/A. Ultimately, a power struggle ensued and eventually led to Indra giving up and claiming that the forum was dead on or around March 16 as shown in the picture below.
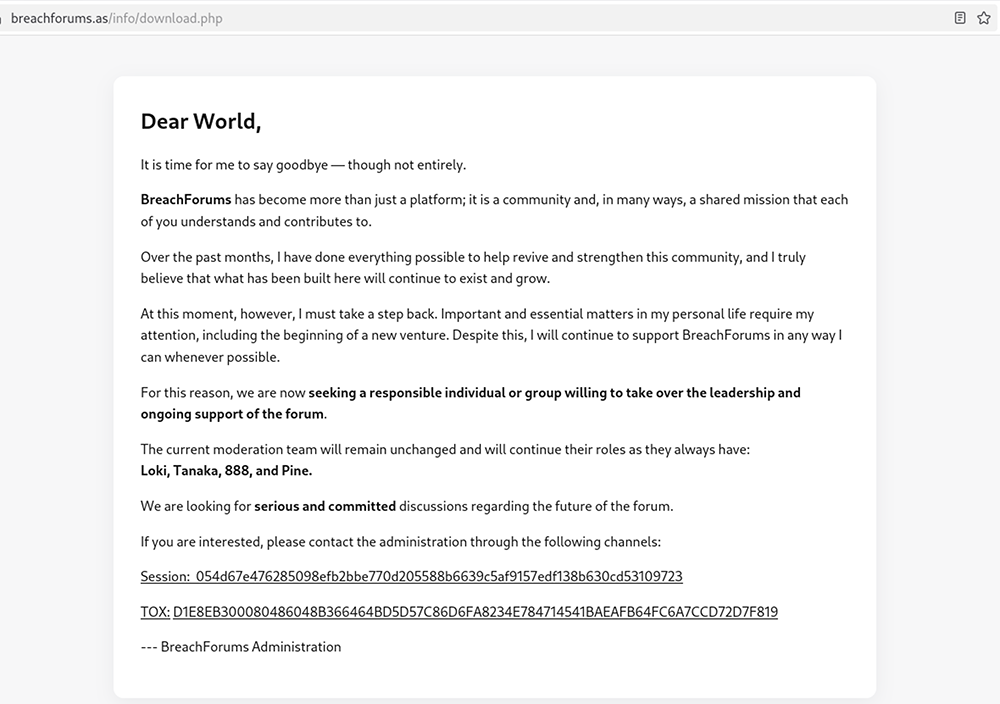
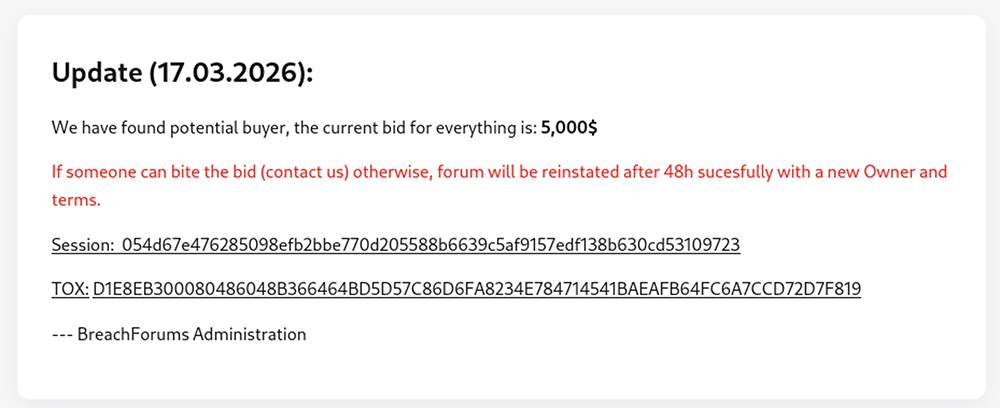
N/A continued to attempt to sell the forum during this time and resorted to controlling old accounts of former admins or members of the community such as Caine as well as creating two new domains breachforums[.]sb and breachforums[.]fi. Shown below is one of the posts on .sb during this timeframe:
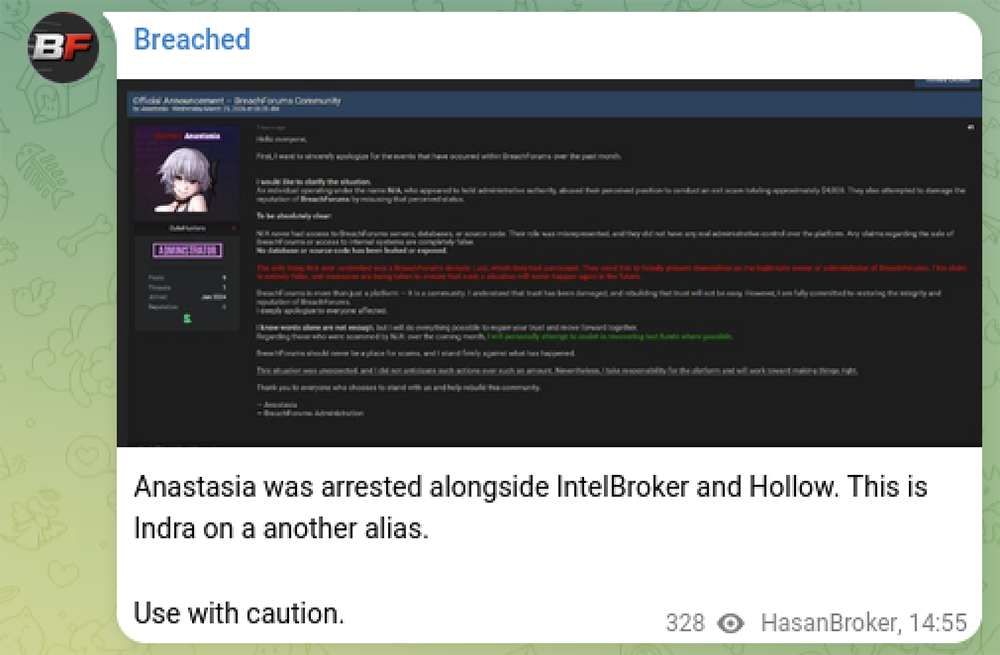
On March 25, Anastasia allegedly made a post on the current N/A-controlled domain, breachforums[.]ac,about the N/A situation, apologizing for their behavior and telling users that N/A only ever had access to the domain, but not the backend data of BreachForums. However, Hasan quickly pointed out that the person behind the Anastasia moniker was allegedly one of the BreachForums administrators arrested in early 2025, and he accused Indra of making posts under Anastasia’s name.
It should also be noted that it’s unclear who has been controlling the “Indra” accounts at various times throughout this saga, and whether (or when) “Indra” has been controlled by the same individual as the “N/A” account.
At the current time the lineage of this BreachForums version is at the [.]ai top level domain. This site is sparsely populated but heavily promoted on Telegram channels. We believe this version of BreachForums to be some sort of scam given the channels that are promoting it.
LAPSUS$ and ShinyHunters
As we covered late last year, a Com-affiliated data-theft extortion group calling themselves ShinyHunters has been operating a data leak site (DLS) – a term for the websites maintained by ransomware and other data-theft extortion gangs where they post threats and leak victim data.
ShinyHunters remains active and has also recently begun working with TeamPCP, a group that has caused issues recently because of a series of supply chain compromises against popular open source tools including Aqua Security’s Trivy tool, multiple GitHub action workflows maintained by Checkmarx, and multiple popular PyPI and npm packages. In these attacks, TeamPCP uses compromised open source developer credentials to change the source code for these open source tools and packages, turning them into credential-stealing malware.
The successful supply chain compromise of Trivy – an open source scanner tool used by many organizations to help with attack-surface management – also resulted in the compromise of multiple high-profile organizations including Cisco and the European Commission. Both organizations were subsequently claimed on the ShinyHunters DLS, and on March 28, ShinyHunters leaked over 90GB of data exfiltrated from the European Commission’s compromised AWS account.

Another group calling themselves LAPSUS$ (which, as previously mentioned, has no apparent connection to Arion Kurtaj’s original LAPSUS$ gang beyond shared values) has also created a DLS and begun posting large breaches from major companies. Thus far, this new LAPSUS$ gang has posted data from multiple newsworthy victims, including a major pharmaceutical company and an AI-based talent recruiting tool. In some cases, they have only posted samples of exfiltrated data from their attacks and are attempting to sell the full datasets to the highest bidder, which is a less common tactic for a data-theft extortion actor. They have even devoted a section of their DLS to “Exclusive Auctions // Private Sales” for these private sales of breached data.
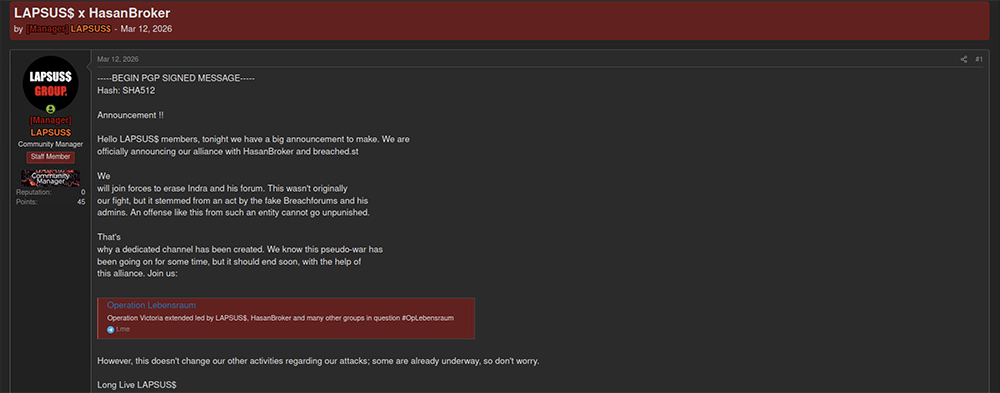
Interestingly, this new LAPSUS$ group appears to be aligned with Hasan in the aforementioned fight between dueling BreachForums successors. LAPSUS$ is active on Hasan’s version of BreachForums in that their account is listed as a staff member on the forum and they have been observed cross-posting breaches to the site.
In a post on March 12, they announced a formal alliance with Hasan, stating that they intend to “join forces to erase Indra and his forum.” They are calling this alliance against Indra’s BreachForums “Operation Lebensraum” – a reference to the core Nazi ideological goal of territorial expansion. Of note, the Vect ransomware group also announced a partnership with Hasan’s BreachForums and TeamPCP around the same time period, but it’s unclear whether any of Vect’s data came from TeamPCP.
Iranian ‘Handala’ hacktivist group attacks Iranian press
In their latest attack, the Iranian Handala hacking group targeted their own country’s free press. Handala Hack Team is ostensibly a pro-Iranian hacktivist group that is generally considered to actually be operating at the direction of the Iranian Ministry of Intelligence and Security (MOIS).
Throughout March, these Iranian state-sponsored hackers have engaged Israel and the US in a handful of cyber skirmishes, often under a thin veil of hacktivism. These include their claims of hacking:
- The personal email account of FBI Director Kash Patel
- Verifone Point-of-Sale devices across the United States
- The website of the independent Iranian press outlet IranWire
- The phone of an IDF employee
- Private correspondence of the Prime Minister of Israel Benjamin Netanyahu
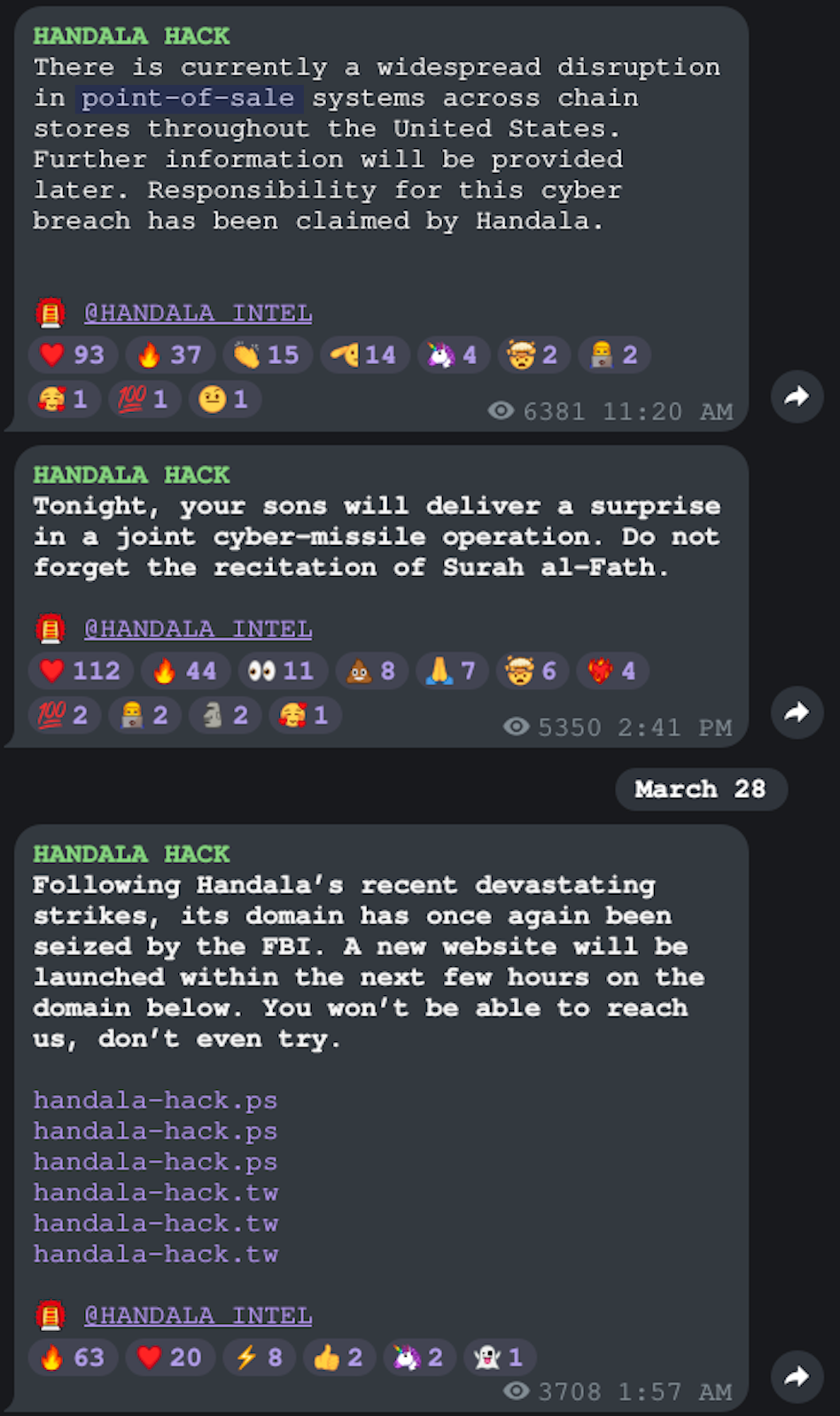
Posts in the Handala Telegram channel from March 2026.
FBI Director Kash Patel’s personal emails
In perhaps their boldest release to date, the group leaked a tranche of emails they claimed to have stolen from the personal email account of current FBI director Kash Patel. The FBI corroborated the authenticity of this hacked-and-leaked data, noting that the data was “historical in nature and involves no government information.”
The data does appear to have been exfiltrated from a personal gmail account used by Kash Patel. In our quick analysis of the 324 released emails spanning 2010 to 2022, we can see:
- Evidence of Kash’s entrepreneurial activities during the early part of his legal career, including commodities trading he was apparently involved in around the 2010-2011 time frame.
- Emails regarding Kash’s relocation to Washington, D.C. around 2013 to work for the DOJ.
- Handala also made sure to include embarrassing photos of Patel from the early 2010s, indicating operational goals of psychological intimidation and embarrassment.
Another interesting detail present in the sample emails: Patel knows sugar. The FBI director’s father worked for Kakira Sugar in Uganda and the leaked emails show that Kash was very engaged in trading sugar around 2010.
Verifone Point-of-Sale devices
Handala also claimed to have hacked Point-of-Sale devices “across chain stores throughout the United States.” Later reporting challenged whether their presumed DDoS attacks were even successful, with Verifone denying any impact to their networks or operations in public statements and journalists and cybersecurity experts unable to find any evidence of impacted operations.
IranWire
In the last week of March, Handala turned their attention closer to home; they targeted the independent Iranian press website IranWire.
IranWire is an independent journalistic outlet that was launched in response to a period of censorship and repression in Iran almost two decades ago. In 2009, the Iranian government held a general election with dubious outcomes. The popular candidate lost by a landslide and the legitimacy of the results were questioned. The grassroots movement of the losing party – and the subsequent populist backlash to election fraud – came to be known as the Green Movement, the Persian Spring, or the Persian Awakening. From this movement eventually arose press outlets like the IranWire, a journalistic outlet for independent citizen-led reporting.
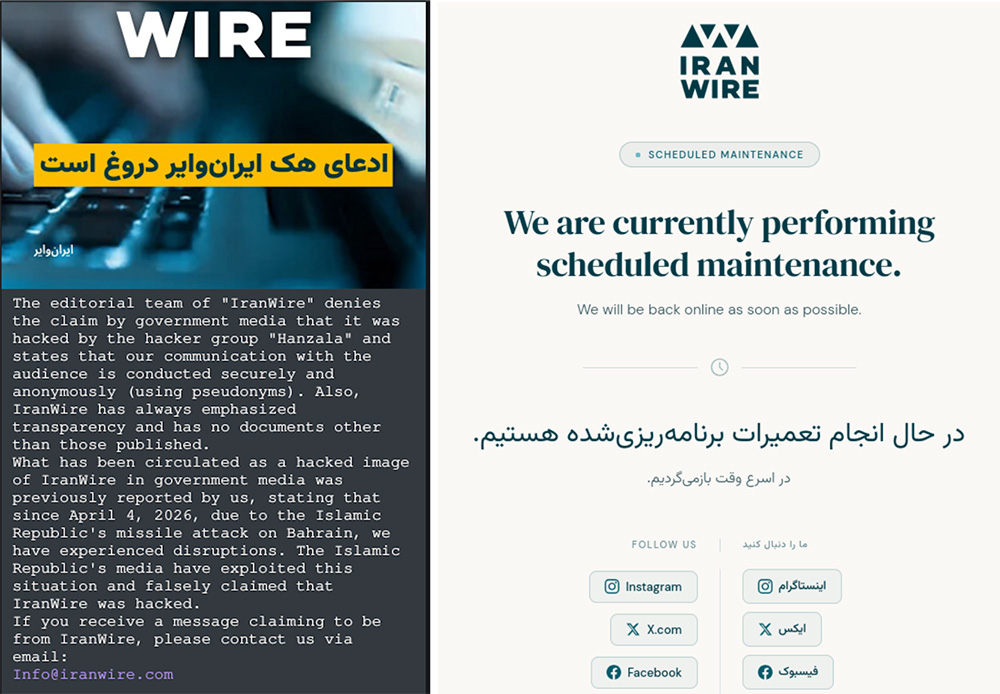
Now in 2026 – under the context of increased escalations brought on by coordinated elimination of Iran’s leadership – Handala targeted IranWire’s website and social accounts. IranWire’s Telegram channel subsequently denied the claims that they had been hacked. However, their website did go down around the time of Handala’s claims, citing “scheduled maintenance” as the reason for the service outage.
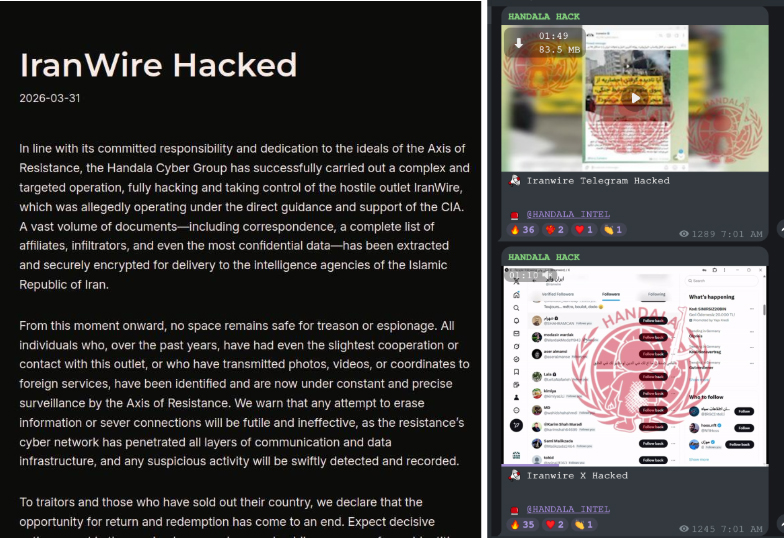
Handala blog post (left) claims to have hacked IranWire, with videos suggesting that they had gained control of the journalistic outlet’s social media accounts (right).
New research and insights from SpyCloud
Security teams are hyperaware of how flooded the threat landscape is with exposed identity data. Our just-released annual Identity Exposure Report reveals that cybercriminals had access to 5.3 billion newly-exposed credential pairs, 8.6 billion stolen session cookies, and at least 1.1 million master passwords to password vaults.
Another sobering finding: 49% of phishing victims last year were corporate users, making it clear that more high-risk exposures are happening within the enterprise environment than most of us would like to think.
If you haven’t yet, do check out the full report – and if helpful, benchmark your defenses with our Identity Threat Protection Maturity Model – here (no form fill required).