Put SpyCloud data to work where it matters most, to you – leveraging our diverse offering of out-of-the-box integrations to scale detection, remediation, and incident response workflows for seamless protection of exposed employee, supplier, and consumer identities.




SpyCloud integrates with popular identity access providers like Active Directory, Entra ID, Okta, and Ping Identity to continuously monitor for and identify compromised session tokens and credentials, allowing you to remediate identity exposures in as little as 5 minutes from discovery.


SpyCloud integrations with EDR tools like Crowdstrike Falcon and Microsoft Defender help you automate key steps to detect and respond to infostealer malware infections.

SpyCloud integrations with SOAR platforms like Palo Alto Cortex XSOAR, Tines, and Microsoft Sentinel come with ready-to-use incident response playbooks and curated intelligence. This means you can quickly and easily tackle identity-related exposure incidents.

SpyCloud integrations with SIEM tools like Splunk, Elastic, Google Chronicle, and Microsoft Sentinel help you prioritize alerts and take fast action to protect your employees.
Combine SpyCloud-normalized OSINT with other valuable third-party data in a single repository. Gain better insight into the threats facing your organization and exponentially increase the accuracy and speed of investigations.
See how to integrate SpyCloud’s recaptured identity data within your existing security workflows.
SpyCloud’s API integrations work with leading technology vendors, delivering identity protection at scale to prevent targeted cyberattacks.
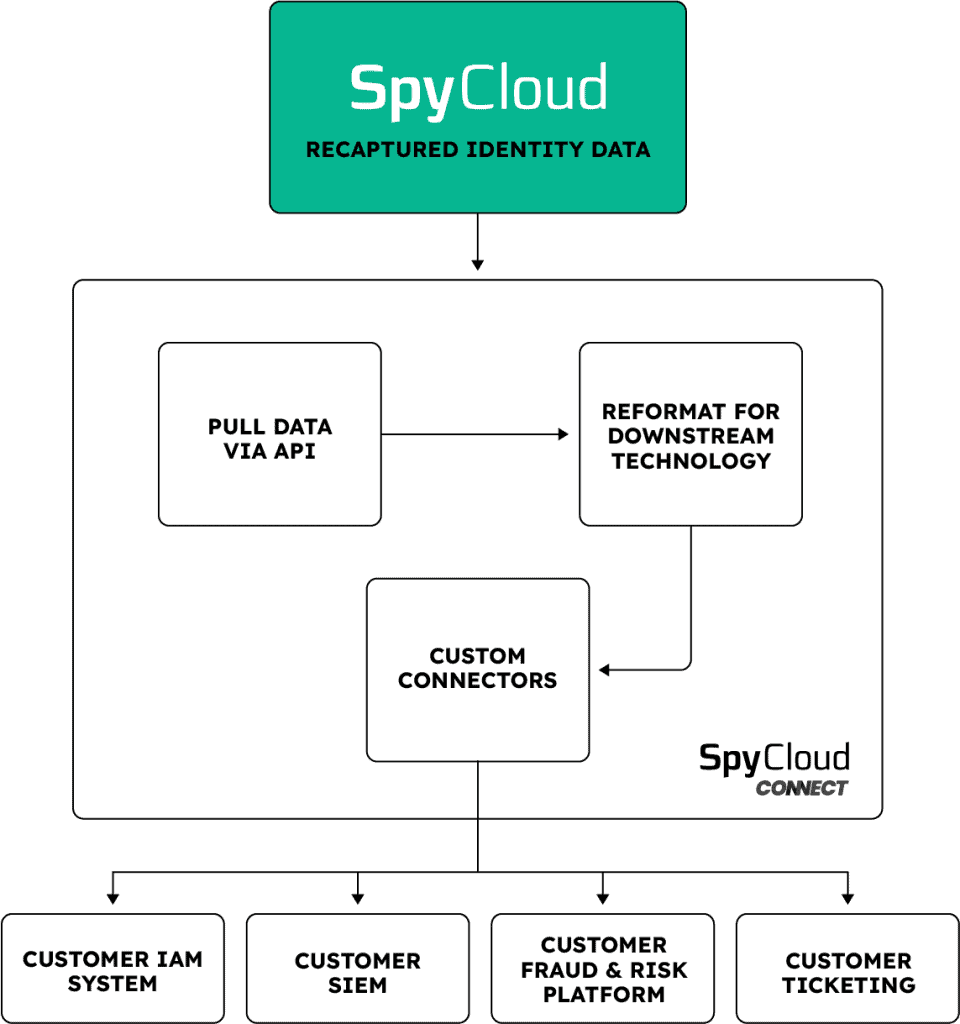
SpyCloud Connect is a hosted custom automation solution that allows SpyCloud products to be seamlessly integrated with a wide variety of security tools and processes – enabling rapid remediation and scalable automation of compromised identities within a customer’s preferred tech stack.
Whatever you want, whenever you want it – SpyCloud Connect builds out the workflows for your desired integrations to send SpyCloud data where and when you need it, all in the tools you are using today without needing to burden your existing resources with custom development work.
Optimize your team’s workflows with SpyCloud’s powerful recaptured malware, phished, combolist, and breach data
SpyCloud integrates with Splunk, Elastic SIEM, Google Chronicle (Google SecOps), Microsoft Sentinel, and Devo. These integrations deliver SpyCloud’s recaptured breach records, infostealer malware logs, and phishing capture data as enrichment signals, improving event correlation and helping analysts prioritize identity-related alerts. Security teams can correlate SpyCloud exposure data with authentication events, endpoint alerts, and access logs in the same SIEM workflow they already use, without building custom data pipelines.
SpyCloud integrates with Palo Alto Cortex XSOAR, Tines, Swimlane, and Microsoft Sentinel (which supports both SIEM and SOAR functions). These integrations come with ready-to-use incident response playbooks and curated intelligence that let security teams automate response to identity-related exposure incidents. Common automated workflows include triggering password resets for employees with confirmed credential exposures, creating high-priority tickets for malware-infected users, and escalating sessions with stolen cookie exposure for immediate revocation.
SpyCloud integrates with CrowdStrike Falcon and Microsoft Defender for Endpoint to help security teams detect and respond to infostealer malware infections that bypass traditional endpoint detection. SpyCloud’s integration surfaces high-fidelity alerts about malware-infected devices and exfiltrated identity data, including the specific credential counts, cookie counts, and application access data stolen from each infected device. This gives EDR-focused teams definitive evidence of what was compromised so they can execute a full post-infection response.
SpyCloud integrates with Active Directory, Microsoft Entra ID, Okta Workforce Identity, and Ping Identity to continuously monitor for and automatically remediate compromised employee credentials and session cookies. When SpyCloud detects that an employee’s credentials appear in recaptured darknet data, it triggers an automated password reset or session revocation directly in the identity provider within 5 minutes of discovery, without manual analyst intervention. SpyCloud is available in the Okta Integration Network, making deployment straightforward for organizations already using Okta.
Yes. SpyCloud integrates with Maltego through more than 80 pre-built Maltego transforms, enabling CTI analysts and investigators to pivot directly into SpyCloud’s recaptured darknet identity dataset from within their existing Maltego investigation workflows. SpyCloud also offers pre-built Jupyter Notebooks that deliver query results in a format designed for drill-downs, data exports, and custom analytical workflows. These integrations are designed for threat intelligence teams and incident responders who need to combine SpyCloud data with other OSINT sources in a single investigation environment.