Top Takeaways from the 2026 Verizon Data Breach Investigations Report
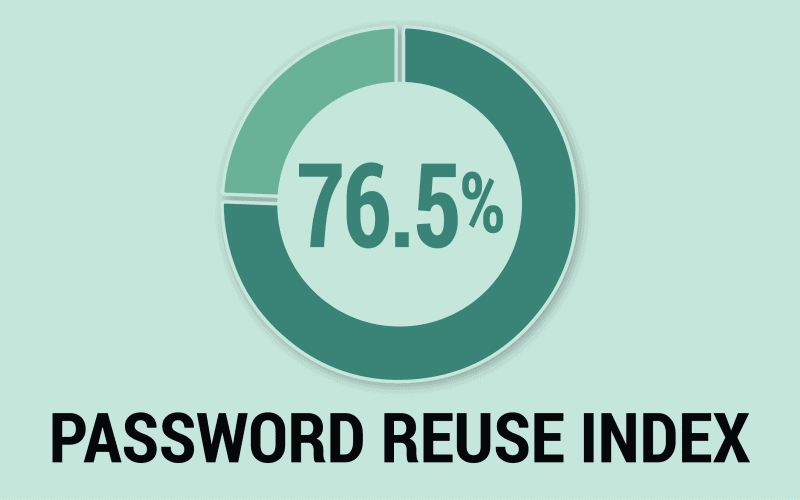
The 2026 Verizon DBIR is the largest breach dataset ever analyzed – and the findings hit close to home for identity security teams. SpyCloud unpacks the numbers that matter most: why stolen credentials still drive nearly 4 in 10 breaches, how infostealers are fueling ransomware, and why MFA alone can’t protect the sessions attackers are already stealing.