Your vendors have access to your systems, your data, and sometimes your customers. When their security fails, the breach lands on your doorstep.
…Not ideal.
Third-party risk management (TPRM) tools help organizations assess, monitor, and reduce the risk posed by third-party vendors – before a compromised vendor becomes a compromised you. As supply chain attacks continue to rise, companies are investing in TPRM and related platforms to gain continuous visibility into vendors’ security posture.
But vendor risk has never been broader, or more complex. According to a recent survey, regulatory compliance and cyber risk are now the top drivers of TPRM strategies, a clear signal that acknowledges a necessary focus on cybersecurity.
And the survey showed that investment is now concentrated mostly on technology and tools, with a spike in budget and spend dedicated to cybersecurity and data protection (49%). The question is whether the tools teams are buying can address the threats that are generating the most risk.
This guide compares the top third-party risk management platforms, breaks down the features that matter, and explains why traditional tools often miss one of the biggest drivers of risk: stolen vendor, partner, and contractor identity data circulating on the darknet.
What are some of the top third-party risk management software options?
Top third-party risk management tools in 2026 include platforms like SpyCloud, as well as UpGuard, SecurityScorecard, Bitsight, OneTrust, and Panorays. Each offers automated vendor assessments, monitoring, and risk rating dashboards that help organizations track the security posture of their third-party vendors.
Third-party risk management software centralizes the work of assessing, monitoring, and mitigating risks that come from working with external vendors. The logic is simple: your vendors often have access to your systems, data, or networks, and their security gaps can quickly become your security gaps. A compromised vendor credential or a malware-infected device at a third party can open a direct path into your environment.
TPRM platforms typically handle four core functions:
- Risk assessment: Evaluate a vendor's security posture before onboarding and throughout the relationship
- Continuous monitoring: Track changes in vendor risk profiles across a variety of signals to indicate higher or lower risk levels
- Compliance tracking: Verify that vendors meet regulatory and contractual requirements like SOC 2, ISO 27001, or GDPR
- Remediation workflows: Coordinate responses when vendor risks surface, ensuring issues actually get resolved
Quick comparison: Third-party risk management tools at a glance
- Best for security ratings: SecurityScorecard, Bitsight
- Best for compliance automation: Vanta, Drata
- Best for GRC integration: OneTrust, ProcessUnity
- Best for identity exposure detection: SpyCloud
Top third-party risk management tools compared
The third-party risk management market includes a range of platforms, each with different strengths. Some focus heavily on external security ratings, while others emphasize questionnaire automation or compliance workflows. Here’s a quick comparison of the leading options:
| Tool | Primary Focus | Best For |
| UpGuard | Attack surface monitoring | Blending security ratings with questionnaire automation |
| SecurityScorecard | Security ratings | Continuous monitoring with high-level scores |
| Bitsight | Enterprise security ratings | Board-level reporting and cyber risk quantification |
| OneTrust | GRC and privacy compliance | Vendor risk integration into broader GRC programs |
| Panorays | Supply chain collaboration | Collaborative risk remediation with vendors |
| Prevalent | Full-lifecycle vendor risk | Managed services and vendor risk |
| RiskRecon | Observed security behaviors | Evidence-based analysis of vendor security hygiene |
| ProcessUnity | Workflow-driven GRC | Customizable assessment and remediation workflows |
| Vanta | Compliance automation | Compliance management and vendor risk |
| Drata | Continuous compliance | Integrated compliance monitoring with vendor risk |
| Black Kite | Ransomware susceptibility | Specific threat analysis like ransomware risk |
| SpyCloud | Identity intelligence | Continuous detection of compromised vendor and application credentials from malware infections, breaches, combolists, and phishing attacks |
UpGuard
UpGuard combines external attack surface monitoring with automated vendor questionnaires. The platform scans publicly visible infrastructure while also providing a structured way to collect self-reported information from vendors. It’s particularly useful if you want both an outside-in view of vendor security and a way to manage questionnaire workflows in one place.
SecurityScorecard
SecurityScorecard provides A-F security ratings based on externally observable data like DNS health, patching cadence, and network security. The letter-grade format makes it easy to communicate vendor risk to non-technical stakeholders, and the platform excels at continuous monitoring across large vendor portfolios.
Bitsight
Bitsight targets large enterprises with a focus on cyber risk quantification, which means translating security findings into financial terms that resonate with boards and executives. The platform also offers extensive peer benchmarking, so you can see how your vendors compare to industry averages.
OneTrust
OneTrust positions vendor risk management within its broader governance, risk, and compliance (GRC) platform. If you’re already managing privacy, ethics, or other compliance functions in OneTrust, adding vendor risk keeps everything in one system.
Panorays
Panorays emphasizes collaboration between organizations and their vendors. The platform combines external ratings with internal assessments and provides workflows that help both parties work together on remediation rather than just flagging issues.
Prevalent
Prevalent offers a mix of software and managed services, meaning they can handle vendor assessments on your behalf. This approach works well for organizations that lack the internal resources to manage a large vendor portfolio or want to offload the assessment workload.
RiskRecon
RiskRecon, owned by Mastercard, provides risk assessments based on observed security behaviors. Rather than relying solely on questionnaire responses, the platform delivers detailed, evidence-based insights into how vendors actually manage their security.
ProcessUnity
ProcessUnity focuses on workflow automation for complex GRC and vendor risk processes. The platform is highly customizable, making it suitable for enterprises with specific assessment and remediation requirements that don’t fit neatly into out-of-the-box solutions.
Vanta
Vanta automates evidence collection for compliance frameworks like SOC 2 and ISO 27001, with vendor risk management built in. It’s popular among fast-growing tech companies that want to manage compliance and vendor risk together without adding headcount.
Drata
Drata provides continuous compliance automation with an integrated third-party risk module. The platform emphasizes ongoing monitoring rather than periodic assessments, which helps maintain compliance posture between audits.
Black Kite
Black Kite offers risk ratings alongside a Ransomware Susceptibility Index, providing specific threat analysis that goes beyond general security scores.
SpyCloud’s Supply Chain Threat Protection
Many vendor risk management tools rely on questionnaires, infrastructure scans, and point-in-time security scores – assessments that are often outdated before the ink dries. They can tell you how a vendor’s external attack surface looks on paper, but they can’t tell you if an attacker already has valid credentials they can use to walk right through your front door.
SpyCloud Supply Chain Threat Protection takes a fundamentally different approach, securing your supply chain at the identity layer. By continuously analyzing recaptured breach data, infostealer malware logs, phishing exposures, and credential combolists tied to your vendor ecosystem, SpyCloud reveals whether vendor employees, devices, or shared application access have already been compromised, so you can act before attackers can pivot into your environment.
All of this intelligence is delivered through a centralized dashboard that tracks exposure trends across your entire vendor portfolio, measuring each vendor via a comprehensive threat index based on the frequency, recency, and severity of their exposures over time.
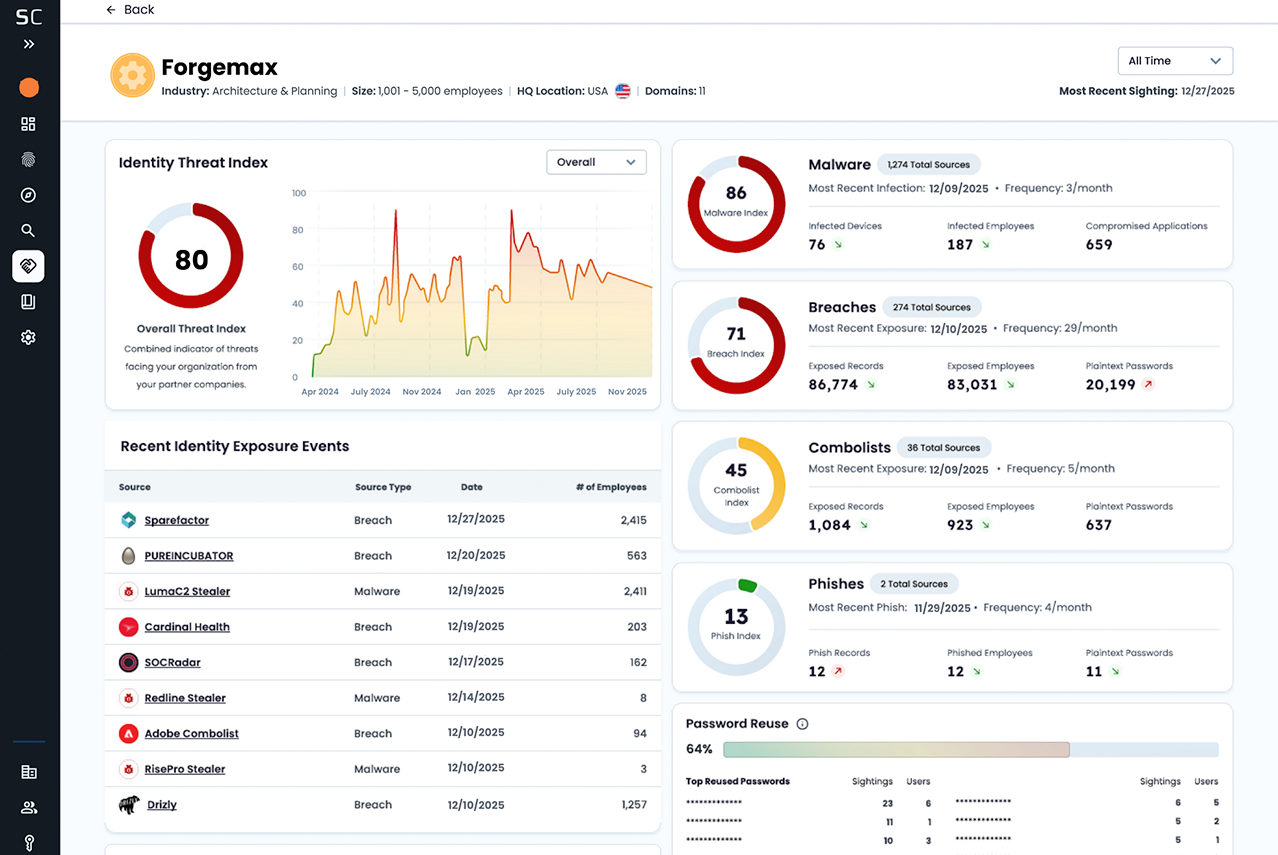
SpyCloud signals are built on data science weighted by volume, source, and severity of compromise – helping you prioritize threats with meaningful context. View what your risk is right now, or segment by exposure type and timeframe for tracking whether a third party’s security hygiene is improving or degrading over time.
The result is a shift from best-guess assessments to evidence-based, continuously updated risk intelligence, giving your team the early warning and collaborative remediation tools needed to stop supply chain threats at their source, not after a breach.
Essential features of third-party risk management software
When evaluating platforms, look for capabilities that match your organization’s specific needs and maturity level.
Automated risk assessment and scoring
Platforms automatically calculate risk scores based on external scans, questionnaire responses, and threat intelligence. Automation is essential for scaling assessments across hundreds or thousands of vendors and partners without overwhelming your team with manual work.
Continuous monitoring and real-time alerts
Point-in-time assessments quickly become outdated. A vendor’s security posture can change the day after you complete an annual review. Continuous monitoring provides ongoing visibility and alerts you when something changes, whether that’s a new vulnerability, a configuration drift, or a breach disclosure.
Compliance management and framework support
The best platforms map vendor controls to common frameworks like SOC 2, ISO 27001, GDPR, and HIPAA. This simplifies compliance reporting and helps verify that vendors meet your regulatory requirements without requiring you to manually cross-reference controls.
Security questionnaire automation
Sending, tracking, and analyzing vendor questionnaires manually is time-consuming. Automation streamlines the process and often includes pre-built questionnaire templates aligned with industry standards like SIG and CAIQ.
Vendor onboarding and offboarding workflows
Lifecycle management creates a structured process from initial assessment through contract termination. Consistent evaluation at onboarding catches risks early, while proper offboarding ensures data removal and access revocation when relationships end.
Risk remediation and task management
When risks surface, you want tools to track issues, assign tasks, and coordinate responses. Some platforms enable direct collaboration with vendors, while others focus on internal workflow management.
Reporting and analytics dashboards
Dashboards provide executive-level views of vendor risk, trend analysis, and portfolio-level insights. Clear reporting helps communicate risk to stakeholders who don’t live in the details of vendor assessments.
Integration with SIEM, SOAR, and GRC tools
A platform’s ability to fit into your existing security stack matters. Look for integrations with your SIEM, SOAR, identity provider, and other GRC tools to make sure data flows where it’s most useful to your teams rather than sitting in a silo.
How to choose the best third-party risk management platform
Selecting the right platform depends on several factors specific to your organization:
- Vendor portfolio size: Some platforms scale better for thousands of vendors, while others work best for a smaller number of critical third parties.
- Industry and compliance requirements: Certain tools specialize in specific regulatory frameworks like HIPAA for healthcare or PCI DSS for financial services.
- Existing security stack: Evaluate API integrations with your current tools to avoid creating data silos.
- Assessment methodology: Determine whether you prefer external security ratings, internal questionnaires, or a combination of both.
- Remediation capabilities: Consider whether you want collaborative workflows to work directly with vendors on fixing issues.
- Identity exposure visibility: Evaluate whether the platform detects compromised vendor credentials, a threat category that security ratings typically miss.
What traditional third-party risk tools miss (& why identity intelligence matters for your vendor risk program)
Traditional TPRM tools focus on security ratings and questionnaires, but they often miss a critical attack vector: identity exposures. Here’s what typically gets overlooked:
- Stolen credentials: Vendor employees often reuse passwords across personal and work accounts. A breach on any site can expose credentials used to access your systems.
- Malware infections: Infostealer malware on vendor devices captures authentication data, including passwords and session cookies, for your shared applications.
- Phished credentials: Vendor staff targeted by phishing campaigns can unknowingly provide attackers with valid access credentials.
- Compromised applications: Internal and third-party shared applications exposed on malware-infected vendor devices.
- Stolen session cookies: Stolen session cookies allow attackers to impersonate authenticated vendor users without needing a password, bypassing MFA entirely via session hijacking attacks.
Vendor employees with stolen credentials or malware-infected devices represent a direct path into your environment, and infrastructure scans don’t reveal whether your contractor’s password is already for sale on the darknet.
SpyCloud Supply Chain Threat Protection monitors for vendor credentials and authentication data exposed in breaches, malware infections, and phishing attacks. Teams can also securely share data and reports with vendors so they can remediate their own exposures quickly. This identity-layer visibility complements traditional security ratings by revealing whether vendor employees have already been compromised, not just whether their infrastructure looks secure.
How to implement a third-party risk management program
Building an effective program involves several key steps.
01
Define vendor risk criteria and tiering
Establish a tiering system based on factors like data access, system connectivity, and business criticality. Not all vendors carry the same risk, and your assessment depth can vary accordingly. A vendor with access to customer PII warrants more scrutiny than one that only provides office supplies.
02
Inventory and categorize existing vendors, partners, and contractors
Create a complete inventory of all third-party vendors. Many organizations underestimate their total vendor count, so achieving full visibility is a critical first step before you can assess risk.
03
Conduct initial risk assessments
Perform baseline assessments on all vendors using your selected tools and methodologies, prioritizing by risk tier. High-risk vendors get deeper assessments, while lower-tier vendors might only need basic screening.
04
Establish continuous monitoring processes
Move beyond point-in-time assessments to ongoing visibility. Continuous monitoring includes tracking infrastructure changes as well as identity exposures like stolen credentials that surface between formal reviews.
05
Create remediation workflows and escalation paths
Define clear procedures for responding when vendor risks surface. This includes internal escalation paths and communication protocols for working with vendors to resolve issues before they become incidents.
Proactive third-party risk management starts with identity exposure visibility
Modern, comprehensive vendor risk management requires visibility into identity exposures. Traditional tools answer the question, “How secure is this vendor’s infrastructure?” but miss the more urgent question, “Have this vendor’s employees already been compromised?”
SpyCloud Supply Chain Threat Protection closes this gap by monitoring for vendor credentials and authentication data exposed in breaches, malware infections, and phishing attacks.
See how SpyCloud illuminates hidden vendor threats
FAQs about third-party risk management tools
Specialized platforms like SpyCloud collect recaptured data directly from breaches, malware-infected devices, and phishing kits. They then match this data against vendor domains and employee identities to flag specific exposures that affect your supply chain.
Security ratings assess a vendor’s external infrastructure posture, things like server configurations and certificate management. Identity intelligence reveals whether vendor credentials and authentication data have already been stolen and are available to attackers.
Yes, some platforms enable secure, direct data sharing so vendors can validate and remediate their own exposures without lengthy back-and-forth communication or insecure email exchanges.
Implementation timelines vary based on vendor portfolio size and integration needs. Cloud-based tools can deploy in days, while complex enterprise deployments with custom integrations may take several weeks.
Vendor risk management (VRM) software is a category of cybersecurity tools designed to assess, monitor, and reduce the risks introduced by third-party vendors. These platforms help organizations evaluate a vendor’s security posture, track ongoing risk signals, ensure regulatory compliance, and manage remediation workflows. Modern VRM tools combine external security ratings, automated questionnaires, and continuous monitoring to provide visibility across the vendor lifecycle. More advanced platforms also detect vendor identity exposures — such as stolen credentials or malware infections — that traditional infrastructure assessments may miss.
Some platforms extend monitoring to your vendors’ vendors by analyzing dependencies. However, the depth of fourth-party visibility varies significantly across different tools, and most organizations focus first on direct third-party relationships.