February was a short month, but a lot happened in the cybercrime underground. In this latest intelligence and news update, we’re breaking down the developments, including:
- The coordinated takedown of Tycoon 2FA, a prolific PhaaS kit
- New happenings in the criminal hacking forum ecosystem including the merger of two vishing forums, a law enforcement disruption of LeakBase, and the launch of a Kurdish hacker forum
- A data leak from IDMerit, an identity data provider used in KYC processes
- Doxxers going after the developers of the GhostSocks proxy malware
Keep reading for what you should know.
Tycoon 2FA phishing takedown
Tycoon 2FA (Storm-1747) emerged in August 2023 as a sophisticated Phishing-as-a-Service (PhaaS) kit that gives phishers the ability to intercept login sessions in real time, serving as a powerful example of industrialization and specialization in the cybercrime ecosystem. By proxying legitimate Microsoft 365 and Google Workspace login pages, Tycoon 2FA captures credentials, MFA inputs, and session cookies, allowing attackers to bypass MFA and hijack accounts.
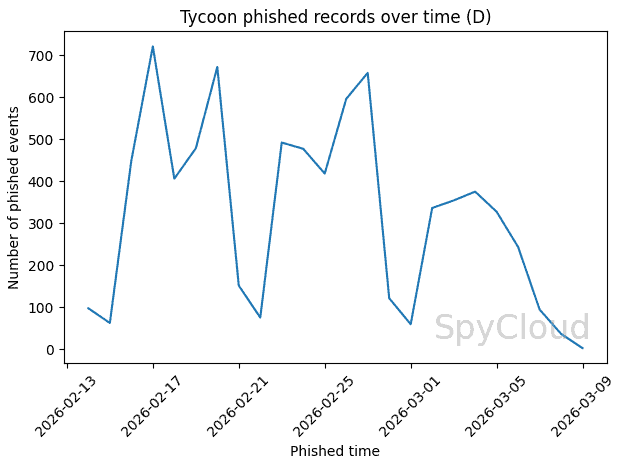
Over the last three years, Tycoon 2FA became one of the most prolific PhaaS kits on the market. In our recaptured data, SpyCloud identified 328,865 victim records exposed through administrative panels, including 173,000+ unique email addresses and 264,000 passwords.
Our analysis also shows that approximately 80% of victim email addresses were tied to enterprise-managed domains, underscoring the kit’s targeted focus on business environments.
In the first week of March 2026, a coordinated action led by Europol and Microsoft, with support from SpyCloud and other private sector partners, disrupted the infrastructure supporting Tycoon 2FA.

Splash page that appeared on disrupted Tycoon 2FA panel domains after the takedown actions.
So yes, it’s true – sustained public-private collaboration can materially reduce criminal capability and shift the economics of cybercrime in favor of defenders. Full recap here.
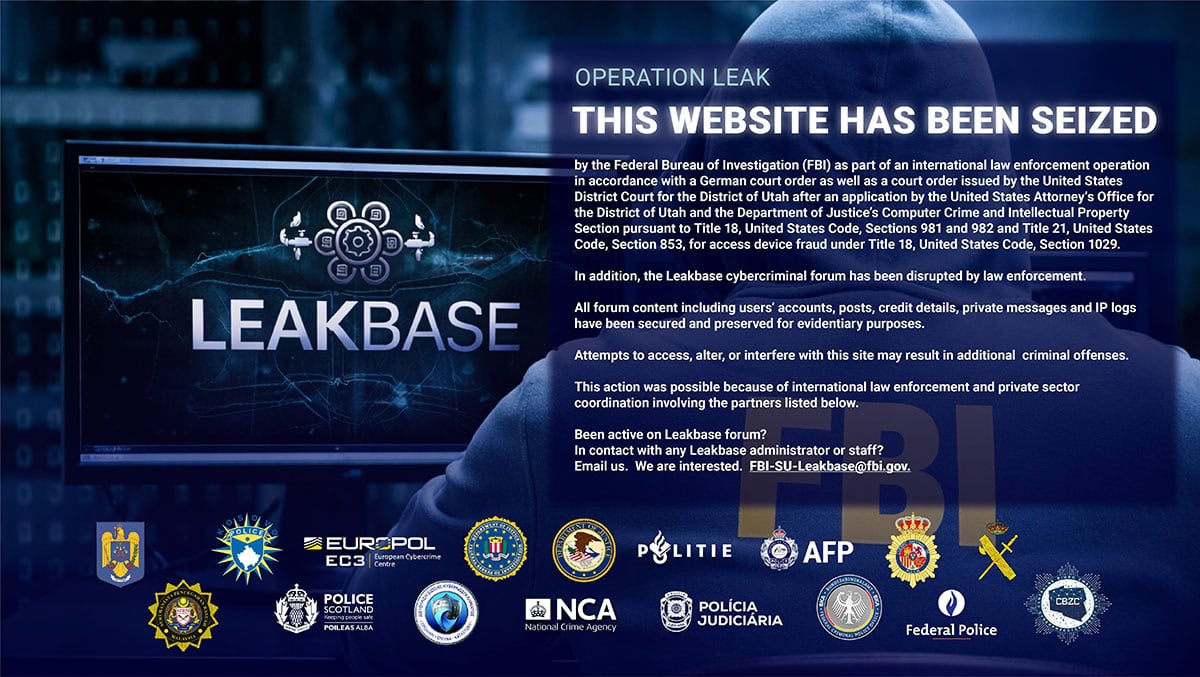
LeakBase domain seizure
Operation Red Card 2.0 & a major blow to fraud activity in Africa
In other positive news, Interpol’s Operation Red Card 2.0 resulted in 651 arrests across 16 African countries in February, recovering more than $4.3 million USD and exposing scams linked to over $45 million USD in financial losses. The operation – supported by the World Economic Forum’s Cybercrime Atlas – targeted high-yield investment scams, mobile money fraud, and fraudulent mobile loan applications, with tactics ranging from phishing and identity theft, to social engineering and fake digital asset schemes.
This is the kind of coordinated disruption that Cybercrime Atlas was built to enable. As a founding partner, SpyCloud has contributed recaptured darknet intelligence, investigative tradecraft, and tooling to the initiative – supporting threat actor hunts and research working groups that expose cybercriminal networks and guide strategic disruption efforts. Operation Red Card 2.0 adds to a track record that includes Operations Serengeti I and II and the Euroboss takedown.
‘Kurdistan Hackers Forums’ launches
In late January, a new regionally-focused Kurdish hacking forum was launched under the name “Kurdistan Hackers Forums.” General forum details appear in both English and Sorani Kurdish, and posts to the forum are in a mixture of both languages.
The forum follows the same general structure of other large hacking forums like BreachForums or Exploit, with different sections devoted to familiar topics like hacking, combolists, cracked accounts, leaked databases and hosting/VPS services. Much of the data, tutorials, and tools are globally relevant. However, there is definitely a particular Middle Eastern regional focus – many of the top posts in the leaked databases section share breached data from Middle Eastern countries like Iraq, Turkey, Israel, Pakistan, and Syria.
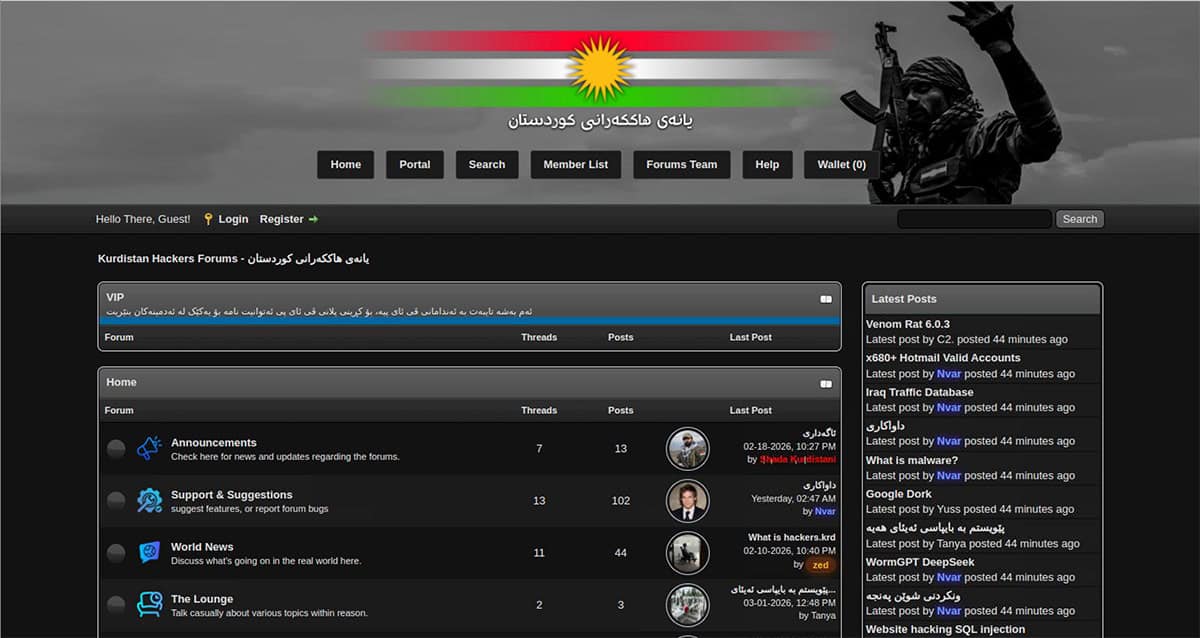
Homepage of the Kurdistan Hackers Forums website.

X post by Cyb3r_Drag0nz promoting the new Kurdistan Hackers forum.
Hacktivists threaten a “Cyber Holocaust” amid tensions in the Middle East
As kinetic conflict in Iran has risen following a US-Israel operation that killed Iranian senior leadership, hacktivist groups appear to be capitalizing on the situation in their public messaging. Anonymous-themed hacktivist groups claiming to be from Bangladesh and Russia have leveraged anti-semitic rhetoric, promising a “Cyber Holocaust” – a term they are apparently using to describe their general targeting of Israel’s digital presence. A pro-Russian hacktivist group titled Russian Legion purported to have hacked Israel Defense Forces (IDF) infrastructure, revealing financial information about various IDF projects, with a message directly from the “commander-in-chief” shared in the channel.

Post from Russian Legion on Telegram claiming that they hacked secret IDF documents as part of their “cyber operation ‘Holocaust’”.
While this intense rhetoric and numerous recent announcements of alliances between Russian and Islamic hacktivists appear directly tied to recent events, this isn’t the first time for either:
- The same Holocaust language was used by the Anonymous collective in 2015, as part of #OpIsrael – Anonymous has been prominently outspoken against Netanyahu’s increased aggression in Gaza.
- Additionally, 21st century Russian-speaking and Islamic hacktivists have long shared a common boogeyman in “The West,” a bloc which (in their conception) includes Israel as well as NATO countries. Announcements of similar alliances have been ongoing, especially throughout the Israeli-Palestinian conflict.
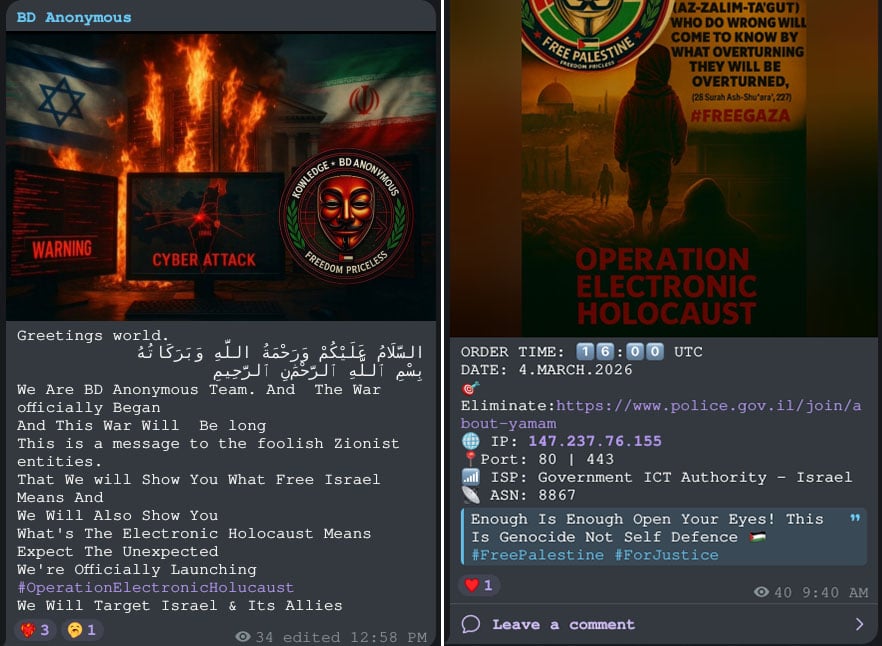
Recent Telegram post by Bangladesh Anonymous announcing an “Electronic Holocaust” in the wake of US and Israeli strikes on Iran.
While these alliances might initially seem unusual, Russian and Islamic cultures are actually fairly intermingled, with many regions in Russia having large Muslim populations. Additionally, Russia’s neighbors Kazakhstan and Uzbekistan also contain significant populations that are both Muslim and Russian-speaking. This shared cultural context and a common vision of “The West” make these alliances not particularly surprising, even considering the recent Russian aggression in Ukraine.
Recent hot conflict in Iran doesn’t change the story much for Middle Eastern hacktivist groups or their international alliances. The leadership of these groups are simply capitalizing on the current situation and using strong rhetoric to inspire their ranks and recruit more DDoSers. Many of these lower-sophistication hacktivist groups rely on individual participation to facilitate their DDoS attacks – encouraging volunteers to install software on their devices in order to add them to their botnets and launch attacks. Therefore, DDoS hacktivist groups in particular tend to capitalize on current events to continuously recruit more volunteers as a prerequisite to launching effective DDoS attacks.
Shortly after the Bangladesh Anonymous post about the war beginning and announcing an “Electronic Holocaust,” they quickly returned to their boilerplate #FreePalestine tags in their channel. Similar motions to capitalize on the situation and engage with the current conflict have also been observed among other Middle Eastern hacktivist groups.
IDMerit data leaked
Last month, Cybernews reported that a large MongoDB instance, reportedly associated with IDMerit – described by Cybernews as “an AI-powered digital identity verification solutions provider” – was left exposed.
When contacted, IDMerit told Cybernews that, following a review, they were unable to identify any “exposure, vulnerability, or unauthorized access within the IDMERIT environment.” However, they noted that “certain data ports associated with independent data sources could have been open, which had the potential to expose certain databases.”
SpyCloud has acquired a dataset that appears to match the data described by Cybernews, based on publicly available reporting. The dataset in SpyCloud’s possession is consistent with MongoDB formatting and was acquired from IP address 103.215.159.140. According to historical DNS resolution data, the domains wapi-fd3.idmerit[.]com and serv701702.idmerit[.]com resolved to this IP address during the period referenced by Cybernews.
The database was taken offline shortly after Cybernews contacted IDMerit to notify them of the exposure.
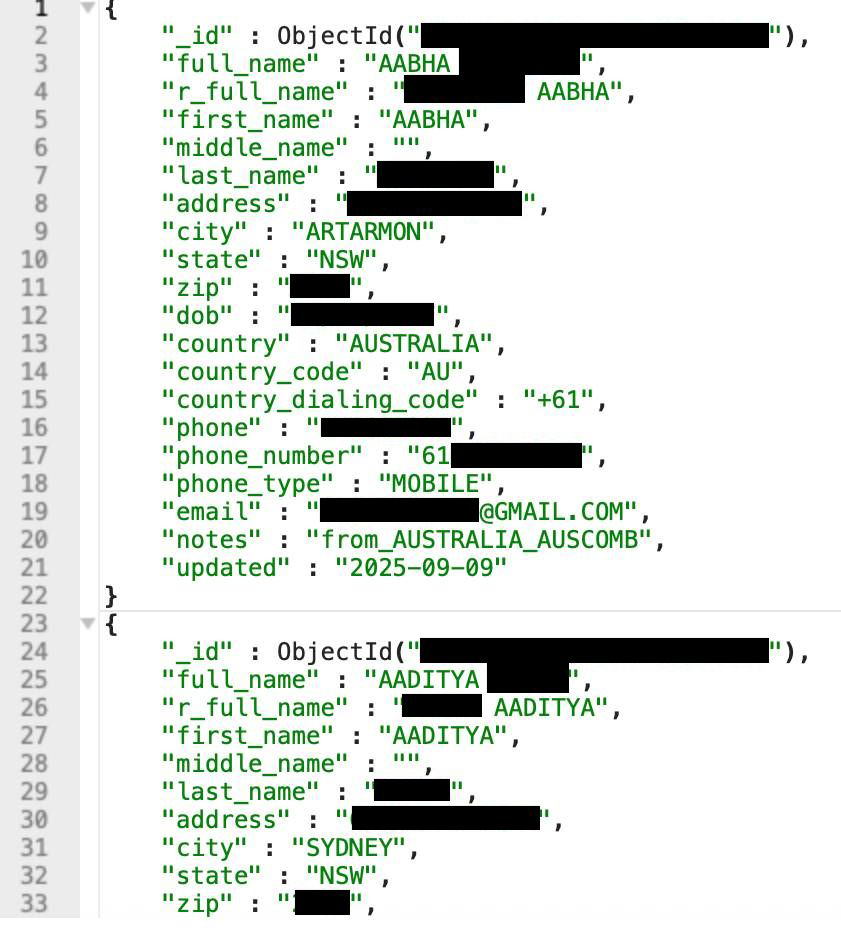
Sample of the leaked data. Image by Cybernews.
An analysis of the data by country shows that Mexico is the most commonly represented country, with 191,555,379 records indicating an address in the country. It is followed by the United States (103,460,415), Italy (65,311,889), Spain (63,489,130), and Brazil (45,426,796).
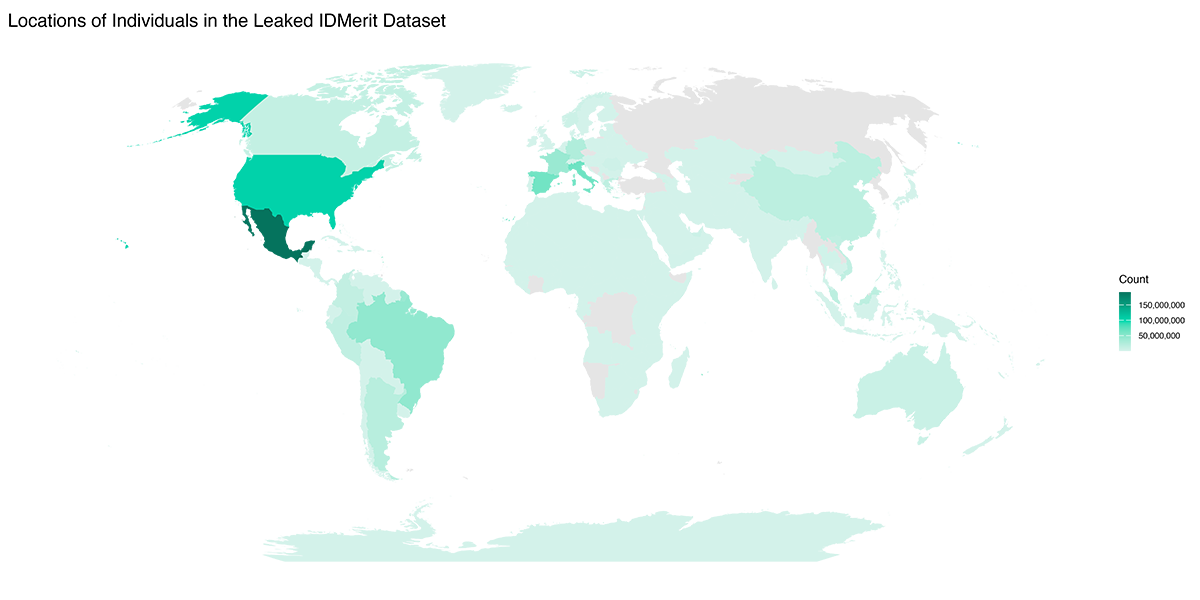
Number of records per country represented in the leaked dataset.
The dataset also contains:
- 875,115,348 full names
- 542,911,579 phone numbers
- 537,193,581 physical or mailing addresses
- 310,150,231 dates of birth
- 122,562,608 national ID numbers
- 65,603,815 email addresses
- 45,642,516 tax identification numbers
- 22 other fields
Com-affiliated vishing forums merge
In other news, CallForums and Spear Forums – two smaller criminal forums that focus on vishing (phishing over voice call) and both claim affiliation with the Com – have merged.
The Com, short for “The Community,” is a loosely affiliated subculture of criminal hackers mostly in their teens and early 20s, from primarily Western countries like the US, UK, and Canada. This subculture is linked to both coordinated violent harassment (e.g. the 764 violent extremist group), as well as cybercriminal hacking and corporate extortion campaigns (e.g. the Scattered LAPSUS$ Hunters group which regularly conducts vishing, criminal hacking, and corporate extortion).
Com-affiliated cybercriminal actors are known in particular for using sophisticated vishing techniques as an initial access vector to compromise networks.
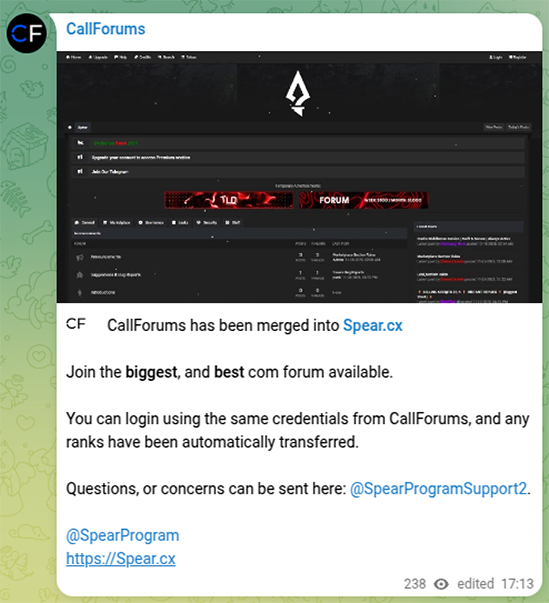
Message on the CallForums Telegram channel announcing their merger with Spear Forums.
Message on the official Spear Forums Telegram channel announcing their merger with CallForums.
In January 2026, both CallForums and Spear Forums announced the merger on their respective Telegram channels, promising CallForums users that any account upgrades they purchased would be automatically moved over to Spear Forums. The CallForums domain now redirects visitors to the Spear Forums domain.
Posts on Spear Forums include a variety of databases, tools, and services for sale, with an emphasis on vishing, smishing (phishing over SMS), and cryptocurrency platforms (both breached user/customer data as well as strategies to bypass KYC).
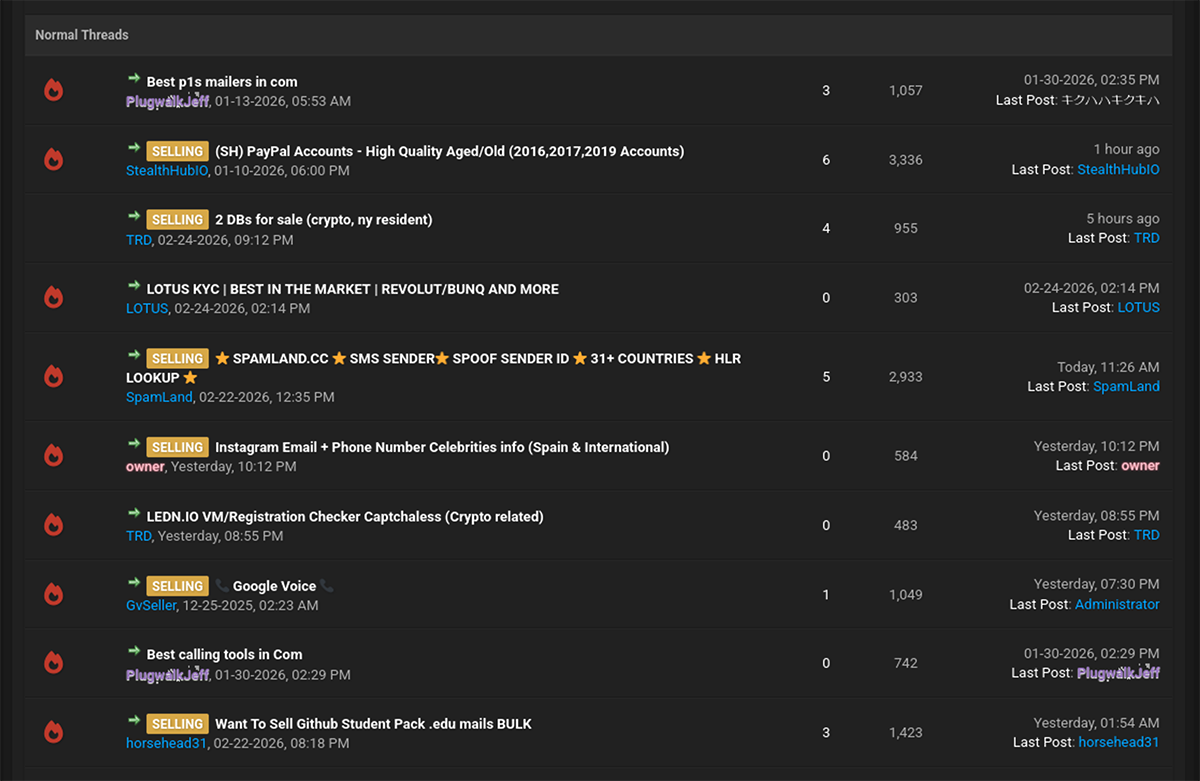
Screenshot of the “Seller’s Place” section of Spear Forums showing data and tools for sale.
One popular topic is “Press 1” calls (often abbreviated as P1); this is a common type of vishing scam in which victims are told that one of their financial accounts is having an urgent issue, and that they need to “press 1” to speak to a representative and resolve it. At that point, the victim is connected to a scammer who socially engineers them into giving up sensitive account information.
Breach of Chinese National Supercomputing Center (NSCC)
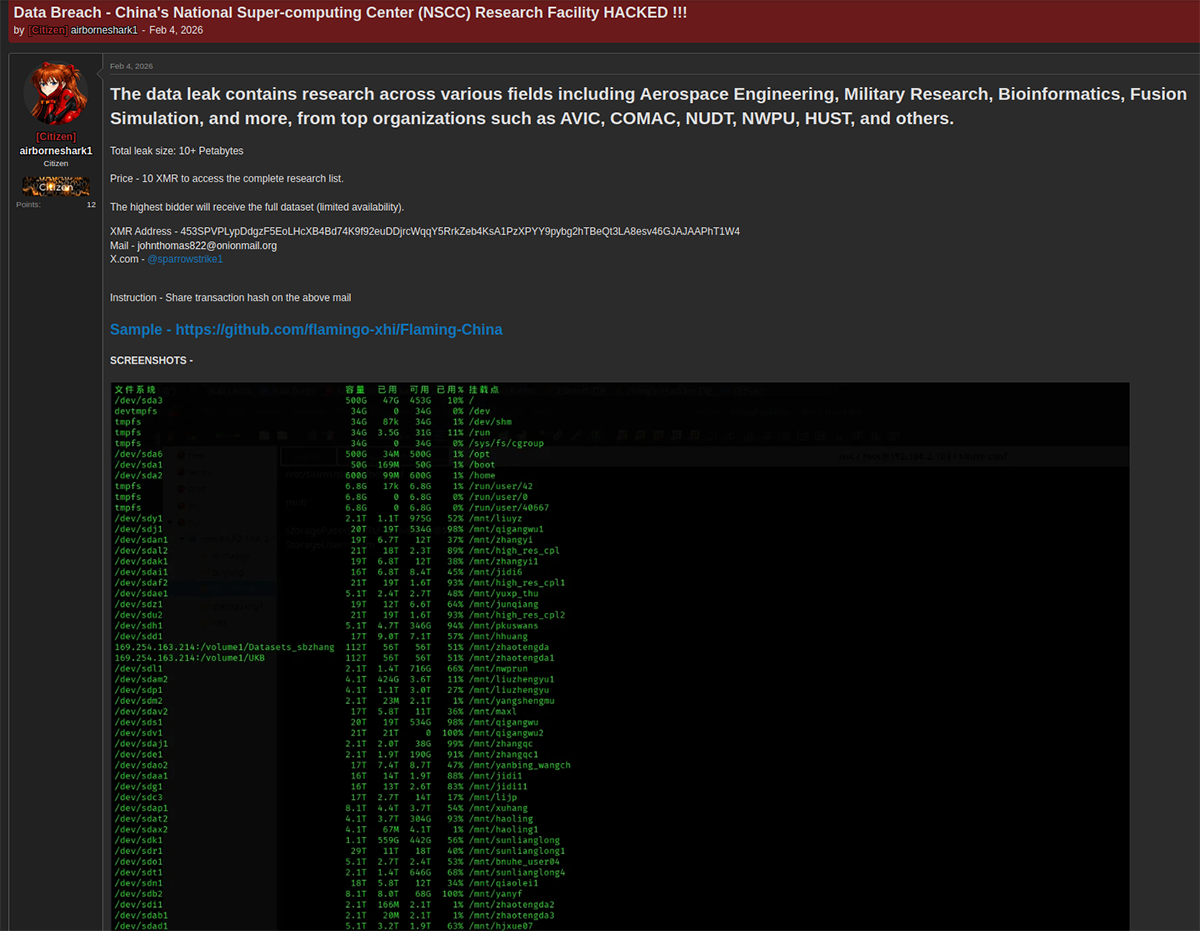
Post on Hasan’s BreachForums announcing the NSCC data for sale.
The sample data includes a wide range of different types of files, mostly focused around scientific research and development into defense technology. There is a detailed user manual for operating the “HPC1” system – which appears to be the name for their High Performance Computing cluster. One folder titled “AeroStealth” contains an assortment of files related to advanced computational modeling of fluid dynamics for aerospace applications.
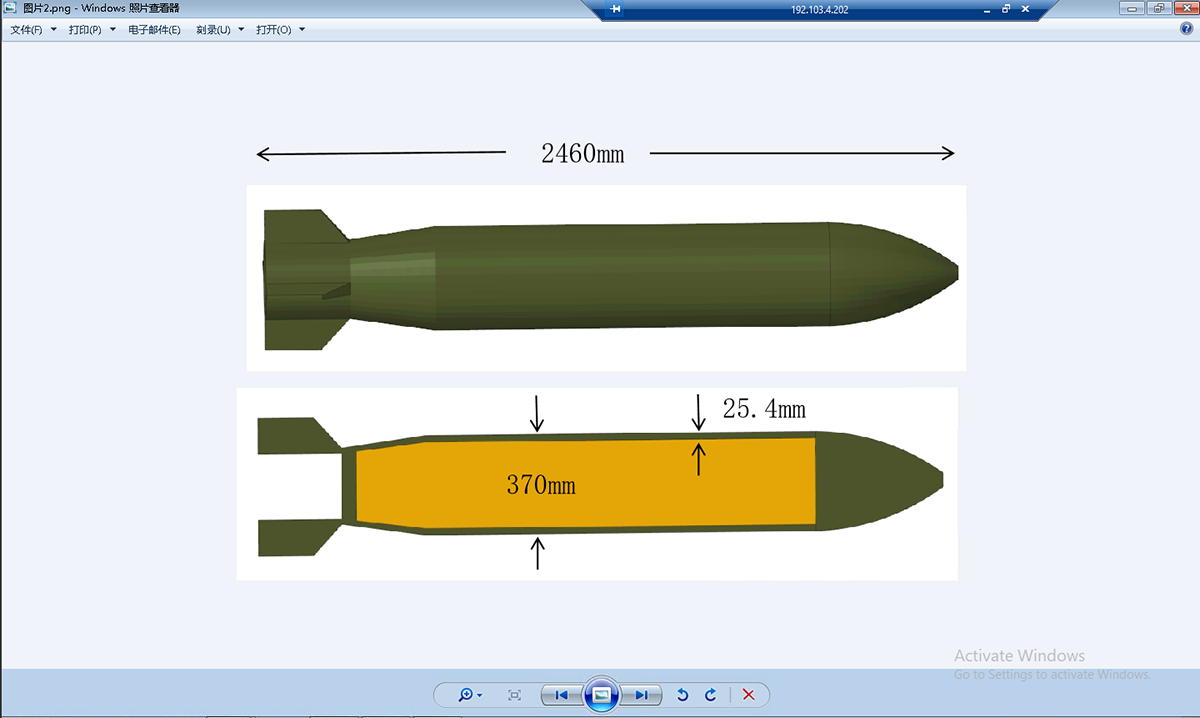
Image of a weapon from the NSCC sample data, showing the NSCC-TJ focus on defense technology. The actor appears to be using an RDP session to access files and take screenshots.
In a folder labeled “Feiyi” – apparently short for Flying Wing Aerodynamic Stealth Optimization (飞翼气动隐身优化), a technology used in UAVs – there is also a cracked version of the Altair HyperWorks FEKO modeling software apparently obtained from a CAD-focused software cracking group called SolidSQUAD.
While we didn’t find any obvious malware bundled in with the cracked software revealing this as a possible initial intrusion vector, it is still somewhat interesting that NSCC-TJ is using cracked computational electromagnetics software.
Other files in this folder also reference the X-47B, a stealth drone developed by Northrop Grumman. In 2025, a team of Chinese aerospace engineers published research into using reinforcement learning to enhance digital simulations of stealth aircraft that specifically used the X-47B to demonstrate their findings.

Portion of the file tree for the “Feiyi” folder in the leak showing cracked FEKO software as well as some references to the X-47B drone.
Data leaked from company behind Flax Typhoon

Post about an “Integrity Technology Group sensitive data leak” on DarkForums.
The data is split into two archive files – one is labeled as sample data, and the other is marked as sensitive data available for sale. As other researchers have also noted, the latter is encrypted and password-protected, making the data difficult to access.
In the “sample” file, the data is separated into three folders – scanning data (扫描数据), stolen data (窃取数据), and company data (集团资料). The scanning data appears to contain the results of different types of external scans on a range of different domains. These include both Chinese domains that are presumably Integrity Tech customers, as well as domains from possible Chinese government intelligence targets, including the Taiwanese Ministry of Digital Affairs. The stolen data looks like it contains exfiltrated data from multiple different targets, including BSNL – an Indian state-owned telco.
The company data folder appears to contain some data about Integrity Tech and its operations. It contains a handful of corporate documents, including:
- Invoices and contracts for technical services
- A 2020 whitepaper about their “APT Adversary Intelligence Tracking System”
- An accounting spreadsheet including income and expenditure data from July 2024 - July 2025
- A personnel list (人员清单) spreadsheet containing PII on 515 employees of Integrity Tech, including the company’s founder and chairman Cai Jingjing (蔡晶晶), who is listed at the top of the document with employee number 0001
Cover page of an Integrity Tech’s APT Adversary Intelligence Tracking System white paper (APT敌情跟踪产品⽩⽪书) from the sample data.
GhostSocks developer doxxed
The Lumma Rats, a site known for doxxing developers of the LummaC2 malware, has begun to target developers of the GhostSocks proxy malware. GhostSocks is a popular Golang-based proxy malware that infects computers to use them as proxy exit nodes. As we wrote about in December 2024, GhostSocks and LummaC2 are closely integrated such that actors using LummaC2 can also easily infect victims with GhostSocks reverse proxy binaries to turn their victims’ machines into residential proxies. Using this feature, actors are able to log in to victims’ accounts while appearing as if they are coming from the victim’s own machine from their usual IP address.
The Lumma Rats (Люмма крысы) doxxing site previously published detailed doxxes of dozens of developers and administrators of the LummaC2 infostealer malware-as-a-service in October and November 2025. So far, they have made two posts about GhostSocks:
- The first post called out GhostSocks generally for working with LummaC2. It also listed GhostSocks users and “sub-accounts” of LummaC2, indicating that LummaC2 could access GhostSocks accounts for users they had recommended to the GhostSocks service through their bundling scheme. The post also listed devices infected with the GhostSocks proxy located in Russia. Usually malware developed by Russian nationals is programmed to avoid infecting systems in Russia or other Commonwealth of Independent States (CIS) countries to avoid angering the Russian government.
- The second post doxxed Aleksandr Sergeevich Oborin, a Russian national, naming him as the main developer of GhostSocks. The post lists his name, date of birth, passport number, SNILS (Russian Individual Insurance Account Number), and INN (Russian Taxpayer Identification Number). It also lists usernames, email addresses, phone numbers, and banking information.
While we can’t confirm the attribution of the GhostSocks activity to this individual, we can see through our data holdings that many of the PII details about the named individual do appear genuine and interconnected.
Beginning of the doxxing post on the Lumma Rats website. The message at the bottom roughly translates to “Aleksandr Sergeevich Oborin, you’re f***ed.”