USE CASE: AUTOMATED ATO PREVENTION
Protect Employees & Consumers from
ACCOUNT TAKEOVER
Preventing account takeover attacks requires fast detection and remediation of exposed identity data beyond just stolen credentials. SpyCloud’s holistic approach illuminates dark web exposures well beyond what your current toolset finds and eliminates ATO threats automatically – so you can finally get ahead of criminals targeting your employees and customers.
The SpyCloud approach
Credentials are only part of the story. Identity data is dynamic, interconnected, and often exploited in ways most tools can’t see.
SpyCloud extends a holistic identity lens across personal, corporate, and crossover exposures with actionable data tied to real users and real threat vectors – with automation that solves the problem, not just notifies you about it.
Treating accounts as standalone perimeters and assuming device wipes solve the problem.
Viewing identities as interconnected data points that criminals exploit for unlimited access.
Users’ work, personal, current and past exposures matter to your business.
You don’t need more feeds – you need the right identity data that illuminates the scope of threats to your users right now.
Automating the remediation of stolen identity data (cookies, passwords) so you actually stop attacks before they happen.
Get ahead of account takeover – for every identity you manage
Monitor credentials and authentication artifacts tied to employees and consumers across breaches, malware infections, and successful phishes
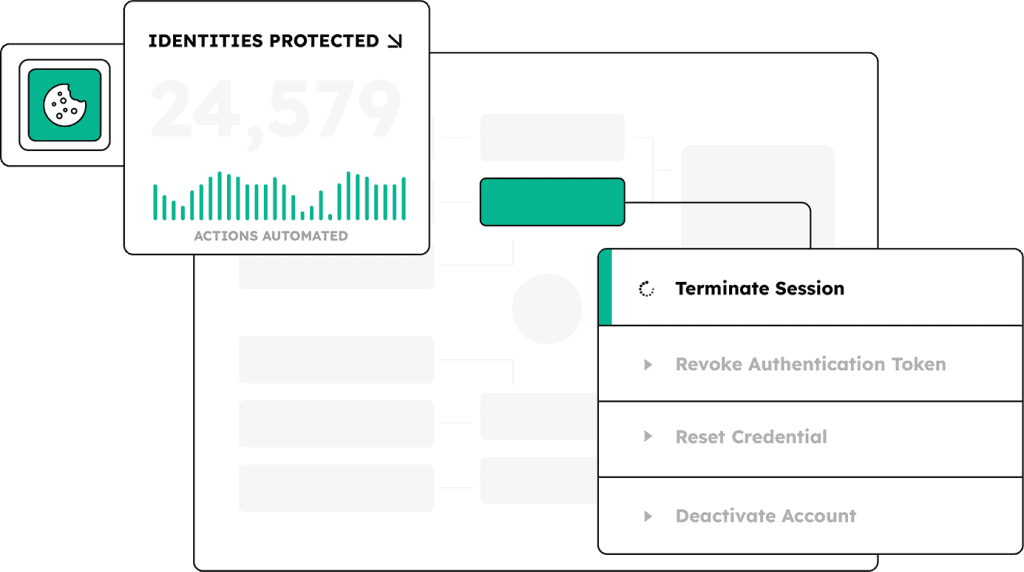
Kick off workflows that revoke tokens, reset passwords, and trigger enhanced authentication before compromise can occur
EXPLORE MORE PRODUCTS
Stop account takeover with identity threat protection
Prevent exposed identity data from being used to access employee accounts
Automate remediation within minutes of discovery in Active Directory, Entra ID, and Okta Workforce
EXPLORE WHO USES SPYCLOUD
Defenders
we help
Integrations





Next steps
Catch dark web identity exposures before attackers log in
Account Takeover Prevention FAQs
Credential monitoring catches exposed passwords but modern ATO attacks also exploit stolen session cookies, refresh tokens, and infostealer malware data. SpyCloud recaptured 8.6 billion stolen session cookies in 2025 and tracked 13.2 million new infostealer infections averaging 50 credentials each. Effective ATO prevention requires visibility across credentials, session cookies, and infostealer logs, not just breach data.
Alert-based ATO notifies security teams and relies on manual triage, taking hours or days. Automated ATO remediation triggers workflows directly in Active Directory, Okta, or Entra ID within minutes of detection. SpyCloud customers with Identity Guardians remediate exposed identities in under 5 minutes from discovery.
Infostealer malware frequently infects personal and contractor devices outside EDR coverage. In 2025, 40% of infostealer infections occurred on devices with EDR or antivirus installed. The malware exfiltrates everything stored in the browser across all applications. Organizations without visibility into infostealer logs in criminal markets cannot close the full ATO exposure from a single infection.
MFA and passwordless authentication reduce credential-based ATO risk but do not eliminate it. Both operate at login. After a successful authentication event, the system issues session cookies and refresh tokens that can be exfiltrated by infostealer malware or stolen through AitM phishing. In 2025, phishing attacks surged 400% year over year and SpyCloud recaptured 28.6 million phished identity records including session cookies and authentication tokens.
Native IdP tools operate on internal authentication signals and cannot see credentials stolen from personal devices, unmanaged endpoints, or third-party applications. SpyCloud recaptures identity records from criminal sources including infostealer logs, phishing kit output, and breach data. SpyCloud IDLink surfaces 12 to 14 times more exposed records per user than traditional monitoring methods.