USE CASE: FRAUD PREVENTION
Shift Fraud
Prevention Upstream
To Catch Risk Sooner
Fraud doesn’t begin at the transaction. It starts the minute a user’s identity is compromised. SpyCloud pipes compromised credentials, cookies, and PII into your application and risk models, letting you cut down false positives and stop account takeover, session hijacking, synthetic identities, and fraud without extra friction.
Outsmart fraudsters with identity-centric exposure intelligence
Most anti-fraud solutions focus on what users do. SpyCloud focuses on what’s already happened to them. By identifying users whose identities are actively being exploited or sold on criminal marketplaces, we facilitate real-time, decisive action – with minimal friction for legitimate users.
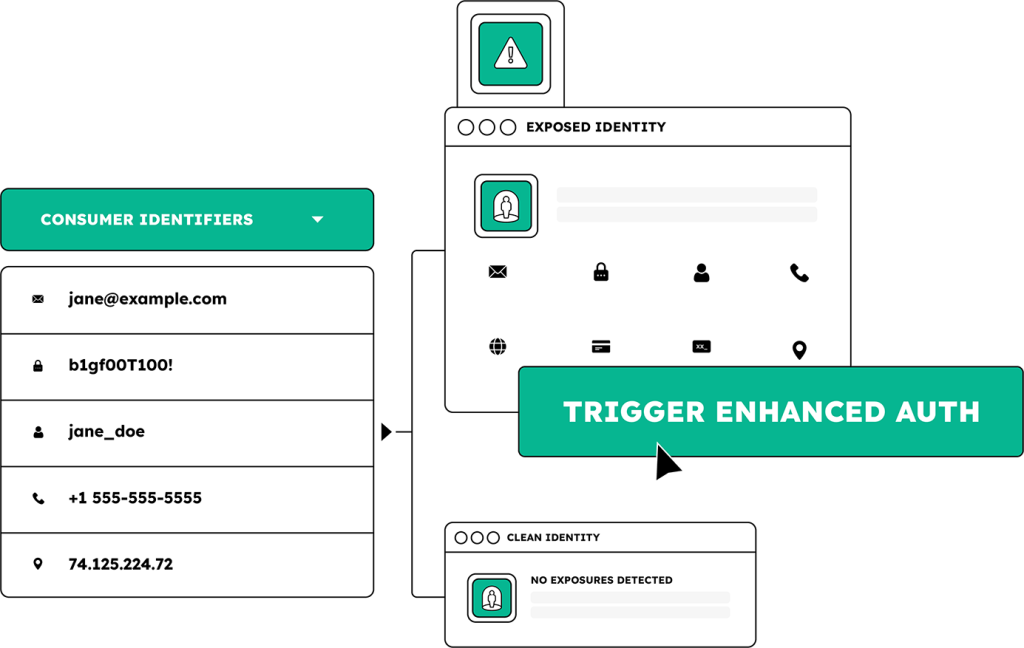
Detect exposed credentials, session tokens, and PII tied to users exposed in a third-party breach, malware infection, or phishing attack
Require step-up authentication or block transactions to stop potential fraudsters – and let low-risk users interact friction-free
Enrich investigations with identity exposure data to accelerate pattern recognition, streamline attribution, and resolve cases faster
Layer identity intelligence into every stage of the user lifecycle
TRANSACTION ATTEMPT
POST-FRAUD INVESTIGATION
Bad actors register with synthetic identities or previously exposed credentials
Fraudsters perpetrate ATO via reused credentials or session hijacking
Fraudsters bypass weak or static controls
Your team is plagued with manual, slow, low-fidelity workflows
Flag high-risk signups using breached, malware-exfiltrated and successfully phished identity data
Enrich real-time risk models to trigger step-up auth or block risky transactions
Accelerate attribution with identity-linked breach and malware exposure intelligence
EXPLORE MORE PRODUCTS
Turn exposure intelligence into your fraud defense
EXPLORE WHO USES SPYCLOUD
Defenders
we help
Digital identity teams
CIAM teams
Risk & trust teams
Improve user risk assessments and reduce false positives with malware-exfiltrated data and stolen session intelligence
Fraud investigators & analysts
Next steps
SpyCloud integrates with your existing stack to extend fraud signals, enhance identity risk scoring, and deliver measurable impact. Stop reacting and start predicting today.
Identity Fraud Prevention FAQs
Behavioral fraud detection platforms analyze what users do: login patterns, device characteristics, transaction velocity, navigation behavior, and other signals generated during a session or transaction. These tools are strong at detecting anomalous behavior from known users and catching automated fraud at scale. They have a structural limitation: they operate on signals generated inside the organization’s environment and cannot see what has already happened to a user outside it. A user whose credentials were stolen in an infostealer infection last week has not yet exhibited any anomalous behavior on your platform. Their login looks normal because it is normal — they have the right credentials, the right device, and no suspicious transaction history. SpyCloud provides the upstream intelligence layer that behavioral tools cannot generate: the fact that this user’s credentials, session cookies, or PII are currently circulating in criminal markets. That signal, fed into the fraud model before or during authentication, enables a risk intervention before the fraudster has had an opportunity to behave anomalously. The two approaches are complementary rather than competitive. Behavioral fraud detection remains essential for catching fraud that behavioral tools can see. SpyCloud extends fraud prevention to the identity compromise events that precede behavior entirely.
Synthetic identity fraud is difficult to detect at account creation because the fraudulent identity is constructed to look real. Traditional fraud checks — email validation, phone verification, device fingerprinting — are designed to verify the authenticity of identity artifacts, not to detect whether those artifacts have been fabricated from stolen identity elements or assembled from multiple real individuals’ data. SpyCloud’s Consumer IDLink API approaches this differently by correlating multiple submitted identity artifacts simultaneously against SpyCloud’s recaptured darknet dataset. When an account creation request submits an email address, phone number, username, and IP address together, IDLink checks whether those elements have previously appeared in combinations consistent with synthetic identity construction or criminal account farming. An email address that has never appeared in any breach record but is associated with a phone number from a heavily breached malware infection log, or a phone number that appears in multiple accounts flagged for fraudulent activity, produces a correlation signal that no single-identifier check can surface. This is the primary detection lever for synthetic identities at account creation where behavioral signals do not yet exist.
Session cookie-based ATO is the hardest fraud vector for legacy tools to catch because the attacker presents a valid authenticated session. The cookie was stolen from a legitimate user’s device through infostealer malware or AitM phishing, and when replayed it looks indistinguishable from the legitimate user’s normal session. Behavioral signals are minimal because the attacker is not making unusual requests — they are behaving like the account holder because they have the account holder’s session. SpyCloud’s Session Identity Protection product provides a continuously updated feed of compromised session cookies tied to an organization’s application domains, recaptured from criminal markets in near-real time. Fraud teams query this feed against active sessions or incoming authentication requests. When a session cookie matches a known-compromised artifact, the system can terminate the session and require fresh authentication from the legitimate user. Critically, this intervention is targeted: only users with confirmed compromised sessions are disrupted. Legitimate users with clean sessions experience no friction. This precision is what makes session cookie intelligence an effective fraud tool without the false positive burden that blanket re-authentication policies create.
SpyCloud’s consumer fraud APIs address four distinct lifecycle touchpoints that each catch a different attack vector. At account creation, the Consumer IDLink API performs holistic identity correlation to detect synthetic identity patterns before a fraudulent account is established. The User Exposure API and Password Exposure API can also run at account creation to flag whether the submitted credentials are already known-compromised. At login and authentication, the User Exposure API performs a real-time check against breach, malware, and phishing records, triggering step-up authentication for high-risk users without adding friction for low-risk ones. The Session Identity Protection feed flags users whose active session cookies appear in criminal markets, enabling session termination before an attacker can act on them. At high-value transactions, the Consumer IDLink API escalates risk scoring for accounts whose identity correlation signals indicate broader compromise or synthetic identity patterns. At rest, scheduled batch checks using the User Exposure API surface accounts that have become newly exposed since their last login, enabling proactive outreach or account holds before the account holder is targeted. Most production deployments run the User Exposure API inline at login plus periodic batch sweeps, and escalate to the Consumer IDLink API for high-risk touchpoints and new account screening.
SpyCloud delivers fraud intelligence via REST API with JSON output, designed to integrate into existing fraud stacks as an enrichment signal rather than as a replacement system. The most common integration pattern is adding SpyCloud’s exposure signals as an additional risk feature in the fraud decisioning engine alongside existing behavioral, device, and network signals. A user with a confirmed credential exposure in SpyCloud’s recaptured data receives an elevated risk score that can trigger step-up authentication, additional friction, manual review, or transaction block depending on the organization’s risk policy. SpyCloud does not make the fraud decision — it provides the darknet-sourced evidence that the decisioning engine uses to make a better-informed decision. For fraud teams using platforms like Sift, Sardine, Emailage, or custom ML models, SpyCloud’s API output can be consumed as a feature input with minimal integration work. For teams using SOAR or workflow automation platforms, SpyCloud Connect provides a managed service that builds and maintains custom integrations connecting SpyCloud data to any tool in the fraud stack without requiring dedicated engineering resources from the fraud team.