TL;DR
- Read the signals: Not all supply chain exposures carry the same risk. Malware and phishing warrant faster action than breach or combolist data. Context – vendor size, criticality, and shared system access – shapes how you respond.
- Use SpyCloud's Identity Threat Index: Weight exposures by severity, volume, and source to prioritize where to focus, and track trends over time to catch whether a vendor's security hygiene is improving or degrading.
- Act before an incident: SpyCloud shifts the timeline forward. Use exposure data to make decisions before an incident happens – not just after.
- Engage your partners: Sharing specific, evidence-based exposure data with vendors moves the conversation from "prove your security" to "here's what attackers already have – let's fix it together."
What to do when partner identity data is exposed on the dark web
Your supply chain is part of your attack surface, whether you can see it or not.
While traditional third-party risk management (TPRM) focuses on posture (controls, policies, and point-in-time assessments) these approaches don’t account for a critical reality: the exposed identity data that is already in attackers’ hands.
Most incident response (IR) playbooks start after a compromise within your supply chain is confirmed. But when you can continuously monitor for exposed identity data already circulating in the criminal underground, waiting for an incident to act creates unnecessary risk.
When vendor employees fall victim to malware, phishing, or third-party breaches, their exposed identities become viable entry points into your environment. Enterprises can mitigate the risks associated with supply chain exposure by taking swift action to inform affected partners, vendors, and contractors and help them remediate.
SpyCloud Supply Chain Threat Protection provides continuous visibility into exposed identity data across your vendor ecosystem so you can understand who and what’s been exposed, how it could be used to access your critical data and IP, and what it means for your environment right now.
This guide focuses on how to interpret vendor exposure data and act on it with SpyCloud so that exposure signals lead to informed decisions, not just awareness.
SpyCloud’s recommended flow for supply chain threat protection.
Your vendors’ compromised credentials are your problem too. When partner identity data surfaces in the criminal underground – through infostealer malware, phishing campaigns, credential breaches, or combolists – it creates viable entry points into your environment. This guide covers how to:
Supply chain security is a shared responsibility. The sooner you act on exposed identity data, the less likely it is to end up in an incident report.
Follow this guide for tangible steps you can take to improve supply chain visibility and threat protection.
How to interpret supply chain exposure signals
Not all exposures across your supply chain carry the same risk – the key is understanding what each signal means and how it could affect your environment.
To set the stage, you’ll want to start with context. A partner’s location, industry, size, and relationship to your data all shape how you should respond. SpyCloud publishes data continuously so you can act fast – but we always advise customers to pay attention to historical trends as well. Patterns over time often reveal risks that a single snapshot misses, and unusual movement (up or down) may signal a conversation worth having with your partners.
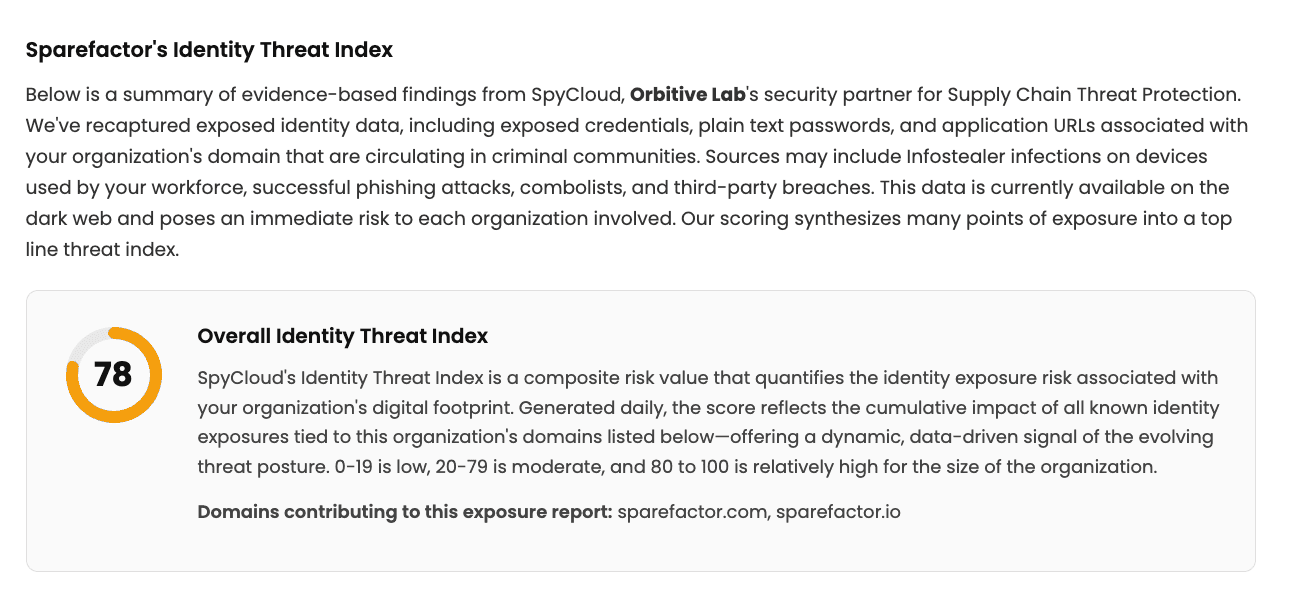
SpyCloud’s Identity Threat Index
SpyCloud’s Identity Threat Index helps contextualize these signals by weighting exposures based on severity, volume, and data source – giving you a clearer view of where to focus. This at-a-glance continuously updated score converts raw darknet exposure data into actionable, sortable risk signals across malware, phishing, breach, and combolist exposures.
Rank vendors by overall risk or drill down into specific exposure types to identify which vendors require immediate attention. Or choose a specific time frame to see whether a third party’s security hygiene is improving or degrading over time.
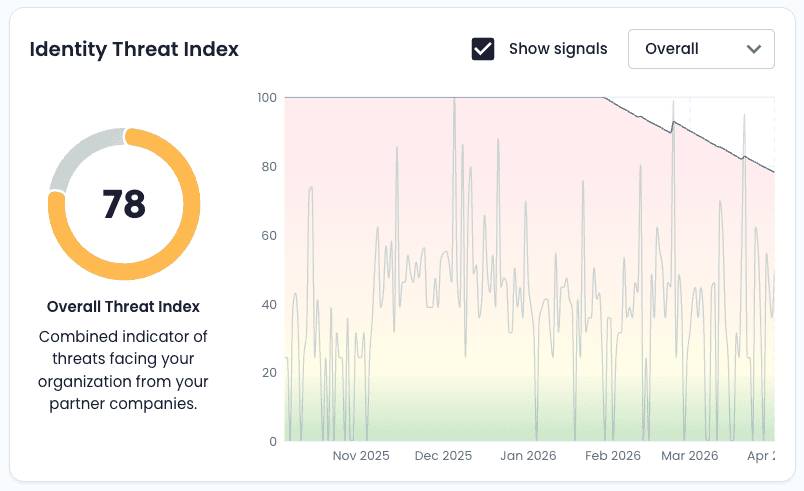
An example of the SpyCloud Supply Chain Threat Protection Identity Threat Index.
Treat the Identity Threat Index as your pre-incident response triage layer. Instead of waiting for SIEM alerts to escalate into incidents, prioritize risk by reviewing recent exposures across your supply chain. Look for which vendors are trending in either direction to understand what events are happening to inform these values.
Then dive into a vendor to explore the data a level deeper.
Exposure signals
Password reuse hygiene
SpyCloud surfaces password hygiene signals that can inform how you tune existing security controls. You can see the overall reuse rate but also patterns into the number of employees who are reusing passwords, and how frequent that specific password appears in the darknet
For example, if you observe a high password reuse rate among a vendor’s workforce, you can:
- Increase scrutiny on activity (like emails) originating from that vendor’s domain
- Adjust authentication or monitoring policies accordingly
- Use the data as context for vendor conversations
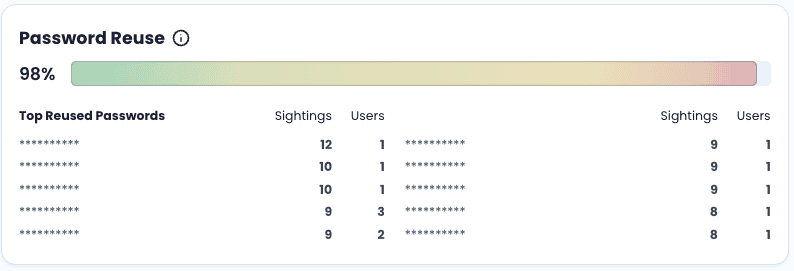
An example of password reuse signals tied to a vendor.
Infostealer malware exposures
Malware infections often provide the most actionable signal. These infostealer logs can include credentials, session cookies, and application access from infected devices. Look for exposed applications, repeat infections, and the number of affected employees.
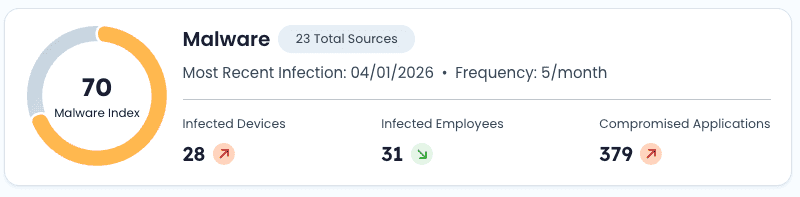
An example of malware exposure signals tied to a vendor.
A quick note on exposed applications
Applications exposed by an infostealer infection are critical pieces of information to determine the risk of your partners and any threats to your organization. By seeing what’s been exposed on vendor devices, you’ll immediately know if something you host has been compromised and requires remediation, or if there is risk from shared third-party apps that requires action.
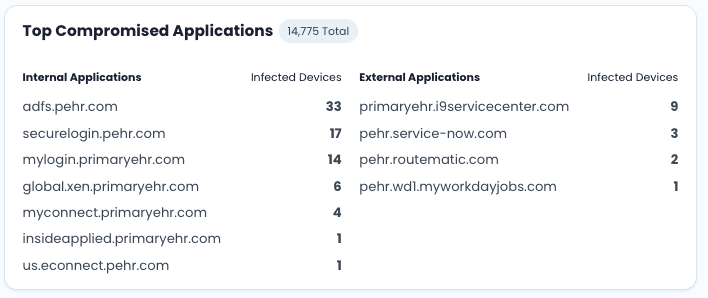
An example list of compromised applications with the corresponding count of malware-infected devices.
For every vendor, you can see the top list of compromised applications, along with the count of infected devices. Focus on two areas:
Internal applications
If exposed applications include systems you host:
- Escalate internally to assess access risk and prevent full-blown incident response
- Evaluate whether sessions, credentials, or tokens may be compromised
- Take appropriate containment or monitoring actions
Shared or third-party applications
If exposure includes SaaS tools shared between your organizations:
- Assess whether shared access could introduce risk
- Use this information to guide vendor communication and remediation
Phishing exposures
Data from successful phishing campaigns can include credentials and sensitive identity information. SpyCloud’s Identity Exposure Report showed that almost half of all phished records include an email address and location data (IP or physical address), enabling targeted social engineering attacks, and 49% of victims are corporate users. It’s no surprise that phishing is now the top reported initial access vector for ransomware.
- What it means: Increased likelihood of account takeover and follow-on attacks
- What to look for: Volume of affected employees, presence of plaintext passwords
- Why it matters: Even with awareness programs in place, phishing continues to produce usable credentials
Start by educating your partners on who has been successfully phished, so they can advance their preventative measure to look for users who may also be victims of phishing target lists, trying to launch follow-on attacks.
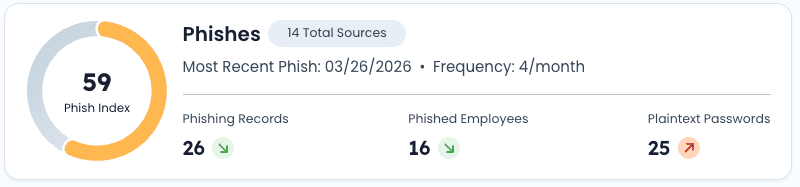
An example of phishing exposures tied to a vendor.
Combolist exposures
Credential lists – now increasingly enriched with URL:Login:Password (ULP) data – are frequently aggregated and circulated for reuse by cybercriminals.
- What it means: High risk of credential stuffing and password reuse exploitation
- What to look for: Password reuse rates, overlap with corporate domains
- Why it matters: Reused credentials can bridge personal and professional access
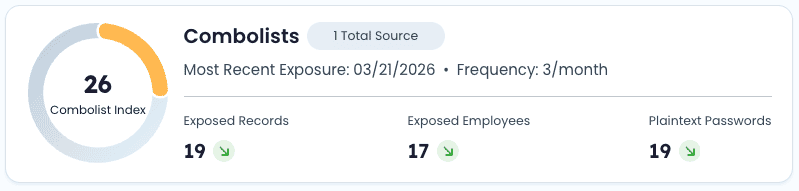
An example of combolist exposures tied to a vendor.
Third-party data breach exposures
SpyCloud also tracks historical exposure from breaches across external services. This information doesn’t mean your vendor organization has necessarily been breached nor is there a confirmed incident requiring a response. But the data does mean users across your supply chain have been compromised and their data is present in the darknet.
- What it means: Persistent identity risk, especially when credentials are reused
- What to look for: Frequency of exposure, repeated credential use, employee overlap
- Why it matters: Breach data often fuels other attack methods like credential stuffing

An example of data breach exposures tied to a vendor.
All of these exposure signals become inputs into your broader security strategy to prevent incidents – not just a metric to track.
Turning exposure data into action
Traditional incident response playbooks are designed for confirmed incidents – but continuously monitoring your suppliers for new exposure data helps you act earlier to guide decisions before an incident occurs.
Exposure data is only valuable if it informs decisions. When reviewing supply chain exposure signals, focus on three questions:
01
What type of exposure is it?
Malware and phishing signals typically require faster attention than breach or combolist data.
02
Does the exposure intersect with our environment?
Look for shared applications, domains, or access points that could create a direct path into your systems.
03
What’s the potential impact?
Consider the number of affected vendor employees, type of data exposed, and whether access to sensitive systems could be involved.
The purpose here is to avoid alert fatigue and focus on the exposure signals that translate into real threats to your organization.
Triage framework based on exposure signals
| Exposure signal | Recommended action |
| ⚠️ High password reuse rate across many employees | ✅ Set up heightened security on any activity from the vendor’s domains |
| ⚠️ Elevated frequency of exposed records, no active malware or phishing | ✅ Monitor over time; document with compliance teams |
| ⚠️ Active malware or phishing signals | ✅ Assess impact on your environment, notify internal teams, engage vendor |
| ⚠️ High-severity active exposure with shared app access | ✅ Treat as near-incident; deploy protective actions now |
Focus on what you can control. For most scenarios, you won’t be able to remediate or reset exposed vendor credentials or access directly, but there are other actions you can take.
See a spike in frequency of malware-infected devices? Reach out to your vendor’s security team about their device policy. See phished employees? Alert your vendor that this new attack vector might be blind to their security controls. Even a rise in combolist exposure might warrant education into the rise of ULP combolists and remediation steps on their side.
Need to dig deeper? That’s where SpyCloud Investigations comes in
When a vendor’s exposure profile changes – such as a spike in their Identity Threat Index or the presence of malware or phishing signals – your team may want to investigate further. SpyCloud Investigations allows you to investigate vendor domain exposures with powerful pivoting, graphing, and AI Insights to gain a deeper understanding of what’s at stake.
Why transparency with partners matters
Supply chain security is shared. Acting on exposure data is more effective when you engage partners directly.
SpyCloud enables a more productive, evidence-based approach to vendor communication. The most effective way to help prevent incidents and become a trusted advisor, is to share a sample of SpyCloud’s recaptured identity data directly from with your contacts across your supply chain.
Instead of asking vendors to validate their security posture, you can show:
- What exposed identity was identified with their domains
- When the exposures occurred
- Which employees were compromised
- What type of data is involved
This shifts the conversation from “prove your security” to “here’s what attackers already have – let’s address it.”
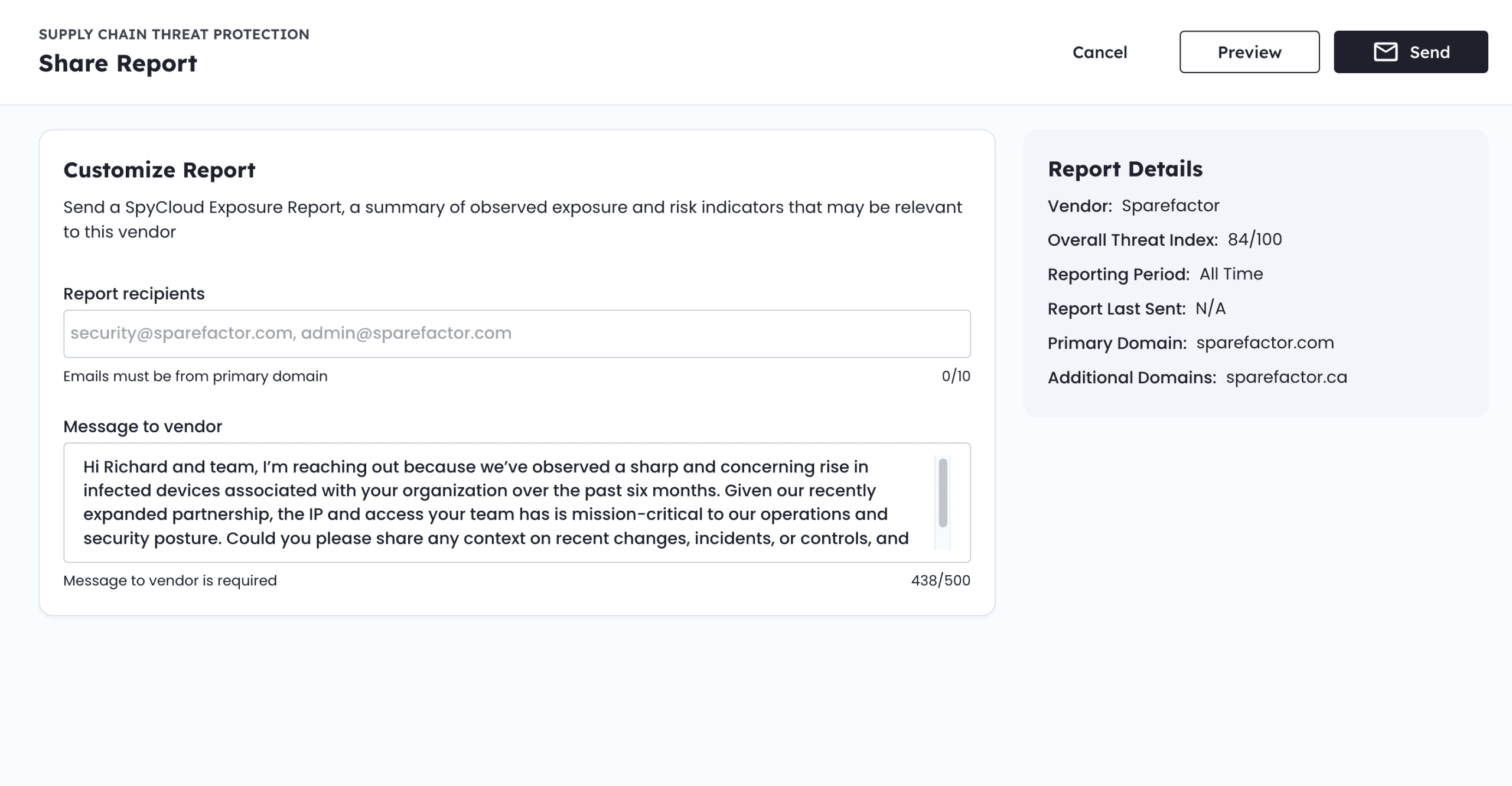
An example of how to share a custom message and the corresponding exposure report with a partner.
When reaching out, provide clarity and direction. Start by writing a tailored message to your partner. This is the chance to add your own knowledge and expertise and understanding of SpyCloud data to help the partner know exactly what is happening and what you’re asking them to do.
Key elements to include in your outreach:
- Summary of the exposure data and timeframe
- Explanation of the data source (malware, phishing, breach, etc.)
- Confirmation of risk (data is accessible to threat actors)
- Clear expectations for follow-up
How to communicate exposure to vendors
Educate your partner about SpyCloud’s exposure data and what makes up their individual Identity Threat Index across the extent of the monitored domains. They don’t need access to SpyCloud to take action on the guidance you send.
An example summary of a vendor’s overall Supply Chain Identity Threat Index for their domain.
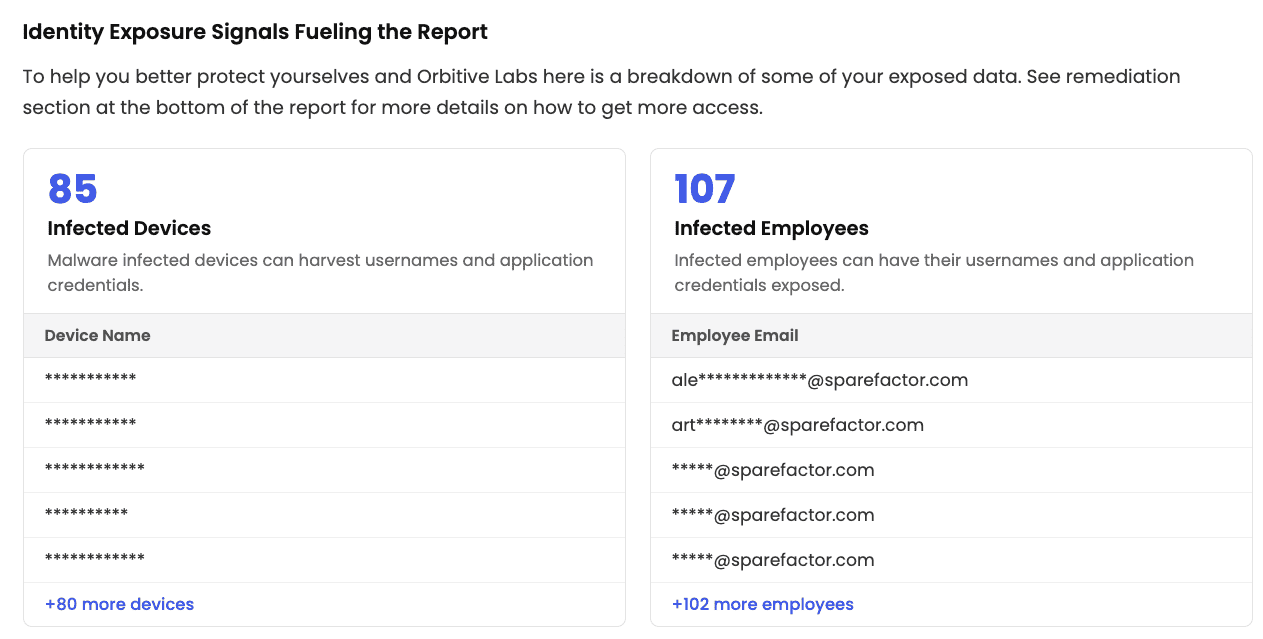
Example of malware-infected device and employee details driving the signals included in the report.
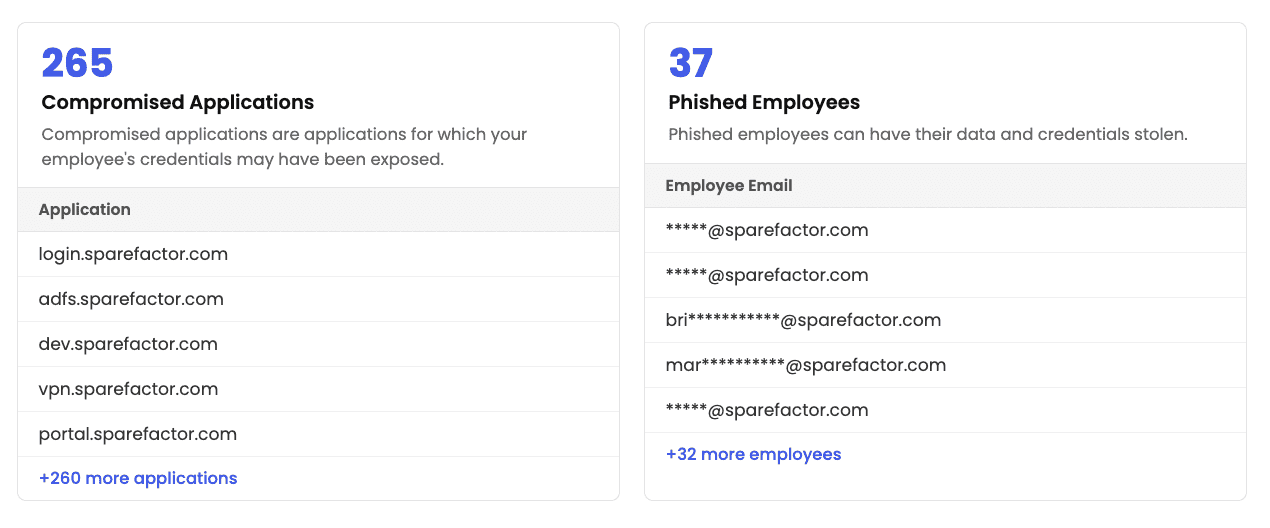
Example of compromised application and phished employee details driving the signals included in the report.
Suggested actions to request:
- Acknowledge receipt of the exposure information
- Validate affected users
- Reset credentials where applicable
- Remediate access from infected devices and revoke session cookies
- Strengthen authentication controls (e.g., MFA)
- Review device and phishing protections
Providing structured, evidence-based communication helps vendors take action more quickly – and strengthens the partnership.
The SpyCloud difference for your supply chain
Traditional third-party risk management platforms provide important insight into vendor security posture, but they weren’t designed to detect active identity threats.
SpyCloud Supply Chain Threat Protection focuses on how compromise actually happens: through exposed credentials, malware infections, successful phishing campaigns that allow stolen identity data to circulate in the criminal underground. It’s built to support a two-way street: visibility for both you and your partners.
By combining continuous exposure monitoring with actionable context, security teams can:
- Identify where vendor exposure becomes an enterprise threat
- Prioritize response based on real evidence of compromise
- Strengthen partnerships through transparent, data-driven collaboration
At the end of the day, reducing supply chain risk requires the ability to act on identity exposures before they’re used against you.
Don’t inherit your vendors’ risk – solve it with SpyCloud.
FAQs
Traditional TPRM evaluates vendor security posture through controls, policies, and point-in-time assessments. SpyCloud Supply Chain Threat Protection goes further by continuously monitoring for exposed identity data already circulating in criminal underground markets – credentials, session cookies, and malware logs that attackers can exploit right now, regardless of a vendor’s self-reported security posture.
SpyCloud monitors for five key exposure types across your vendor ecosystem: infostealer malware infections, phishing campaign data, third-party data breaches, combolist exposures, and password reuse hygiene signals. Each carries different risk implications and recommended response actions.
SpyCloud’s Identity Threat Index contextualizes exposures by weighting severity, volume, and data source. Active malware and phishing signals generally require faster attention than exposed breach or combolist data. Exposures that intersect with shared applications or systems you host should be escalated immediately.
Yes, and SpyCloud is designed to support that. Sharing recaptured identity data directly with vendor security contacts shifts the conversation from abstract posture discussions to concrete, evidence-based remediation. SpyCloud allows you to share exposure reports directly with partners via email so vendors can see their own exposed data and take action.
Recommended remediation requests include: acknowledging the exposure, validating affected users, resetting compromised credentials, revoking session cookies from infected devices, enabling or enforcing MFA, and reviewing phishing and device protection policies.
No – it moves the timeline forward. SpyCloud helps you act on exposure data before a confirmed incident, reducing how often full incident response is triggered. When deeper investigation is needed, SpyCloud Investigations adds pivoting, graphing, and AI Insights for more complex vendor threat analysis.



