For the past decade, SpyCloud has tracked how stolen identity data fuels cybercrime. That underground economy is now faster, more automated, and more interconnected than ever – and identity exposure is scaling with it.
SpyCloud’s 2026 Identity Exposure Report examines identity data recaptured from criminal underground sources over the past year. SpyCloud’s recaptured datalake has grown to 65.7 billion distinct identity records – a 23% increase year over year.
But the more important story is what’s changing beneath the surface: exposure is spreading like disease, spanning both human and non-human identities, and attackers are weaponizing identity artifacts that deliver outsized downstream impact. Below, we break down the key findings and what security teams can do to reduce identity-driven risk.
What is identity exposure?
Identity exposure occurs when credentials, session cookies, API keys, authentication tokens, or other identity artifacts are stolen and circulate in criminal underground sources. Attackers use this data to gain initial access to accounts, cloud systems, developer tools, and enterprise applications.
Identity exposure fuels identity-based attacks such as:
Identity exposure is spreading, fast
For years, identity compromise was framed as a series of discrete events: a breach disclosure, a phishing campaign, a specific malware outbreak. Security teams responded incident by incident.
The data now shows a different pattern.
Identity exposure is spreading, fast
Identity exposure is sustained by multiple, parallel streams feeding the same threat ecosystem – stemming from third-party breaches to phishing, malware, and combolists. In 2025 alone, SpyCloud recaptured:
- 13.2 million infostealer infections, exposing 642.4 million credentials
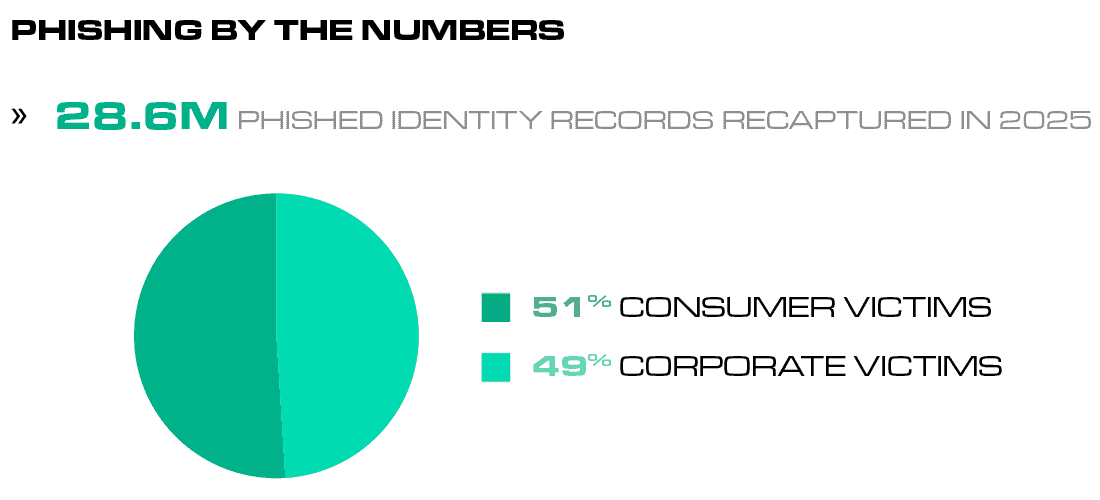
- 28.6 million phished records, about half of which include IP and physical addresses
- 4,514 data breaches, including 39 breaches with more than 50 million records
- 6.2 million credentials or authentication tokens for AI tools
Notably, the breach volume observed in SpyCloud’s data exceeds the number of publicly disclosed incidents. For example, the Identity Theft Resource Center reported 3,322 publicly disclosed compromises in 2025. The gap reflects a growing reality: many breaches are never publicly reported, and others surface in criminal marketplaces where stolen identity data is traded long before organizations disclose incidents.
SpyCloud’s recaptured data provides visibility into these hidden exposure streams – revealing how identity artifacts move through the criminal ecosystem even when the originating breach remains undisclosed.
Once this data enters underground marketplaces, attackers rarely use it in isolation. Attackers mix and match identity fragments across sources to gain initial access that sometimes even appears legitimate (like in the case of session hijacking). Credentials from one dataset intersect with session cookies from another. A reused password overlaps with third-party application access. Phishing data supplies the context needed to make malicious activity look like normal behavior.
Identity sprawl has expanded the enterprise attack surface
Modern organizations no longer manage a handful of logins. They operate across SaaS platforms, cloud environments, developer tools, AI systems, and external services – each introducing new identities and new exposure paths.
But identity sprawl isn’t limited to people.
Organizations have accumulated a second, less visible layer of access: non-human identities (NHIs). API keys, tokens, secrets, service accounts, and automation credentials allow systems to authenticate continuously without human interaction.
That persistence changes the risk. Many NHIs:
- Operate 24/7
- Carry broad or over-privileged access
- Follow inconsistent rotation practices
- Lack phishing-resistant MFA or clear ownership
SpyCloud data shows exposed API keys, infrastructure tokens, developer credentials, and AI authentication artifacts circulating in criminal underground sources. These identities often sit deep within trusted workflows, meaning a single exposed token can provide disproportionate downstream access.
Phishing: An enterprise identity threat
Phishing remains one of the most reliable ways to harvest identity data – and it’s not primarily a consumer problem. SpyCloud recaptured 28.6 million phished identity records in 2025, with 49% tied to corporate victims. Enterprise controls are not fully preventing identity compromise.
In addition to delivering traditional credentials into bad actors’ hands, modern phishing datasets increasingly include:
- Session cookies
- Authentication tokens
- MFA artifacts
- Physical location data
These artifacts allow attackers to bypass traditional login protections without defeating them directly. Instead of “cracking” accounts, they use valid authentication mechanisms.
Phishing as an identity threat multiplier
Continuous identity exposure monitoring and rapid session invalidation reduce the downstream impact of phishing and malware-based identity theft.
Infostealer malware is exfiltrating identity data at massive scale
Infostealer malware continues to serve as a primary source of high-quality identity data for attackers. In 2025, SpyCloud observed:
-
13.2 million malware infections that exposed:
- 642.4 million credentials
- 8.6 billion cookies
- This new data confirms that the average infostealer malware infection exposes 50 user credentials.
Even after law enforcement disruption of major stealer families, identity extraction persisted at scale. In fact, 40% of infections occurred on endpoints protected by EDR or antivirus tools, demonstrating that traditional endpoint defenses are not sufficient to prevent identity extraction.
And malware is fueling session hijacking attacks
Attackers increasingly rely on session cookies and authentication tokens captured through malware (and phishing) to hijack active user sessions. In 2025 alone, SpyCloud recaptured 8.6 billion stolen session cookies circulating in underground sources.
Because session cookies represent authenticated sessions, attackers can reuse them to bypass login protections entirely, gaining access without ever needing a password.
This technique, commonly known as session hijacking, allows attackers to:
- Bypass MFA protections
- Impersonate authenticated users
- Move laterally across SaaS environments
- Maintain persistent access to enterprise applications
Non-human identities give high-leverage access to attackers
The defining shift this year is leverage. Attackers are prioritizing identity artifacts that unlock disproportionate downstream access, particularly NHIs.
In 2025, SpyCloud observed 18.1 million exposed API keys and tokens, including:
- 60+ thousand API keys and tokens tied to payment and remittance platforms
- 36+ thousand infrastructure and hosting tokens
- Thousands more tied to developer ecosystems, collaboration tools, software package repositories, and AI platforms
Passwords still matter, but they’re part of a larger and systemized problem
Despite advances in authentication, passwords remain a primary fuel for identity abuse.
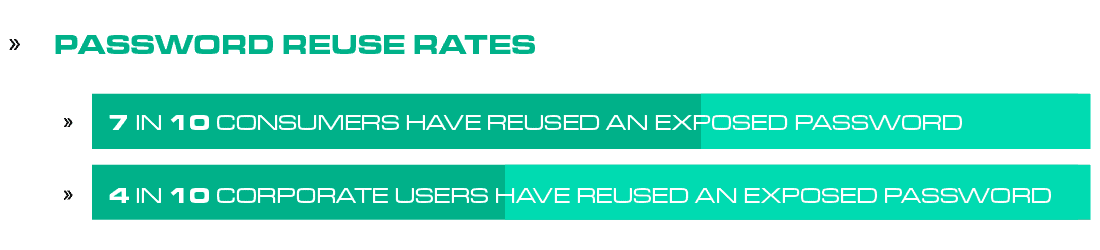
In 2025, SpyCloud recaptured 5.3 billion credential pairs circulating in criminal underground sources. Analysis also showed password reuse rates of 65% among consumer accounts and 42% among corporate accounts.
A single exposed password can still unlock one or multiple systems.
But passwords are rarely exposed alone. They are often captured alongside session cookies, third-party application credentials, personally identifiable information (PII) and other identity data – increasing the likelihood of account takeover and follow-on abuse.
Even organizations investing in stronger authentication aren’t immune. SpyCloud recaptured 1.1 million password manager master passwords in 2025. A single compromised master password can expose an entire credential vault, amplifying the downstream impact of a single identity exposure event.
Identity exposure has reached a turning point
For years, identity exposure was treated primarily as a volume problem – more breaches, more records, more remediation to manage.
The 2026 report shows it has crossed three critical thresholds:
- Scale: The scale of circulating identity data has accelerated dramatically
- Scope: Exposure now spans both human and non-human identities across cloud, third-party, and AI ecosystems
- Leverage: Attackers are prioritizing high-leverage identity artifacts that enable multiple entry points and automated abuse
Together, these shifts redefine identity risk. Identity now functions as interconnected access infrastructure, underpinning cloud environments, development pipelines, vendor ecosystems, and AI-driven workflows. When that infrastructure is exposed, attackers gain valuable access and a structural advantage.
The identity attack surface runs wide and deep
Attackers are assembling access from every layer of exposed identity data – passwords, cookies, tokens, API keys, PII, and more – to build persistent, reusable entry points into modern environments. As identity sprawl expands across cloud, SaaS, third-party ecosystems, and AI systems, the impact of a single exposed identity continues to grow.
Organizations that treat identity exposure as a measurable attack surface and respond with continuous monitoring, rapid session invalidation, and disciplined governance across human and non-human identities can reduce attacker advantage.
The question isn’t whether exposure will occur. It’s whether your defenses are built to contain the sprawling identity perimeter.
How organizations can reduce threats tied to identity exposure
Organizations are increasingly adopting identity threat protection strategies designed to detect and remediate exposed identity data before attackers can weaponize it. Effective programs focus on progressive threat reduction across three maturity levels:
Level 1 – Defend:
Remove the most common paths to initial access
- Reduce password reuse and enforce phishing-resistant MFA
- Identify and rotate known-exposed credentials
- Monitor for workforce and consumer identity exposures from breaches, phishing, and malware
Level 2 – Deepen:
Implement comprehensive exposure monitoring and containment
- Remediate historical and new workforce and consumer identity exposures
- Invalidate exposed sessions, cookies, and tokens to reduce session hijacking risk
- Expand visibility to vendor and third-party identities
- Inventory non-human identities, assign ownership, and enforce least-privilege access
Level 3 – Disrupt:
Proactively break attack cycles
- Continuously monitor exposed identities across human and machine accounts
- Automate remediation workflows to reduce response time
- Leverage tradecraft-driven AI to surface hidden identity threats