PRODUCT: WORKFORCE THREAT PROTECTION
Detect Identity Exposures
& Automatically Kill the Attack Path
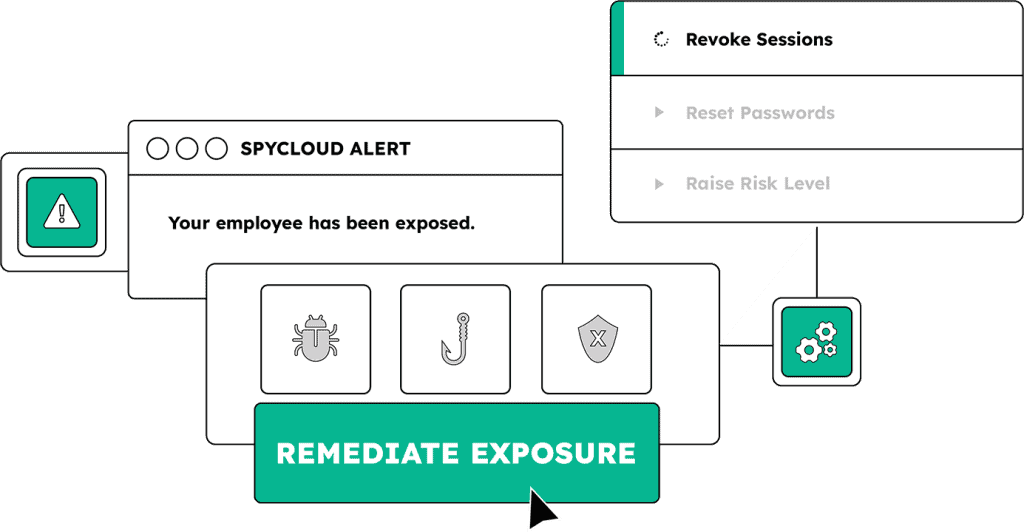
Attackers don’t need passwords to get in. Malware infections, successful phishes, combolists, and breaches leave behind a trail of exposed identity assets that criminals use to bypass authentication entirely. SpyCloud continuously detects workforce identity exposures, giving you the intelligence to act first: reset sessions and shut down high-severity threats.
Know when workforce identities and sessions are exposed, continuously
Stolen session cookies bypass MFA and passkeys entirely, giving criminals authenticated access to your environment without ever touching a password. By recapturing exposed identity data and stolen sessions directly from the underground, SpyCloud delivers early, actionable intelligence and automated remediation that closes entry points before they’re exploited.
See recaptured session cookies, identity data, and credentials from malware logs, phishing kits, combolists, and breaches linked to your workforce and contractors
Instantly invalidate compromised sessions across your entire workforce and reset exposed credentials – eliminating the authentication bypass window
Push early-warning intelligence into your IAM, SSO, or SIEM to trigger adaptive policies – risk scoring, conditional access, and automated remediation – the moment an exposure is detected
Explore how SpyCloud's continuous workforce threat protection works
Integrate directly into your identity and response stack
Designed for fast-moving security teams, SpyCloud integrates into your existing workflows to detect and act on identity exposures before they become incidents or events.
Push exposure signals into your IAM/IdP to revoke stolen sessions and enforce step-up authentication the moment exposures are detected

Feed workforce identity exposure signals into your SIEM for alerting, investigation, and corelate with other identity security data

Automate remediation workflows and incident response in your SOAR using SpyCloud identity exposure data

SpyCloud digs deeper into the dark web and cyber underground than other tools and finds more stolen identity data sooner. We have more hits than we did with the other system because SpyCloud data is fresher and more complete.
EXPLORE OTHER PRODUCTS
Protect your entire workforce from identity threats
Detect exposures across your extended workforce and automatically close the attack path.
Identity Guardians
Automatically revoke stolen sessions across Active Directory, Okta Workforce, or Entra ID – eliminating authentication bypass
Endpoint Threat Protection
Detect infostealer malware infections across your workforce to uncover stolen session cookies and application access that give attackers a foothold
Next steps
Identity threats targeting your workforce start in the underground. SpyCloud finds the starting point and shuts it down.
Employee Credential Protection FAQs
SpyCloud Workforce Threat Protection monitors employee and contractor credentials across four distinct data sources recaptured from criminal infrastructure. Third-party breach data covers credentials from breaches at companies where employees registered with work email addresses, including breach source details and plaintext passwords. Infostealer malware logs cover credentials exfiltrated from infected employee and contractor devices, along with session cookies, device fingerprints, and application access data captured in the same infection. Phishing capture data covers credentials harvested during successful phishing attacks targeting employee accounts, surfaced from captured phishing kit output before those credentials circulate widely in criminal markets. Combolists cover repackaged credential sets that aggregate multiple breach and malware sources into new attack-ready lists. SpyCloud continuously ingests and processes more than 25 billion pieces of stolen identity data every month, with new data typically published within days of appearing in criminal markets well before it reaches breach notification services or public indexes. The practical difference is that SpyCloud customers see exposures in hours to days rather than the weeks to months that follow typical breach disclosure timelines.
Standard dark web monitoring and breach notification services identify credential exposures by scanning indexable portions of dark web forums and marketplaces, or by receiving notifications when a breach is publicly disclosed. Both approaches depend on data that is already publicly or semi-publicly available — which means it arrived in criminal markets weeks or months before the monitoring service found it. SpyCloud infiltrates criminal communities directly and recaptures stolen identity data from the source before it enters the wider criminal ecosystem. This includes infostealer malware logs, which are distributed through private criminal channels and rarely indexed by dark web scanners, and phishing kit output, which is captured before credentials from a phishing campaign have been aggregated and resold. SpyCloud’s recaptured dataset now contains 65.7 billion distinct identity records. Beyond data freshness and scope, SpyCloud’s IDLink analytics extend monitoring to employees’ personal identity footprints — surfacing exposures tied to personal email addresses and personal accounts that share password patterns with corporate accounts. This produces 14 times more plaintext passwords per user compared to exact-match monitoring against the corporate domain alone, catching the password reuse attack path that breach notification services structurally cannot see.
Workforce Threat Protection is an intelligence and detection layer, not a replacement for IAM tools. Okta and Azure AD manage identity lifecycle, access policy, and authentication. They operate on internal signals — login events, access requests, policy violations inside the corporate environment. They have no visibility into what is happening in criminal markets with employee credentials outside the corporate perimeter. Workforce Threat Protection fills that gap by continuously monitoring criminal sources for exposures tied to employee identities and delivering actionable exposure alerts. Those alerts then feed directly into IAM workflows: Workforce Threat Protection integrates with Okta, Entra ID, and Active Directory to trigger automated remediation when a match is confirmed. For organizations using Identity Guardians, the automated response is a forced password reset or session revocation executed within minutes of detection. For organizations using SIEM or SOAR, the exposure data enriches alert queues and feeds automated playbooks. The relationship is additive: IAM tools manage the authentication layer while Workforce Threat Protection monitors the criminal underground for what attackers already know about that layer.
Workforce Threat Protection and Endpoint Threat Protection both use SpyCloud’s recaptured darknet data, but they address different scopes of the identity exposure problem. Workforce Threat Protection monitors employee and contractor credentials across the corporate domain against breach, malware, and phishing data, and surfaces the credential-level exposure: which employees have compromised passwords, from which source, and with what recency. It answers the question of who is exposed and triggers credential hygiene remediation. Endpoint Threat Protection goes deeper into the device-level impact of infostealer infections specifically. When a device is infected, an infostealer exfiltrates not just credentials but also session cookies, browser autofill data, PII, device fingerprints, and the full inventory of every application accessed from that device. Endpoint Threat Protection surfaces the cookie count, application exposure scope, and PII from each infected device — the full blast radius of the infection rather than just the credential portion. Most security programs benefit from both. Workforce Threat Protection provides continuous credential hygiene across the entire workforce. Endpoint Threat Protection handles the deeper investigation and response when a specific infostealer infection is confirmed and the full scope of what was exfiltrated needs to be understood before remediation is complete.
SpyCloud’s data processing pipeline is designed to minimize the window between when stolen credentials appear in criminal sources and when security teams can act on them. Breach data and phishing captures are typically published in the SpyCloud platform within days of being recaptured from criminal sources. Infostealer malware logs, which circulate through more private criminal channels, are processed within hours to days of SpyCloud recapturing them. The practical effect is that security teams learn about employee credential exposures in the same timeframe that criminal operators are acquiring and testing that data — often before the data has been weaponized in a targeted attack. A financial services company using Workforce Threat Protection reported discovering anywhere from 3,000 to 11,000 direct credential matches per hour at peak. Each of those represents an account that could have led to account takeover before Workforce Threat Protection surfaced the exposure. The alternative — waiting for a breach notification that arrives weeks or months after the data has been in criminal hands — leaves an extended window during which attackers with access to the same data can test credentials against corporate login portals without any detection.