VIRTUAL EVENT
LIVE PRODUCT TOUR
IDENTITY THREAT PROTECTION
See how you can disrupt cybercrime in 15 minutes.
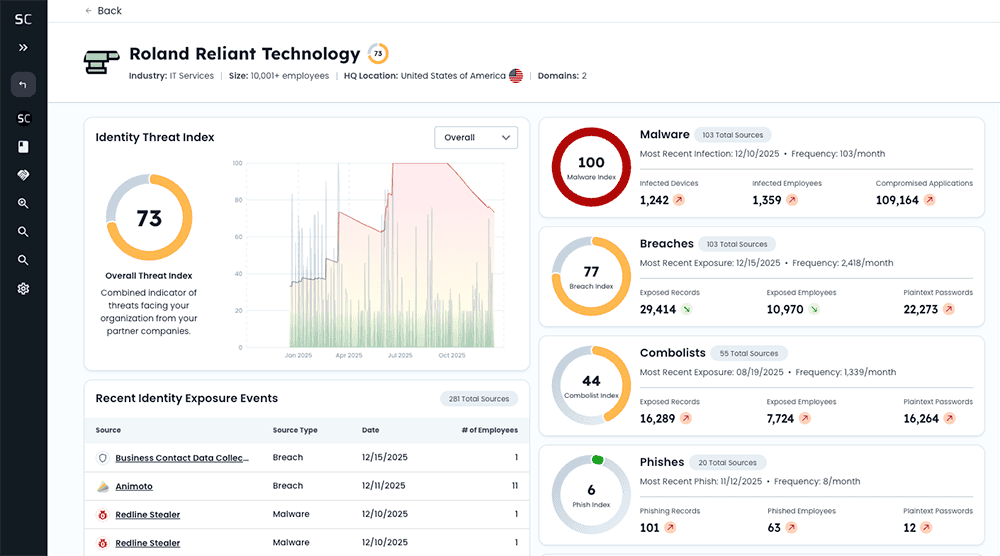
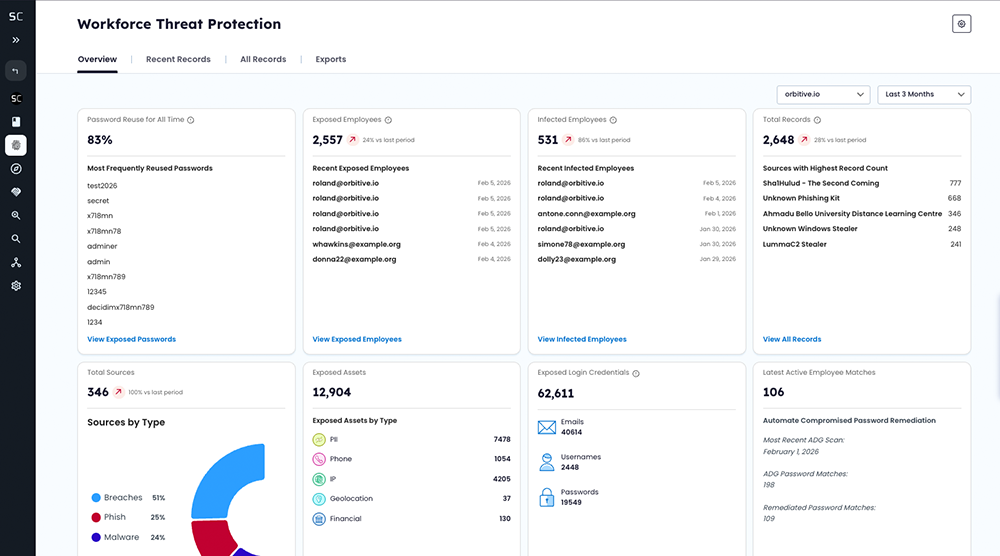
Stolen data from breaches, malware infections, combolists, and successful phishing campaigns fuels today’s most persistent identity-based threats. Protecting your workforce isn’t enough. Exposed credentials and malware-exfiltrated authentication data tied to endpoints and third-parties expand your attack surface.
Our bi-weekly live product tour series, Inside Identity Threat Protection, gives you a first-hand look at how to:
- Identify exposed identity data across your workforce, endpoints, and supply chain
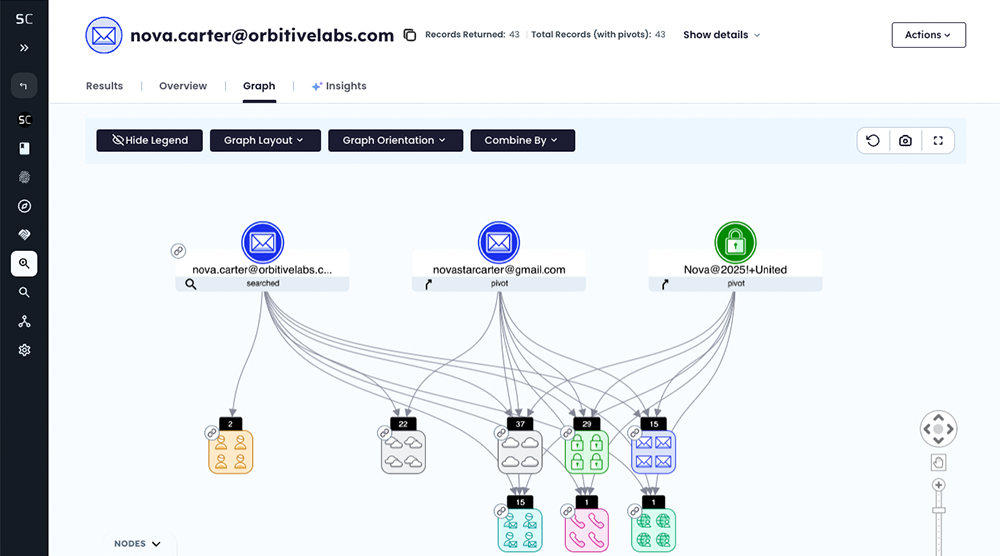
- Connect exposures to real attack paths
- Automate remediation to stop account takeover, ransomware, and follow-on attacks
- Conduct a more comprehensive cybercrime investigation from insider threat identification to financial fraud
Choose a session – or attend them all – and see how to stop identity threats before criminals act.
TRUSTED BY HUNDREDS OF GLOBAL INDUSTRY LEADERS