Phishing-as-a-Service (PhaaS) has emerged as one of the most significant evolutions in cybercrime infrastructure, enabling low-skill threat actors to deploy sophisticated phishing attacks with minimal technical expertise.
At the forefront of this trend is Tycoon 2FA (Storm-1747), a commercially distributed phishing kit first observed in August 2023 that is specifically engineered to defeat two-factor authentication (2FA) and multi-factor authentication (MFA) protections.
What is Tycoon 2FA? A phishing kit built to defeat MFA
Unlike traditional phishing tools that simply harvest usernames and passwords, Tycoon 2FA operates using an adversary-in-the-middle (AitM) approach. This means attackers host deceptive login pages through a reverse proxy that intercepts a victim’s interaction with legitimate services such as Microsoft 365 and Gmail. As the victim enters their credentials and MFA prompts, the kit relays this information to the real service while capturing sensitive authentication tokens – most notably session cookies – that can be replayed later to gain unauthorized access without re-entering MFA.
The PhaaS model used by Tycoon 2FA allows buyers to lease or subscribe to ready-to-use phishing infrastructure, often marketed on encrypted messaging platforms like Telegram. This lowers the barrier to entry for cybercriminals and broadens the pool of potential attackers beyond technically sophisticated actors.
What happened? The globally-coordinated takedown of Tycoon 2FA
SpyCloud Labs researchers have been monitoring Tycoon 2FA since its initial release, and released an in-depth analysis of both the Tycoon 2FA infrastructure and victimology after looking at over 150,000 phished credentials tied to Tycoon.
In early 2026, in coordination with Europol, Microsoft, and a coalition of private sector partners, including SpyCloud, authorities and partners executed a coordinated seizure of infrastructure and services supporting Tycoon 2FA. The operation was designed to disrupt the platform’s operational capabilities and reduce its capacity to harvest credentials and session data from victims globally.
As part of the joint disruption effort, SpyCloud provided victim intelligence to law enforcement partners to support notification efforts and contributed operational metrics to assist in identifying priority targets and measuring ecosystem impact.
At the time of the disruption, TrendAI reported that Tycoon 2FA had accumulated a user base of at least 2,000 operators and had leveraged more than 30,000 phishing domains. Based on SpyCloud’s data, during the time it was active, Tycoon 2FA harvested at least:
- 173K+ unique email addresses
- 67K usernames
- 264K passwords
These figures underscore both the scale of adoption and the operational maturity of the service prior to takedown.
Tycoon 2FA victimology
Since the first identified Tycoon 2FA record in August 2023, SpyCloud has identified 328,865 victim entries sourced from exposed Tycoon 2FA panels. These records contain email addresses, usernames, plaintext passwords, IP addresses, and associated country and device identifiers. The dataset reflects a globally distributed operation targeting enterprises across a broad range of sectors, including defense, manufacturing, insurance, and technology.
Tycoon’s primary targets are organizations and individuals using Microsoft 365 and Google Workspace accounts. These platforms are deeply embedded in enterprise environments and cloud ecosystems, making them high-value targets. Compromise of these accounts can enable lateral movement, data exfiltration, business email compromise (BEC), and serve as an initial access vector for ransomware operations.
Geographic analysis of victim log data indicates that the United States accounts for the largest concentration of identified victims (179,264), followed by the United Kingdom (16,901), Canada (15,272), India (7,832), and France (6,823). This distribution underscores the global scope of the campaign, with a pronounced emphasis on North American and Western European targets.
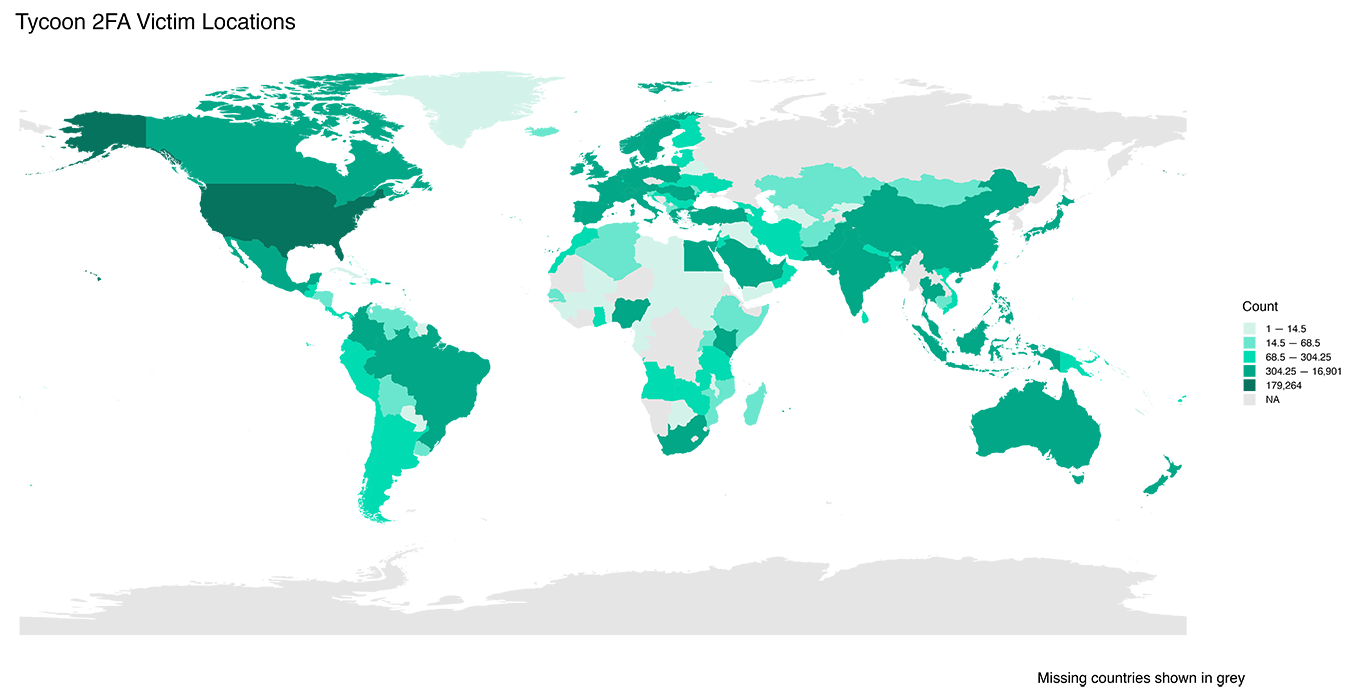
SpyCloud analysis of Tycoon 2FA Victim Impact by Location, Source: SpyCloud Labs
Analysis of victim email domains further clarifies the campaign’s enterprise focus. SpyCloud analysts compiled a reference list of 4,738 known free email provider domains (e.g., Gmail, Outlook, Hotmail) and compared it against domains observed in Tycoon 2FA victim records. Approximately 80% of victim email addresses did not match any domain within the freemail dataset.
This indicates that the overwhelming majority of targeted accounts were enterprise-managed or otherwise associated with paid domains, reinforcing the conclusion that Tycoon 2FA is primarily directed at business environments rather than individual consumer accounts.
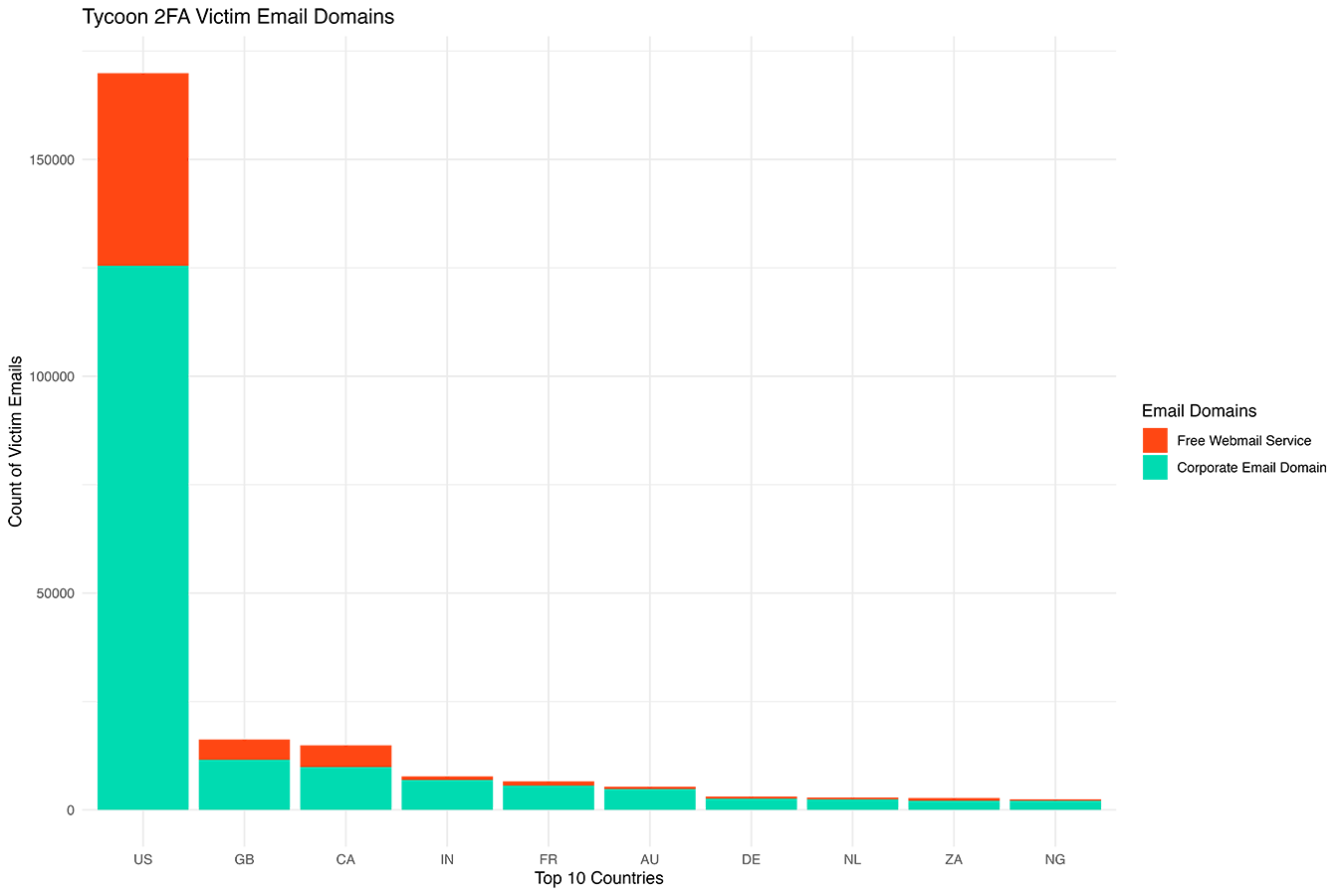
The number of victim emails by country split out into freemail and non-freemail domains, Source: SpyCloud Labs
Behind the curtain: Analyzing the threat actors’ obfuscation techniques
SpyCloud partnered with Spur, a leading IP intelligence company that specializes in identifying hidden infrastructure including VPNs, proxies, and anonymized services, to analyze login activity of users of Tycoon 2FA and better understand the operators behind the panel access.
The analysis shows that the overwhelming majority of logins originated from obfuscated infrastructure. Specifically, 75% of logins were attributed to residential proxy networks and 24% to VPN services. Only approximately 1% of login activity originated from IP addresses not associated with either form of obfuscation.
Residential proxy networks, while marketed for legitimate use cases, are frequently leveraged by threat actors to evade detection controls. These services enable operators to align their apparent geolocation with that of a target, facilitating the bypass of geolocation-based security controls and contributing to device fingerprint evasion strategies.
For AitM phishing frameworks such as Tycoon 2FA, geographic alignment is operationally significant. Threat actors must closely approximate the victim’s location to reduce the likelihood of triggering additional authentication challenges when replaying stolen credentials or session cookies.
When isolating IP addresses not associated with residential proxy infrastructure or known VPN services, login activity is concentrated primarily in Nigeria (211 logins) and South Africa (62 logins). Smaller volumes of activity were observed from the United States, Canada, Saudi Arabia, and Kenya.
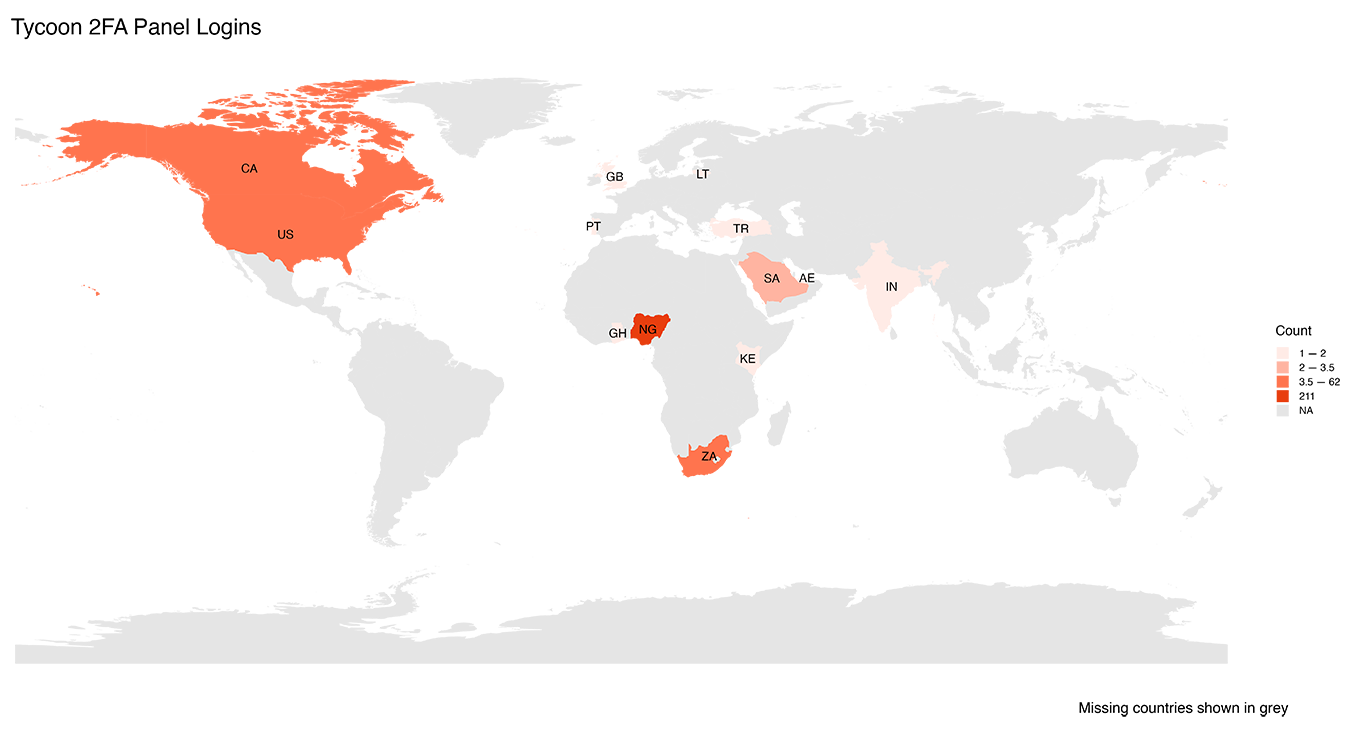
Tycoon 2FA panel log-in activity by location based on IP addresses not associated with either a residential proxy or VPN, Source: SpyCloud Labs
Enterprise impact: Tycoon 2FA victim analysis
SpyCloud identified 328,865 victim records sourced from exposed Tycoon 2FA administrative panels. These records included:
- Enterprise email addresses
- Plaintext passwords
- IP addresses
- Device metadata
- Country identifiers
Primary target platforms:
- Microsoft 365 accounts
- Google Workspace accounts
These cloud productivity environments are high-value enterprise targets because compromise enables:
- Lateral movement
- Data exfiltration
- Business email compromise (BEC)
- Initial ransomware access
Takeaways from the Tycoon takedown
Tycoon 2FA exemplified the increasing sophistication and commercialization of AitM phishing frameworks. Its large operator base, reliance on obfuscated infrastructure, and clear focus on enterprise-managed accounts demonstrated how effectively modern phishing kits can scale. The data underscores both the operational maturity of the platform and the real-world impact it had across global organizations.
The coordinated disruption led by Europol, Microsoft, and private sector partners represents a meaningful blow to that ecosystem. Seizing infrastructure, degrading service availability, and enabling victim notification efforts directly reduces harm and raises the operational cost for threat actors. Targeting not just individual operators, but the enabling platform itself, signals a maturing approach to ecosystem-level disruption.
While AitM techniques will persist, this operation demonstrates that coordinated public-private action can materially impact the threat landscape. By combining infrastructure intelligence, victim telemetry, and law enforcement authority, defenders can impose friction on criminal service models that depend on scale and reliability.
Sustained collaboration will be critical. Continued monitoring for exposed credentials, adoption of phishing-resistant authentication mechanisms, and rapid intelligence sharing remain essential. But it can not be overstated, well-coordinated defensive action can measurably reduce criminal capability and shift the economics of cybercrime in favor of defenders.
What organizations should do after an MFA-bypassing phishing campaign
Even after infrastructure takedowns, exposed credentials and session tokens remain exploitable. Organizations should:
- Monitor for exposed enterprise credentials in criminal ecosystems
- Invalidate active session cookies when compromise is suspected
- Deploy phishing-resistant authentication methods (FIDO2, hardware tokens)
- Implement continuous credential exposure monitoring
- Monitor for anomalous login geography and proxy abuse
Tycoon 2FA demonstrates that traditional MFA alone is not sufficient against modern phishing kits.
Acknowledgements
Thanks to Microsoft and Europol for driving this operation, and for the support of private industry partners including Cloudflare, Coinbase, Crowell & Moring, eSentire, Health-ISAC, Intel471, Proofpoint, Resecurity, The ShadowServer Foundation, and TrendAI.
Discover what cybercriminals know about your business and your customers – and how those insights help you protect digital identities and prevent targeted attacks.
FAQs
Tycoon 2FA uses a reverse proxy infrastructure to intercept authentication sessions between victims and legitimate services like Microsoft 365 and Google Workspace. When users enter credentials and approve MFA prompts, the kit harvests authentication tokens and session cookies, which attackers can replay to gain unauthorized access without re-authenticating.
Tycoon 2FA primarily targeted enterprise-managed accounts, particularly Microsoft 365 and Google Workspace users. Analysis of victim data shows that the majority of compromised email addresses were associated with corporate domains rather than freemail providers, indicating a strong focus on business environments.
Organizations should adopt phishing-resistant authentication methods such as FIDO2 or hardware-based security keys, continuously monitor for exposed credentials and session cookies in criminal ecosystems, invalidate exposed session tokens, and detect anomalous login activity involving residential proxies or VPN infrastructure. MFA alone is not sufficient protection against modern adversary-in-the-middle phishing frameworks.