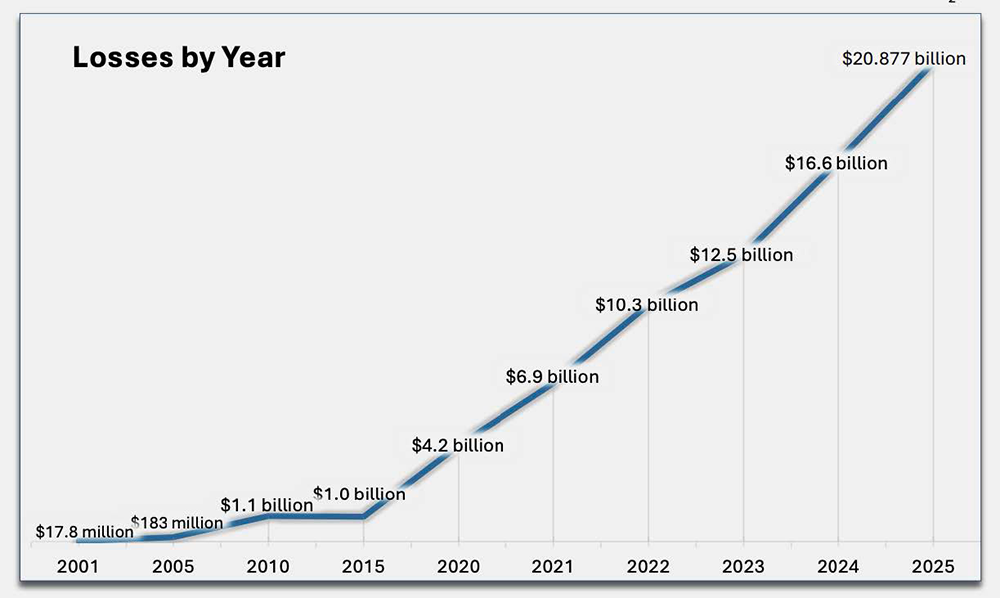
Cybercrime losses jumped by 26% year-over-year, grossing more than $20 billion for the first time, according to the FBI Internet Crime Report 2025 – an analysis of last year’s cybercrime trends, impacts, and losses published in April 2026.
In its 26th edition, the FBI IC3 report showed record-breaking losses, the official debut of AI-driven complaints and losses, and a threat landscape growing even more sophisticated – but at 60+ pages, you might not have the time to comb through it all.
At SpyCloud, we analyzed the report to provide you and your security team with the most important trends and data points to better protect your organization against account takeover, ransomware, and other identity-driven attacks as we make our way through 2026.
Here’s what stood out:
TL;DR
- Total cybercrime complaints received by the FBI increased by 17.3% to over 1 million per year and 3,000 per day.
- Overall, cybercrime losses by year are on the rise, escalating from $16.6B to over $20.9B from 2024 to 2025, with phishing losses escalating from $70M to $215.8M.
- The FBI saw an increased number of account takeover-related incidents last year, underscoring SpyCloud’s previous reporting on this pervasive threat.
- Both financial fraud and employment fraud also drove billions in losses, with the DPRK remote worker scams making a notable impact.
- AI-related cybercrime was noted in the report for the first time ever, with 22,000 complaints and nearly $900M in associated losses.
Let’s dig into the trends behind the numbers.
Phishing losses jumped by 3x, indicating the growth of sophisticated campaigns
Phishing is still the front door for bad actors with the highest number of complaints and significant jump in losses, signaling that campaigns are becoming more sophisticated and targeted.
According to the FBI IC3 report, complaints slightly decreased from 193,407 in 2024 to 191,561 in 2025, while the losses from phishing attacks escalated from $70M to $215.8M. This jump is likely due to the fact that cybercriminals are modernizing their tactics and scaling their attacks with phishing-as-a-service (PhaaS) platforms and AI.
SpyCloud has seen this sophistication firsthand. PhaaS platforms give less technically skilled criminals access to turnkey kits that can capture session cookies, 2FA codes, and other sensitive identity data that allows attackers to launch follow-on attacks.
The SpyCloud 2026 Annual Identity Exposure Report showed 28.6 million phished identity records recaptured in 2025. Almost half of the victims were corporate users (49%), demonstrating that enterprise security controls alone are not preventing identity compromise.
“The spike in losses we see in the report is not surprising. Flat complaint volume with disproportionately large losses tells you attackers are getting more precise – but there’s a larger problem that this data doesn’t show.
Phishing is a pervasive initial access mechanism and the reported complaints don’t show how phished credentials and session cookies then fuel account takeover, BEC, session hijacking, and ransomware. The complaint count is only the tip of the spear.”
While the IC3 report counts crime after it happens, SpyCloud data surfaces targeted and successfully phished data circulating the criminal underground before crimes occur to help organizations prevent what too often happens next.
Account takeover: A hidden engine behind the numbers
Account takeover was called out as a growing threat for the first time ever in the report, with 4,700 complaints and $359.7 million in losses, acknowledging what we at SpyCloud have long labeled as a hard-hitting threat for organizations across all sectors.
IC3 also flagged the unique complexity of account takeover crimes with some cases involving more than 50 simultaneous ACH transactions across multiple banks. This level of complexity makes it extremely hard to recover funds, which is why account takeover prevention is so important.
But that $359.7 million figure is only part of the story.
Account takeover is frequently the mechanism behind the fraud types in the IC3 report. When a business email is compromised, an investment account is drained, or a tech support scammer gains access to a victim’s finances, compromised credentials or stolen session data are often what opened the door in the first place.
Business email compromise losses continue to grow
Business email compromise (BEC) is the #2 crime type by total financial losses listed in the report, with $3.04 billion lost in 2025 over $2.77 billion the year before, making BEC a high-dollar threat that shows no sign of leveling off.
It’s also important to note that 86% of BEC losses were transmitted via wire transfer or ACH, making them fast-moving and often unrecoverable by the time fraud is detected.
The threat is also evolving: the report flags AI as an emerging enabler of BEC schemes, with chat generators mimicking executives and voice cloning being used to authorize fraudulent transfers. Businesses reported over $30 million in AI-enabled BEC losses alone.
And while BEC continues to grow, it’s no longer the only fraud type moving serious money. The FBI’s fund-recovery team noted that tech support and account takeover scams are now triggering emergency fund-freeze requests at a rate that rivals BEC – a sign that high-dollar fraud is spreading across more attack types, not just concentrating in one.
Financial and employment fraud drives billions in losses
The report highlights fraud as one of the most costly and wide-ranging threat categories, spanning everything from investment scams to a new breed of employment deception.
On the financial side, investment fraud and BEC topped the loss charts at $8.6 billion and $3 billion respectively, while account takeover, tech support scams, and government impersonation collectively drove hundreds of millions more in losses.
The report also calls out employment fraud, spotlighting a threat SpyCloud has been actively tracking: DPRK remote worker scams. North Korean state-sponsored IT workers are using stolen or fabricated identities to secure remote positions at U.S. companies. SpyCloud’s own research found DPRK IT workers inadvertently infecting their machines with infostealer malware – exposing fake personas, reused passwords, and other tactics to investigators and revealing that nearly every Fortune 500 company has interacted with and potentially hired at least one of these operatives.
SpyCloud’s insider threat detection and fraud prevention capabilities are built to interrupt that chain early, surfacing compromised identity data from the criminal underground before it can be weaponized for account takeover, synthetic identity fraud, or fraudulent transactions.
New ransomware variants identified across several industries
The report also identified 63 new ransomware variants, affecting three sectors the most significantly: critical manufacturing, healthcare, and government facilities.
Ransomware complaints grew steadily but the reported loss figure jumped dramatically by 159% to $32.3M. This number is significantly underreported, though, as entities frequently do not report financial losses from ransomware to the FBI.
The report also found that the top ransomware variants shifted: while Akira remained #1, new entrants include Qilin (#2) and INC./Lynx/Sinobi (#3), replacing LockBit and RansomHub from the top of the 2024 list.
AI-related cybercrime makes its debut, with $900 million in losses
The report also introduced “AI-related” as a formal crime descriptor for the first time ever, with over 22,000 complaints and nearly $900 million in associated losses.
The biggest AI-related loss category was investment fraud at $632M, followed by BEC ($30M) and tech support ($19.5M). According to the report, and as you likely already know, AI is being used to generate deepfakes, clone voices, mass-produce phishing content, and create fake social media profiles at scale.
It’s important to note that AI isn’t necessarily changing the types of crimes – it’s scaling them. Criminals are using AI to automate phishing campaigns, generate convincing deepfake lures, and make social engineering faster and more targeted.
What’s missing from the report
The FBI’s IC3 report is an important annual benchmark in cybersecurity as it documents the damage of cybercrime: the complaints, the losses, and the trends.
But, by definition, it counts crime after it happens.
What it doesn’t show is what made those crimes possible in the first place – how many credentials circulated on the darknet before those accounts were taken over, how many infostealer infections quietly siphoned session cookies in the background, or how many breached passwords were reused across multiple accounts.
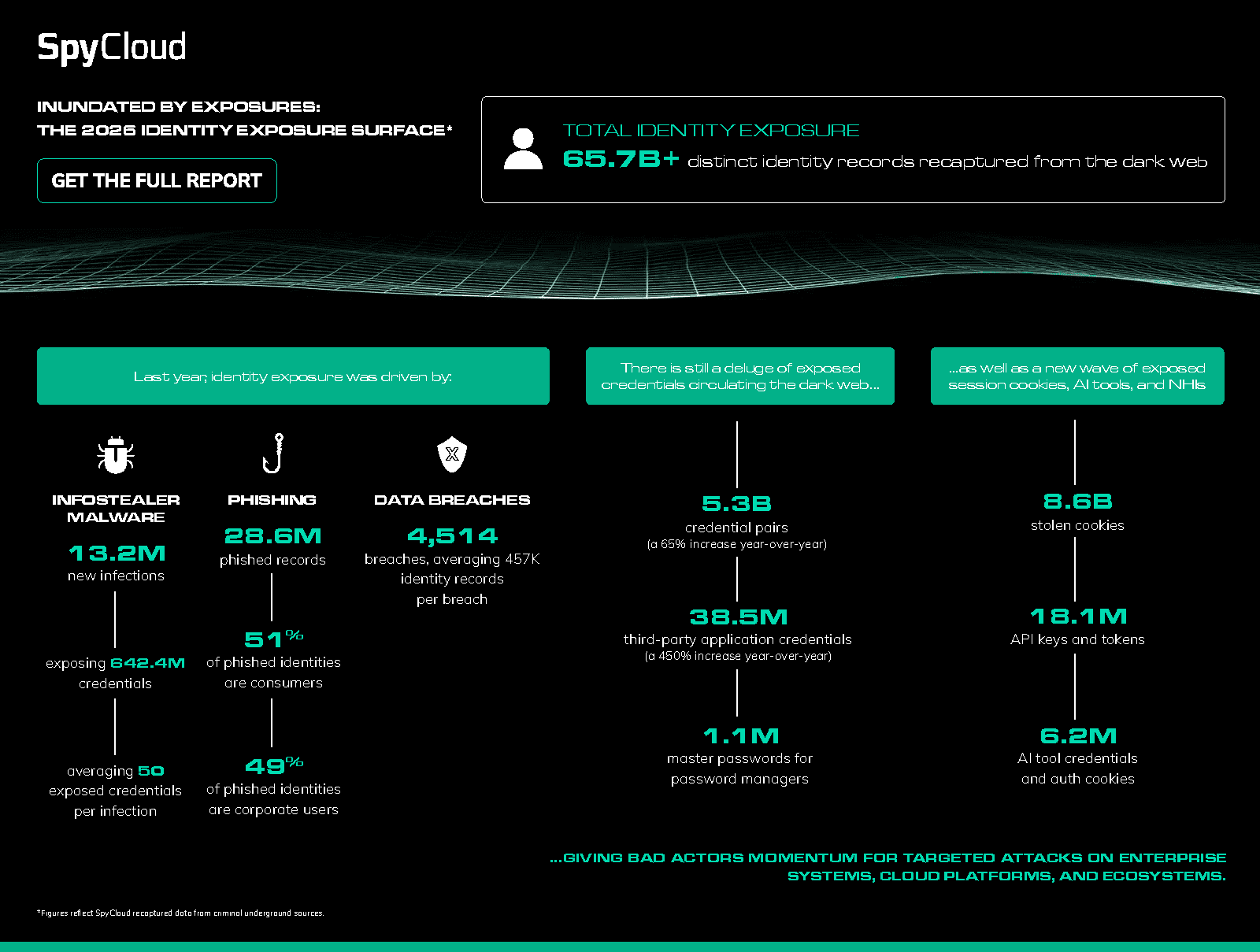
That’s where SpyCloud’s data come in. Our data gives us visibility into the entire identity behind an exposure and is backed by 950B+ total identity assets, including 65.7B + distinct identity records, a 23% increase over 2025. These stolen credentials, PII, session cookies, and other identity data are the raw material powering the crimes IC3 counts.
The current identity exposure landscape, based on SpyCloud’s recaptured data from criminal underground sources.
SpyCloud’s automated identity threat protection solutions are built to interrupt that chain before it becomes a statistic by detecting exposures before criminals can act.
Whether it’s preventing account takeover at the identity layer, remediating exposed employee credentials before they enable a BEC attack, or cutting off the potential for an initial foothold that leads to ransomware, the goal is the same: act on the exposure intelligence before more significant damage is done.
Learn more about identity data-related incidents in the SpyCloud 2026 Identity Exposure Report.
FAQs
The 2025 FBI Internet Crime Report recorded over $20.9 billion in cybercrime losses – a 26% increase year-over-year and the first time losses have surpassed $20 billion. Key findings include a tripling of phishing losses to $215.8M, $3.04B in BEC losses, the first-ever reporting of AI-related cybercrime (22,000+ complaints, ~$900M in losses), and a new callout of account takeover as a growing standalone threat category with $359.7M in reported losses.
Phishing complaints to the FBI actually decreased slightly in 2025, but financial losses tripled – from $70M to $215.8M. This divergence signals that attacks are becoming more targeted and effective, not just more frequent. Cybercriminals are increasingly using phishing-as-a-service (PhaaS) platforms and AI to capture session cookies, 2FA codes, and credentials at scale, enabling high-value follow-on attacks like account takeover, BEC, and ransomware that compound the financial damage far beyond the initial phish.
Account takeover is often the mechanism behind the fraud types the IC3 report tracks separately. When business email is compromised, investment accounts are drained, or tech support scams succeed, it frequently traces back to stolen credentials or hijacked session cookies enabling the initial access. The FBI acknowledged ATO as a growing threat for the first time in the 2025 report, but the $359.7M in direct ATO losses significantly understates its true impact as an enabler of broader fraud categories across the report.
The 2025 FBI IC3 report introduced “AI-related” as a formal crime descriptor for the first time, logging over 22,000 complaints and nearly $900M in losses. The largest AI-related loss category was investment fraud at $632M, followed by BEC at $30M and tech support scams at $19.5M. Criminals are using AI to generate deepfakes, clone voices, mass-produce phishing content, and automate social engineering – not fundamentally changing crime types, but dramatically scaling their reach and precision.
The IC3 report measures cybercrime after it happens – complaints filed, losses reported. It doesn’t capture the upstream identity exposure that made those crimes possible: the stolen credentials circulating on the criminal underground, the infostealer infections quietly harvesting session cookies, or the breached passwords being reused across corporate accounts. SpyCloud recaptures this data from the criminal underground before it’s weaponized – providing security teams with the ability to act on identity exposure intelligence early, before it becomes a statistic in next year’s IC3 report.