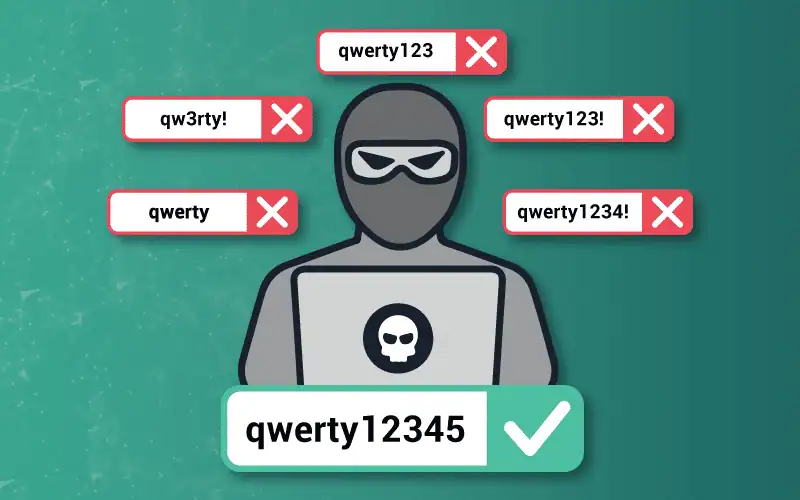
Credential Stuffing vs Password Spraying: Understanding the Key Differences
Dig into the differences between these two common attack types, and how you can prevent account takeovers that stem from either one.
Dig into the differences between these two common attack types, and how you can prevent account takeovers that stem from either one.
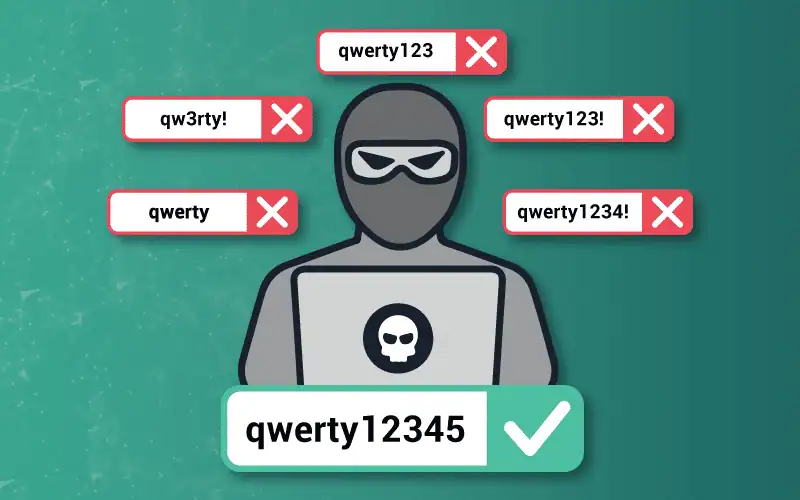
Get the lowdown on botnets, networks of computers infected by malware. See why they’re dangerous and how to protect yourself.

Increased adoption of MFA is a good thing for cybersecurity, especially as remote work grows in popularity – and preference – but humans remain the weakest link.

MFA keeping you up at night? It probably should. Check out these common MFA bypass techniques and why another layer of account protection is necessary.
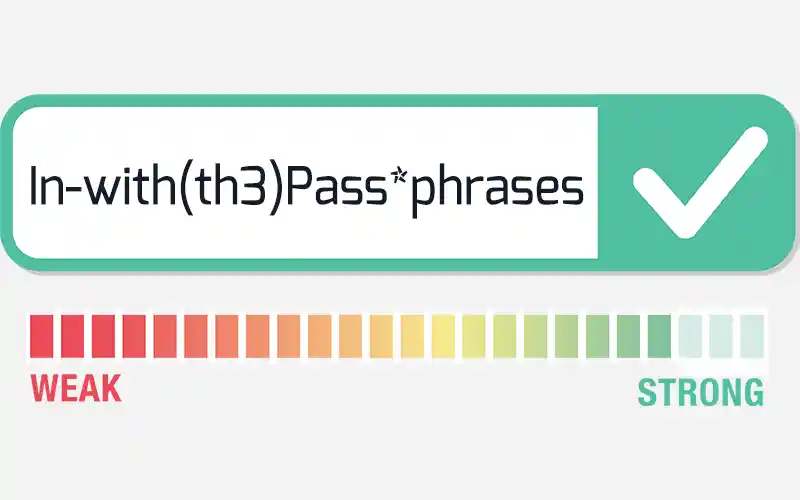
Many years’ worth of accumulated best practices have mostly helped strengthen Active Directory security, but a few long-standing beliefs about enforcing password policies are actually outdated.