Splunk
SpyCloud’s integration with Splunk delivers end-to-end visibility of an organization’s breach, malware, and phishing exposures and the information necessary to take action quickly – reducing the risk that stolen authentication data results in breaches, account takeover, ransomware, or online fraud.
The SpyCloud API unlocks a holistic view of exposed workforce data in one centralized location, dramatically increasing attack surface visibility and decreasing discovery and remediation times. In addition, security teams can now leverage SpyCloud’s robust repository of 425+ billion assets recaptured from the criminal underground to investigate the sources of true sources of digital compromise and make more informed decisions to mitigate their risk of cybercrime.
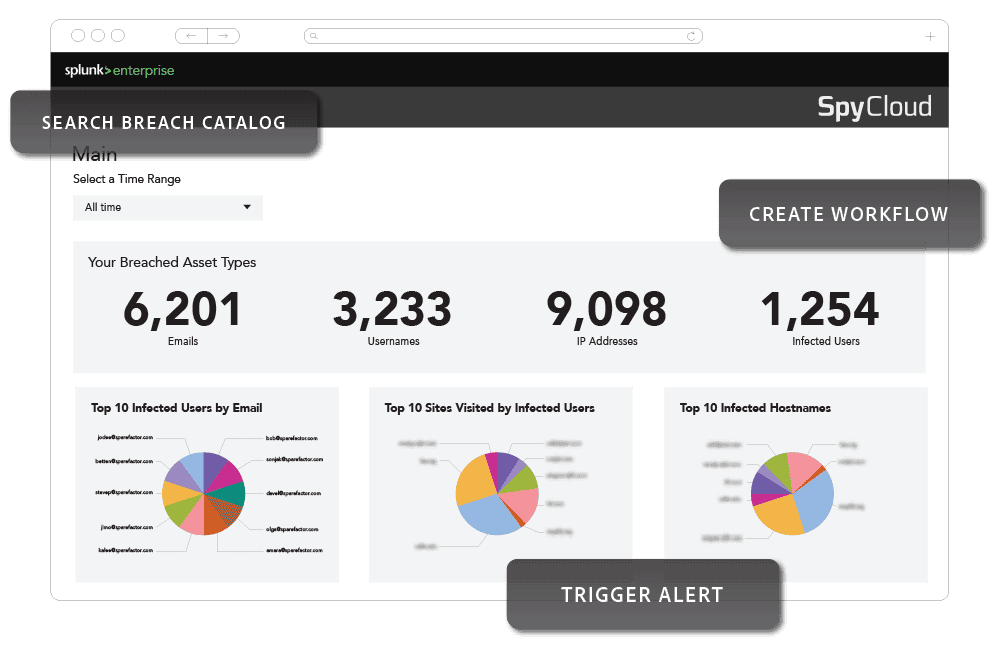
The SpyCloud Add-On and Application for Splunk ingests recaptured data directly into your environment – no manual pulls required.
Automated ingestion of exposed identity data that matches your custom watchlist (domain, email, and IP address), and a customizable schedule can power dashboard and trigger alerts.
Built for threat hunters and cyber threat analysts, this App adds advanced cybercrime investigation capabilities directly into Splunk to de-anonymize threat actors and accelerate attribution.
An interactive UI offers flexible searching and deep dive into SpyCloud data, along with custom search commands to query SpyCloud data within Splunk.
-
Visualize exposure trends
Monitor compromised credentials, cookies, and malware infections with out-of-the-box dashboards built for SOC workflows -
Detect and respond to identity-based threats
Correlate SpyCloud identity data with internal logs and alerts to detect risks early and drive faster response -
Accelerate investigations
Enrich detections with detailed identity context, like infection source and password reuse, for faster answers
Spend time on actionable alerts, prioritizing the highest severity malware exposures affecting critical workforce applications.
- Query SpyCloud’s recaptured data for exposures related to your domain(s) for specific time windows
- Automatically generate tickets to resolve breached and malware-exfiltrated credentials
- Reset fuzzy/variation matches that are easily guessed by criminals
- Get alerts when users have remediated their exposed AD passwords