Elastic
SIEM
OVERVIEW
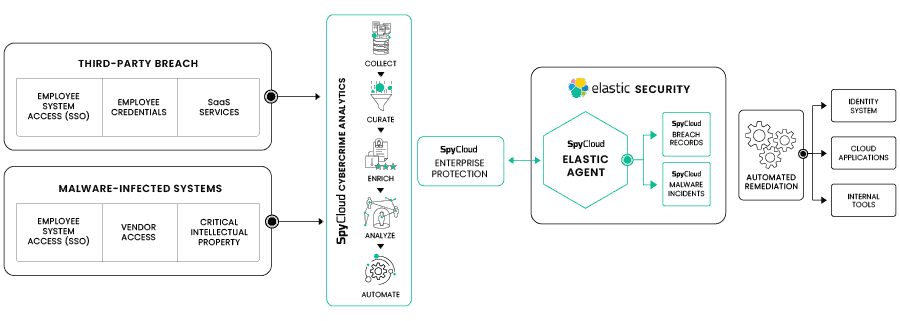
SpyCloud integrates with Elastic to deliver identity exposure intelligence directly into SIEM workflows. Security teams can correlate exposed credentials and malware-related identity risk with log and event data for faster detection and response.
BENEFITS
-
Native Elastic Integration
Seamlessly ingest SpyCloud breach, malware, and phishing exposure data into Elastic Security for unified analysis. -
Enhanced Threat Detection
Improve visibility into exposed identities and risk signals that often precede account takeover and targeted attacks. -
Operational Efficiency
Leverage Elastic’s alerting, dashboards, and analytics capabilities to drive investigation and response directly within your existing SIEM workflows. -
Customizable Visualization
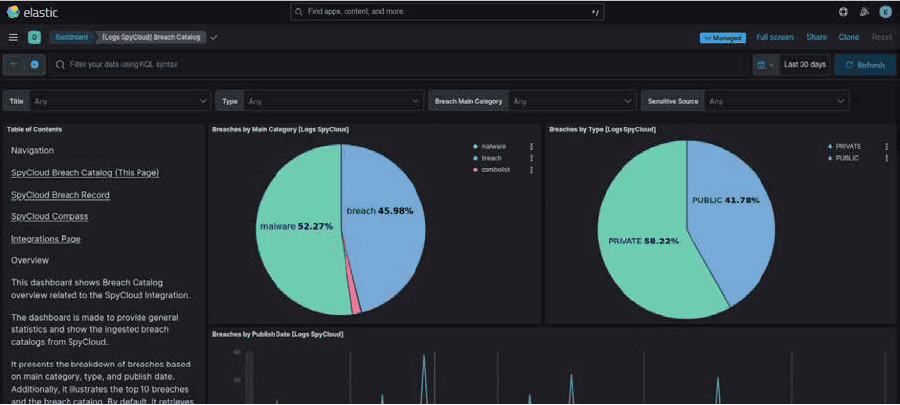
Use pre‑built dashboards or tailor visualizations to track exposure trends, compromised assets, and priority threat indicators.
SEE IT IN ACTION
HOW IT WORKS
- Scheduled Ingestion: SpyCloud Enterprise Protection performs a scheduled ingest of exposure records (from phishing attacks, infostealer malware infections, breaches and combolist) via REST API into your Elastic environment.
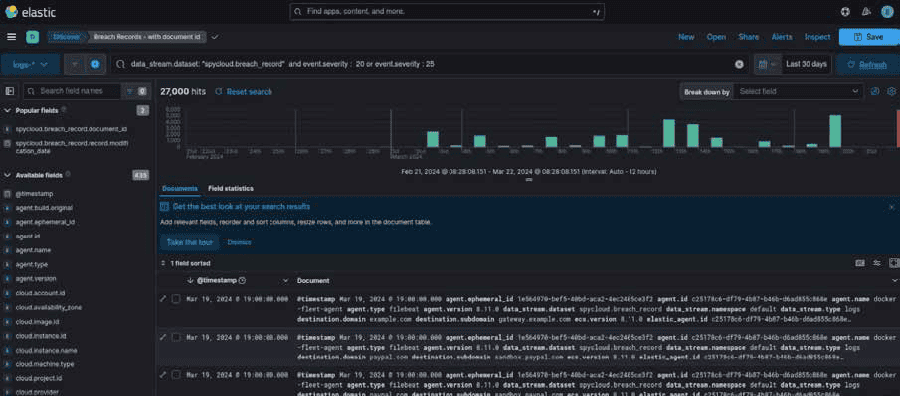
- Index and Store: Data is normalized and indexed into Elastic indices, enabling efficient search, correlation, and threat hunting.
- Detect & Alert: Use Elastic alerting rules to trigger on new or high‑risk exposures (e.g., compromised credentials, infected sessions), helping security teams find and respond to issues faster.
- Analyze & Visualize: Leverage Elastic dashboards and queries to investigate exposures in context alongside other security telemetry, gaining deeper insight into identity‑based threats.
- Automate Response: Optional handoff to SOAR platforms enables automated incident response actions, like forcing password resets, revoking sessions, or notifying user based on SpyCloud exposure signals.